Uber, in an update, claimed there is “no proof” that users’ personal info was compromised in a breach of its inner laptop methods that was found late Thursday.
“We have no proof that the incident associated entry to delicate person facts (like trip history),” the business said. “All of our solutions like Uber, Uber Eats, Uber Freight, and the Uber Driver app are operational.”
The journey-hailing business also reported it is really brought again on the net all the interior program resources it took down previously as a precaution, reiterating it is notified legislation enforcement of the subject.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
It really is not promptly apparent if the incident resulted in the theft of any other facts or how extensive the intruder was inside Uber’s network.
Uber has not offered a lot more details of how the incident played out beyond stating its investigation and reaction attempts are ongoing. But unbiased security researcher Bill Demirkapi characterized Uber’s “no evidence” stance as “sketchy.”
“‘No evidence’ could signify the attacker did have entry, Uber just hasn’t discovered proof that the attacker *used* that accessibility for ‘sensitive’ person facts,” Demirkapi reported. “Explicitly declaring “delicate” user info fairly than consumer details overall is also weird.”

The breach allegedly involved a lone hacker, an 18-calendar year-aged teen, tricking an Uber personnel into supplying account entry by social engineering the target into accepting a multi-factor authentication (MFA) prompt that permitted the attacker to sign up their individual system.
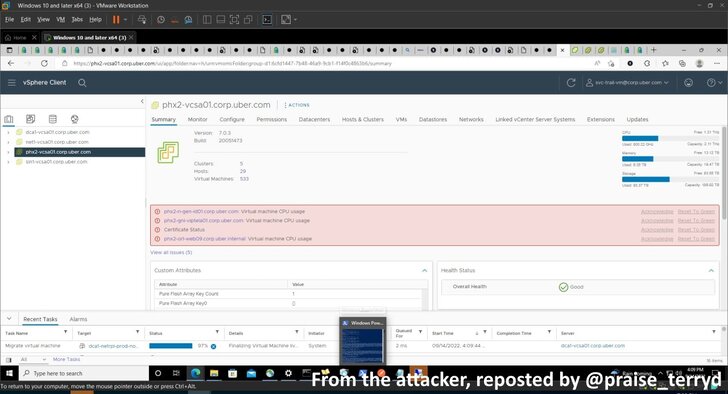
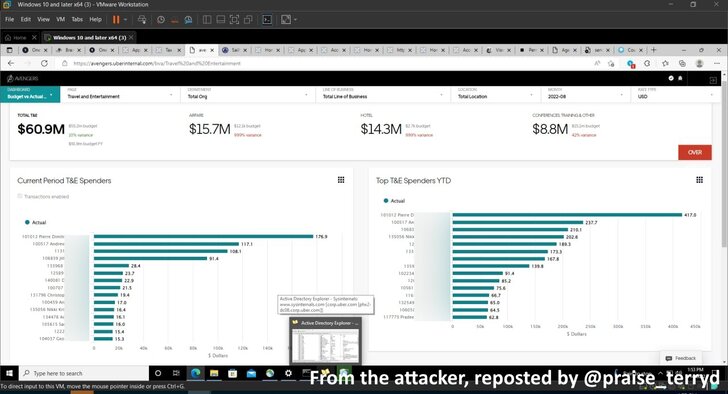
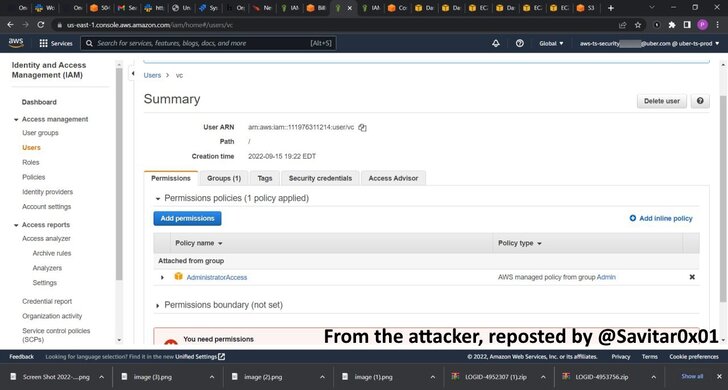
On getting an original foothold, the attacker located an inside network share that contained PowerShell scripts with privileged admin qualifications, granting carte blanche entry to other critical systems, which include AWS, Google Cloud System, OneLogin, SentinelOne incident response portal, and Slack.
Worryingly, as disclosed by security researcher Sam Curry, the teen hacker is also reported to have gotten maintain of privately disclosed vulnerability studies submitted via HackerOne as part of Uber’s bug bounty application.
HackerOne has since moved to disable Uber’s account, but the unauthorized entry to unpatched security flaws in the platform could pose a enormous security risk to the San Francisco-based mostly organization should really the hacker choose to market the information to other danger actors for a quick gain.
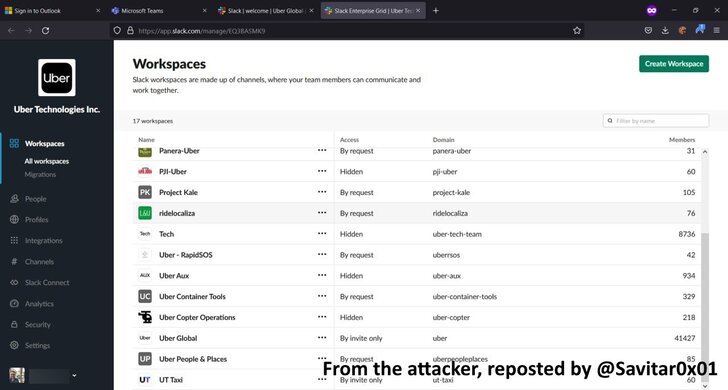
So considerably, the attacker’s motivations guiding the breach are unclear, although a information posted by the hacker saying the breach on Slack bundled a get in touch with for greater pay for Uber’s drivers.
A independent report from The Washington Submit mentioned that the attacker broke into the firm’s networks for enjoyment and may well leak the firm’s resource code in a make any difference of months, while describing Uber’s security as “terrible.”
“Several situations we only speak about APTs, like nation states, and we forget about other danger actors such as disgruntled workforce, insiders, and like in this situation, hacktivists,” Ismael Valenzuela Espejo, vice president of risk analysis and intelligence at BlackBerry, claimed.
“Companies really should include things like these as element of their risk modeling exercise routines to identify who may have a determination to attack the organization, their talent degree and abilities, and what the impact could be according to that analysis.”
The attack targeting Uber, as nicely as the modern string of incidents against Twilio, Cloudflare, Cisco, and LastPass, illustrates how social engineering continues to be a persistent thorn in the flesh for organizations.

