A hackers-for-retain the services of operation has been learned utilizing a pressure of earlier undocumented malware to concentrate on South Asian fiscal establishments and global leisure corporations.
Dubbed “CostaRicto” by Blackberry scientists, the campaign appears to be the handiwork of APT mercenaries who have bespoke malware tooling and intricate VPN proxy and SSH tunneling abilities.
“CostaRicto targets are scattered throughout various countries in Europe, Americas, Asia, Australia and Africa, but the largest focus seems to be in South Asia (primarily India, Bangladesh and Singapore and China), suggesting that the menace actor could be primarily based in that region, but performing on a extensive vary of commissions from varied clientele,” the scientists claimed.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
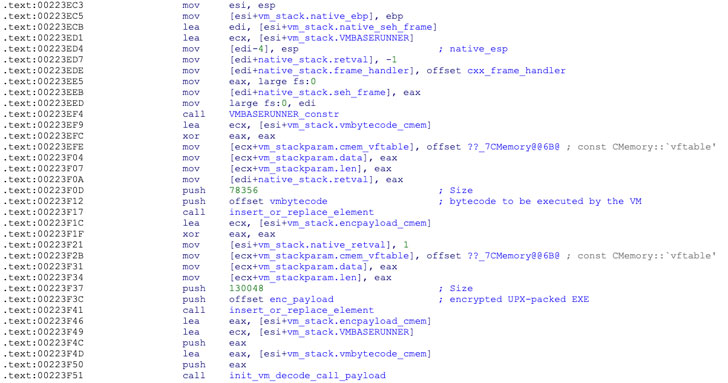
The modus operandi in by itself is rather straight-ahead. On attaining an initial foothold in the target’s ecosystem by way of stolen credentials, the attacker proceeds to established up an SSH tunnel to download a backdoor and a payload loader named CostaBricks that implements a C++ digital machine mechanism to decode and inject the bytecode payload into memory.
In addition to taking care of command-and-regulate (C2) servers by means of DNS tunneling, the backdoor delivered by the over-talked about loaders is a C++ compiled executable called SombRAT — so named right after Sombra, a Mexican hacker, and infiltrator from the popular multiplayer activity Overwatch.
The backdoor will come outfitted with 50 distinct instructions to carry out distinct duties (can be categorized in core, taskman, config, storage, debug, network features) that selection from injecting malicious DLLs into memory to enumerating information in storage to exfiltrating the captured details to an attacker-managed server.
In all, 6 versions of SombRAT have been identified, with the initially version courting all the way back to October 2019 and the most up-to-date variant noticed before this August, implying that the backdoor is less than energetic advancement.
While the identities of the crooks behind the operation are nevertheless mysterious, just one of the IP addresses to which the backdoor domains ended up registered has been linked to an previously phishing marketing campaign attributed to Russia-linked APT28 hacking team, hinting at the chance that the phishing strategies could have been outsourced to the mercenary on behalf of the real threat actor.
This is the next hackers-for-hire operation uncovered by Blackberry, the first currently being a collection of strategies by a group known as Bahamut that was uncovered to exploit zero-working day flaws, malicious software program, and disinformation operations to keep track of targets found in the Middle East and South Asia.
“With the plain success of Ransomware-as-a-Assistance (RaaS), it can be not surprising that the cybercriminal market place has expanded its portfolio to include committed phishing and espionage campaigns to the record of expert services on supply,” Blackberry scientists reported.
“Outsourcing attacks or sure parts of the attack chain to unaffiliated mercenary teams has many rewards for the adversary — it saves their time and assets and simplifies the treatments, but most importantly it provides an supplemental layer of indirection, which aids to protect the true id of the menace actor.”
Found this short article attention-grabbing? Observe THN on Fb, Twitter and LinkedIn to study more exclusive articles we post.
Some pieces of this post are sourced from:
thehackernews.com

 IBM and AMD partner on AI and confidential computing
IBM and AMD partner on AI and confidential computing