An Android malware that was noticed abusing accessibility services in the device to hijack person qualifications from European banking apps has morphed into an completely new botnet as part of a renewed marketing campaign that commenced in Might 2021.
Italy’s CERT-AGID, in late January, disclosed facts about Oscorp, a cellular malware designed to attack multiple money targets with the aim of stealing funds from unsuspecting victims. Its functions consist of the means to intercept SMS messages and make phone calls and complete Overlay Attacks for a lot more than 150 cell applications by building use of lookalike login screens to siphon worthwhile details.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The malware was dispersed via destructive SMS messages, with the attacks typically carried out in authentic-time by posing as financial institution operators to dupe targets about the phone and surreptitiously attain entry to the infected gadget by means of WebRTC protocol and in the end conduct unauthorized bank transfers. Even though no new pursuits have been claimed due to the fact then, it seems that Oscorp might have staged a return soon after a temporary hiatus in the form of an Android botnet known as UBEL.
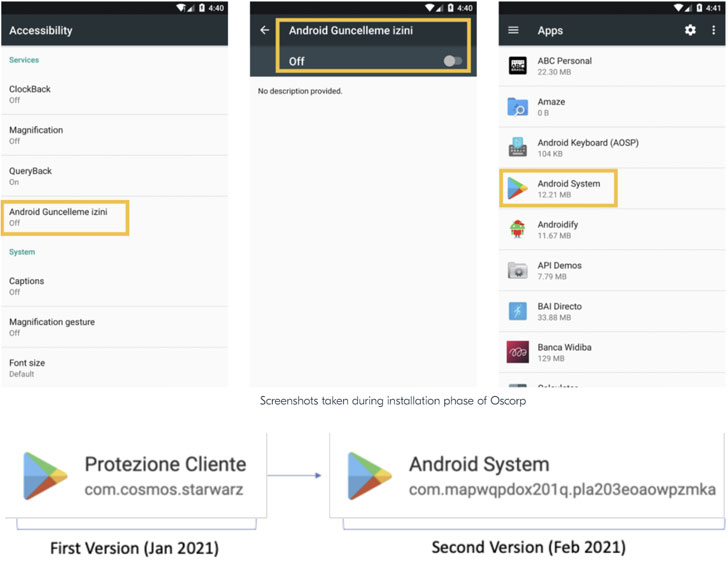
“By examining some relevant samples, we uncovered many indicators linking Oscorp and UBEL to the same destructive codebase, suggesting a fork of the exact original challenge or just a rebrand by other affiliate marketers, as its resource-code appears to be shared concerning a number of [threat actors],” Italian cybersecurity business Cliffy said Tuesday, charting the malware’s evolution.

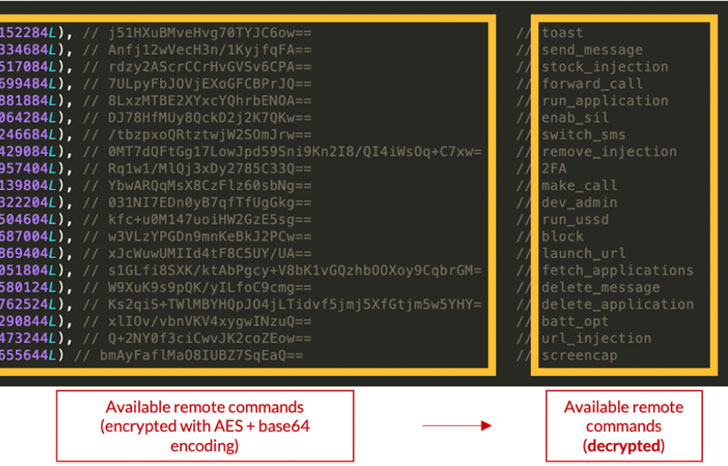
Marketed on underground discussion boards for $980, UBEL, like its predecessor, requests for intrusive permissions that allows it to browse and deliver SMS messages, file audio, put in and delete programs, launch itself routinely after program boot, and abuse accessibility solutions on Android to amass delicate info from the unit this kind of as login qualifications and two-factor authentication codes, the final results of which are exfiltrated back again to a remote server.
At the time downloaded on the product, the malware tries to install alone as a services and cover its existence from the goal, thereby accomplishing persistence for extended durations of time.
Interestingly, the use of WebRTC to interact with the compromised Android phone in authentic-time circumvents the need to enroll a new system and consider above an account to execute fraudulent things to do.
“The primary aim for this [threat actor] by utilizing this aspect, is to stay clear of a ‘new unit enrollment’, therefore greatly reducing the risk of becoming flagged ‘as suspicious’ considering the fact that device’s fingerprinting indicators are well-acknowledged from the bank’s standpoint,” the scientists stated.
The geographical distribution of banking companies and other applications specific by Oscorp consists of Spain, Poland, Germany, Turkey, the U.S., Italy, Japan, Australia, France, and India, amongst others.
Identified this write-up appealing? Observe THN on Fb, Twitter and LinkedIn to browse more special material we post.
Some sections of this write-up are sourced from:
thehackernews.com

 Google launches new bug bounty platform
Google launches new bug bounty platform