The U.S. Department of Justice (DoJ) on Wednesday indicted three suspected North Korean hackers for allegedly conspiring to steal and extort about $1.3 billion in dollars and cryptocurrencies from money establishments and organizations.
The 3 defendants — Jon Chang Hyok, Kim Il, and Park Jin Hyok — are claimed to be members of the Reconnaissance Typical Bureau, a military intelligence division of North Korea, also identified as the Lazarus group, Concealed Cobra, or Superior Persistent Risk 38 (APT 38).
Accusing them of creating and deploying numerous malicious cryptocurrency applications, establishing and fraudulently marketing and advertising a blockchain platform, the indictment expands on the 2018 prices brought from Park, a single of the alleged nation-point out hackers earlier billed in link with the 2014 cyberattack on Sony Images Entertainment.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
A Wide-Ranging Scheme to Dedicate Cyberattacks and Monetary Crimes
“North Korea’s operatives, utilizing keyboards fairly than guns, stealing electronic wallets of cryptocurrency in its place of sacks of dollars, are the world’s main bank robbers,” stated Assistant Lawyer Common John C. Demers of the Justice Department’s Nationwide Security Division.

“The Division will proceed to confront malicious nation point out cyber activity with our distinctive instruments and get the job done with our fellow businesses and the loved ones of norms abiding nations to do the very same.”
The latest indictment is however yet another signal of how the Lazarus Team depends on cyber cryptocurrency heists and cybertheft versus businesses and critical infrastructure in purchase to fund a country that’s been heavily strike by financial sanctions.
The group, which gained a area in the U.S. government’s sanctions checklist in 2019, has been linked into a vast array of criminal cyber things to do, both of those in the U.S. and abroad, like the damaging WannaCry ransomware outbreak of 2017, the SWIFT attacks on banking institutions and ATM networks to steal additional than $1.2 billion, conducting spear-phishing strategies, and carrying out cryptocurrency thefts amounting to at minimum $112 million.
Curiously, the indictment also aspects the defendants’ plans to build their personal crypto-token called Marine Chain in 2017-18, which would let buyers purchase stakes in delivery vessels, but in truth, was a funds-generating initiative aimed at secretly obtaining resources for the authorities while evading international sanctions.
“AppleJeus” Backdoor to Steal Cryptocurrency
Also undertaken by the conspiracy is a scheme that included creating malicious purposes that masqueraded as reputable cryptocurrency buying and selling platforms, only to use them as a backdoor to transfer revenue to their accounts fraudulently.
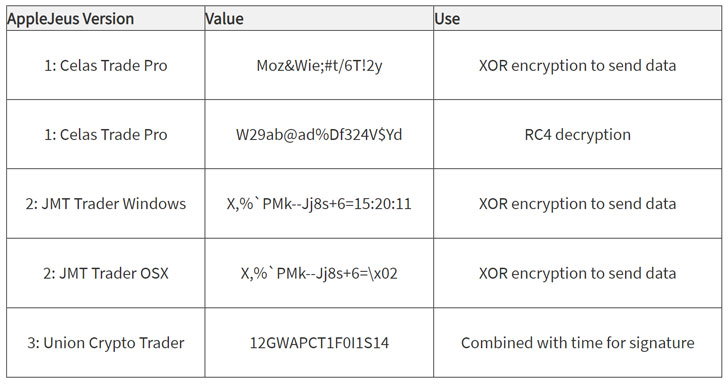
Contacting the backdoor “AppleJeus,” the U.S. Cybersecurity and Infrastructure Security Company (CISA) claimed it discovered at minimum 7 unique variations of the malware considering the fact that 2018, with the Lazarus Group banking on a combine of phishing, social networking, and social engineering tactics as original an infection vectors to trick users into downloading it.
The rogue applications discovered by CISA includes of Ants2Whale, Celas Trade Pro, CoinGo Trade, CryptoNeuro Trader, Dorusio, iCryptoFx, Kupay Wallet, Union Crypto Trader, and WorldBit-Bot.
Energy, finance, governing administration, sector, technology, and telecommunications sectors have been the prominent aim of the attacks, the company in depth, incorporating AppleJeus targets both of those Windows and Mac functioning methods, echoing a prior August 2018 report from cybersecurity organization Kaspersky.
Canadian-American Citizen Billed for Revenue Laundering
U.S. prosecutors reported the a few males ended up stationed by the North Korean govt in other nations around the world this sort of as China and Russia with the intention of furthering the strategic and money interests of the Kim Jong Un-led regime. The DoJ, having said that, did not elaborate on regardless of whether risk actors from possibly region collaborated with the North Korean operatives on these attacks.
In a linked development, the U.S. Federal Bureau of Investigation (FBI) attained warrants to seize cryptocurrencies totaling about $1.9 million that ended up allegedly plundered from an unnamed money companies firm in New York and held at two cryptocurrency exchanges.
A second case that was also unsealed yesterday involved a Canadian-American citizen named Ghaleb Alaumary, who pled responsible in a dollars-laundering scheme and admitted to carrying out ATM “hard cash-out” operations and a cyber-enabled bank heist orchestrated by North Korean hackers.
Despite the fact that the folks are not likely to be extradited and introduced to demo, Jon, Kim, and Park are charged with one particular count of conspiracy to commit computer system fraud and abuse and 1 rely of conspiracy to commit wire fraud and bank fraud. Alaumary has been charged with a person count of conspiracy to commit money laundering, which carries a highest sentence of 20 several years in jail.
“The scope of the legal perform by the North Korean hackers was considerable and extended-running, and the array of crimes they have dedicated is staggering,” said Acting U.S. Lawyer Tracy L. Wilkison for the Central District of California. “The perform specific in the indictment are the acts of a legal nation-condition that has stopped at absolutely nothing to extract revenge and get hold of money to prop up its regime.”
Observed this write-up appealing? Adhere to THN on Facebook, Twitter and LinkedIn to study extra exceptional articles we write-up.
Some areas of this write-up are sourced from:
thehackernews.com


 NIST hints at upgrades to its system for scoring a phish’s deceptiveness
NIST hints at upgrades to its system for scoring a phish’s deceptiveness