The U.S. govt on Thursday produced a cybersecurity advisory outlining multiple intrusion strategies performed by point out-sponsored Russian cyber actors from 2011 to 2018 that qualified the electrical power sector in the U.S. and further than.
“The [Federal Security Service] conducted a multi-stage campaign in which they attained distant accessibility to U.S. and global Vitality Sector networks, deployed ICS-centered malware, and collected and exfiltrated organization and ICS-related data,” the U.S. governing administration mentioned, attributing the attacks to an APT actor recognised as Energetic Bear.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
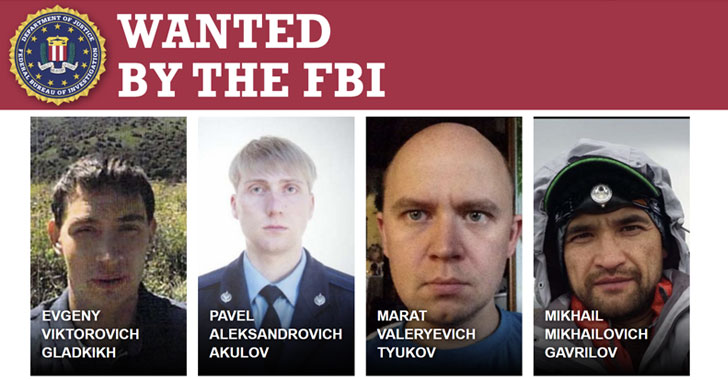
In addition, the Justice Division billed four Russian federal government workforce, which include three officers of the Russian Federal Security Provider and a laptop programmer at the Central Scientific Study Institute of Chemistry and Mechanics (TsNIIKhM), for their roles in carrying out the attacks on oil refineries, nuclear services, and vitality providers.
The four Russian nationals are Pavel Aleksandrovich Akulov(36), Mikhail Mikhailovich Gavrilov (42), and Marat Valeryevich Tyukov (39), and Evgeny Viktorovich Gladkikh (36).
The seven-calendar year-lengthy world-wide energy sector marketing campaign is said to have taken gain of spear-phishing emails, trojanized program updates, and redirects to rogue web sites (aka watering holes) to get original obtain, utilizing it to deploy distant entry trojans like Havex on compromised devices.
Also comprehensive by the security businesses is a 2017 marketing campaign engineered by cyber actors with ties to TsNIIKhM with the intention of manipulating the industrial management devices of an unnamed oil refinery found in the Middle East by leveraging a piece of malware named TRITON.
“TRITON was developed to exclusively concentrate on Schneider Electric’s Triconex Tricon security techniques and is capable of disrupting those methods,” the Cybersecurity and Infrastructure Security Agency (CISA), the Federal Bureau of Investigation (FBI), and the Section of Power (DOE) said.
Collectively, the hacking campaigns are alleged to have singled out thousands of computers, at hundreds of organizations and organizations, in about 135 nations, the FBI explained.
“The potential of cyberattacks to disrupt, if not paralyze, the delivery of critical power expert services to hospitals, homes, businesses and other destinations critical to sustaining our communities is a truth in today’s planet,” stated U.S. Attorney Duston Slinkard for the District of Kansas. “We should acknowledge there are men and women actively seeking to wreak havoc on our nation’s critical infrastructure method, and we should stay vigilant in our effort and hard work to thwart this kind of attacks.”
Uncovered this write-up appealing? Observe THN on Fb, Twitter and LinkedIn to go through far more special content material we article.
Some parts of this report are sourced from:
thehackernews.com


 EU and US reach agreement on Privacy Shield replacement
EU and US reach agreement on Privacy Shield replacement