It also exhibits that all it can take for a breach to get position is an employee to share their login qualifications, proving that password-based mostly authentication is a weak link in account security.
“Once once again, we see that a firm’s security is only as fantastic as their most susceptible workforce,” Masha Sedova, co-founder and president of Elevate Security, claimed in a assertion.
“We have to have to imagine outside of generic teaching, instead let us pair our riskiest workers with much more certain protective controls. As long as we continue on to deal with cybersecurity as entirely a specialized obstacle, we will continue on to reduce this fight,” Sedova included.
Incidents like these are also proof that Time-based mostly A person Time Password (TOTP) codes – usually created by using authenticator applications or sent as SMS messages – are insufficient at securing 2FA roadblocks.
One way to counter this kind of threats is the use of phishing-resistant FIDO2-compliant bodily security keys, which drops passwords in favor of an external components gadget that handles the authentication.
“MFA providers must *by default* routinely lock accounts out briefly when too several prompts are despatched in a small time period of time,” Demirkapi stated, urging corporations to limit privileged accessibility.
Observed this posting attention-grabbing? Adhere to THN on Facebook, Twitter and LinkedIn to go through far more unique material we post.
Some elements of this post are sourced from:
thehackernews.com


 Hackers Had Access to LastPass’s Development Systems for Four Days
Hackers Had Access to LastPass’s Development Systems for Four Days