Multiple unpatched vulnerabilities have been found out in SHAREit, a preferred app with over a person billion downloads, that could be abused to leak a user’s delicate knowledge, execute arbitrary code, and potentially guide to distant code execution.
The conclusions come from cybersecurity organization Craze Micro’s analysis of the Android version of the application, which enables buyers to share or transfer documents between gadgets.
But in a worrisome twist, the flaws are nevertheless to be patched by Smart Media4U Technology Pte. Ltd., the Singapore-centered developer of the application, even with liable disclosure 3 months in the past.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“We made the decision to disclose our exploration a few months after reporting this considering the fact that numerous users could be impacted by this attack simply because the attacker can steal sensitive facts and do everything with the apps’ permission,” Pattern Micro researcher Echo Duan claimed in a create-up. “It is also not very easily detectable.”

One particular of the flaws arises from the method the app facilitates sharing of files (by way of Android’s FileProvider), perhaps allowing for any third-party to attain non permanent study/produce obtain permissions and exploit them to overwrite existing documents in the app’s data folder.
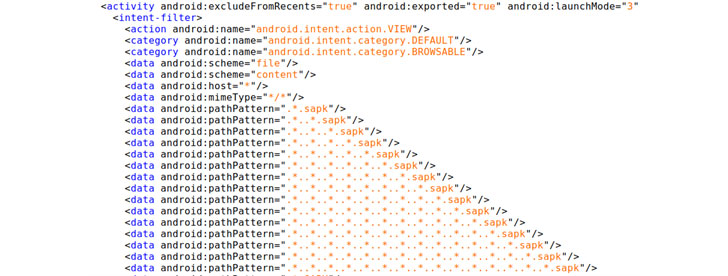
Independently, the use of deep backlinks to launch distinct functions in the application — such as downloading split APK (SAPK) data files from a URL that has the plan of HTTP/HTTPS and area host that matches *.wshareit.com or gshare.cdn.shareitgames.com — can be leveraged to put in a destructive application, resulting in a doable distant code execution when a consumer clicks on a URL.
“When the person clicks this download URL, Chrome will connect with SHAREit to download the SAPK from https://gshare.cdn.shareitgames.com,” Duan explained. “Considering the fact that it supports the HTTP protocol, this SAPK can be replaced by simulating a man-in-the-middle (MitM) attack.”
Last of all, the application is also inclined to what is named a person-in-the-disk (MitD) attack, which occurs when careless use of “external storage” permissions opens the door to the installation of fraudulent applications and even will cause a denial of provider condition.
SHAREit has courted a truthful of security shortcomings in the earlier. In February 2019, two vulnerabilities had been detected in the app that could enable attackers to bypass authentication, obtain arbitrary information, and pilfer documents from Android gadgets.
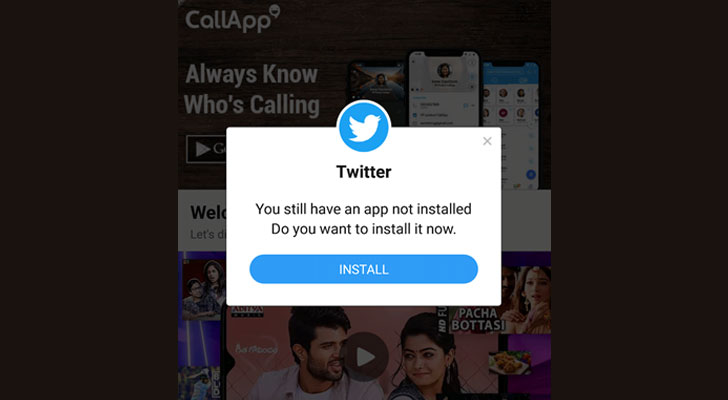 A pop-up from the faux Twitter app created to exam the vulnerability
A pop-up from the faux Twitter app created to exam the vulnerability
Then on June 29, 2020, the Indian federal government banned SHAREit together with 58 other Chinese applications more than issues that these apps were partaking in actions that threatened “countrywide security and defence of India, which ultimately impinges on the sovereignty and integrity of India.”
We have achieved out to the developers of SHAREit, and we will update the story if we hear back.
Observed this post appealing? Comply with THN on Facebook, Twitter and LinkedIn to study additional special content we put up.
Some components of this post are sourced from:
thehackernews.com

 Managed Service Provider? Watch This Video to Learn about Autonomous XDR
Managed Service Provider? Watch This Video to Learn about Autonomous XDR