The US govt on Monday formally charged 6 Russian intelligence officers for carrying out damaging malware attacks with an aim to disrupt and destabilize other nations and result in monetary losses.
The folks, who perform for Device 74455 of the Russian Key Intelligence Directorate (GRU), have been accused of perpetrating the “most disruptive and damaging series of laptop attacks ever attributed to a single team,” according to the Justice Section (DoJ).
All the six men — Yuriy Sergeyevich Andrienko, Sergey Vladimirovich Detistov, Pavel Valeryevich Frolov, Anatoliy Sergeyevich Kovalev, Artem Valeryevich Ochichenko, and Petr Nikolayevich Pliskin — have been charged with seven counts of conspiracy to carry out laptop or computer fraud and abuse, conspiracy to commit wire fraud, wire fraud, harmful safeguarded personal computers, and aggravated identity theft.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“The item of the conspiracy was to deploy harmful malware and acquire other disruptive actions, for the strategic reward of Russia, by unauthorized access (‘hacking’) of target personal computers,” the prosecutors claimed.
“In furtherance of the conspiracy, Andrienko, Detistov, Frolov, Kovalev, Ochichenko, Pliskin, and other folks recognized and mysterious to the grand jury procured, managed, and utilized servers, email accounts, destructive cellular apps, and similar hacking infrastructure to interact in spear-phishing campaigns and other network intrusion strategies versus pcs applied by the victims.”
5 many years ago, Russian hackers belonging to Sandworm (aka APT28, Telebots, Voodoo Bear or Iron Viking) team attacked Ukraine’s electricity grid, Ministry of Finance, and State Treasury Support applying malware such as BlackEnergy, Industroyer, and KillDisk, before embarking on a spree of damaging cyberattacks — like unleashing NotPetya in 2017 and targeting the Pyeongchang Winter season Olympics with phishing strategies and “Olympic Destroyer” malware.
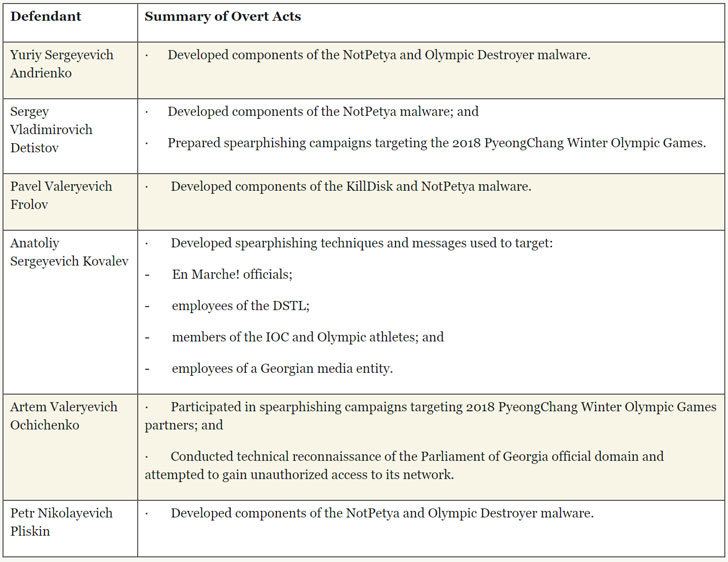
The 6 folks have been accused of establishing elements for NotPetya, Olympic Destroyer, KillDisk malware, as very well as planning spear-phishing strategies directed versus the 2018 PyeongChang Wintertime Olympic Online games, resulting in damage and disruption to computer system networks across France, Ga, the Netherlands, Republic of Korea, Ukraine, the Uk, and the US.
“For example, the NotPetya malware impaired Heritage Valley’s provision of critical medical providers to citizens of the Western District of Pennsylvania by way of its two hospitals, 60 workplaces, and 18 group satellite facilities,” the DoJ said. “The attack triggered the unavailability of patient lists, patient history, physical examination files, and laboratory documents.”
“Heritage Valley misplaced accessibility to its mission-critical personal computer methods (these types of as people relating to cardiology, nuclear medication, radiology, and surgical procedures) for about one particular week and administrative laptop or computer methods for virtually one month, thus resulting in a threat to general public health and fitness and protection,” it additional.
The whole damages introduced about by NotPetya is pegged to far more than $10 billion to day, crippling several multinational organizations like Maersk, Merck, FedEx’s TNT Categorical, Saint-Gobain, Mondelēz, and Reckitt Benckiser.
In a similar development, the Uk federal government also formally accused the GRU of perpetrating cyber reconnaissance from officers and businesses at the 2020 Tokyo Olympic and Paralympic Games before this summer just before they had been postponed up coming year owing to COVID-19.
This is not the first time GRU has appear less than the DoJ scanner. Two decades again, the US federal government billed seven officers operating for the army intelligence company for conducting sophisticated computer intrusions versus US entities as aspect of an impact and disinformation campaign intended to counter anti-doping endeavours.
Located this article intriguing? Observe THN on Fb, Twitter and LinkedIn to read through much more exceptional content we publish.
Some parts of this post are sourced from:
thehackernews.com


 Cyber Solarium Commission lays out plan to secure supply chain
Cyber Solarium Commission lays out plan to secure supply chain