An unpatched security issue in the Travis CI API has still left tens of hundreds of developers’ user tokens uncovered to probable attacks, successfully enabling threat actors to breach cloud infrastructures, make unauthorized code adjustments, and initiate provide chain attacks.
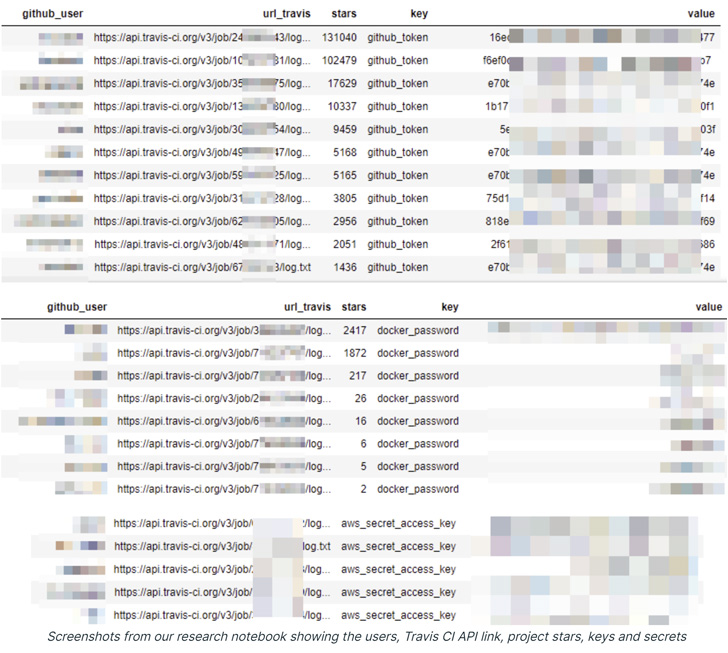
“Extra than 770 million logs of free of charge tier buyers are obtainable, from which you can effortlessly extract tokens, secrets and techniques, and other credentials linked with well-liked cloud assistance companies this kind of as GitHub, AWS, and Docker Hub,” researchers from cloud security agency Aqua reported in a Monday report.
Travis CI is a continuous integration assistance utilised to build and test computer software tasks hosted on cloud repository platforms this kind of as GitHub and Bitbucket.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

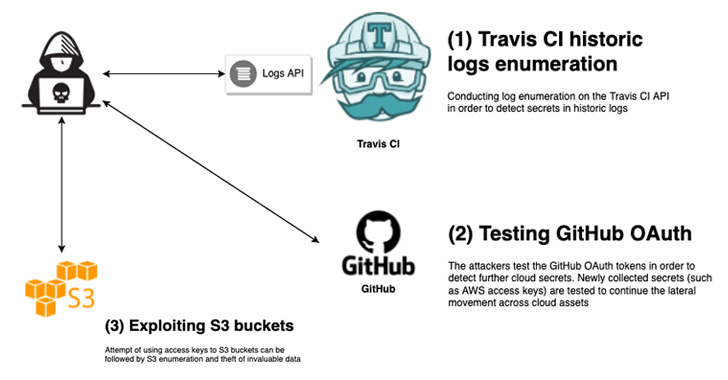
The issue, previously documented in 2015 and 2019, is rooted in the point that the API permits entry to historical logs in cleartext structure, enabling a malicious party to even “fetch the logs that have been earlier unavailable by means of the API.”
The logs go all the way back to January 2013 and up till Might 2022, ranging from log numbers 4,280,000 to 774,807,924, which are utilised to retrieve a one of a kind cleartext log by means of the API.
What is a lot more, even further investigation of 20,000 logs discovered as a lot of as 73,000 tokens, accessibility keys, and other qualifications linked with many cloud solutions like GitHub, AWS, and Docker Hub.
This is regardless of Travis CI’s tries to level-limit the API and mechanically filter out secure setting variables and tokens from establish logs by displaying the string “[secure]” in their put.
A single of the critical insights is that even though “github_token” was obfuscated, 20 other variants of this token that followed a distinct naming conference — together with github_magic formula, gh_token, github_api_important, and github_secret — were not masked by Travis CI.

“Travis CI slowed down the velocity of API phone calls, which hinders the capacity to question the API,” the scientists claimed. “In this case nevertheless, this was not ample. A proficient danger actor can discover a workaround to bypass this.”
“Having said that, combining the ease of accessing the logs by way of the API, incomplete censoring, accessing ‘restricted’ logs, and a weak course of action for price restricting and blocking accessibility to the API, coupled with a huge range of potentially uncovered logs, benefits in a critical predicament.”
Travis CI, in reaction to the conclusions, has mentioned the issue is “by design,” necessitating that end users stick to very best practices to steer clear of leaking techniques in establish logs and periodically rotate tokens and secrets.
The conclusions are specially significant in the wake of an April 2022 attack marketing campaign that leveraged stolen OAuth person tokens issued to Heroku and Travis CI to escalate accessibility to NPM infrastructure and clone select private repositories.
Observed this post interesting? Follow THN on Facebook, Twitter and LinkedIn to go through more exceptional articles we submit.
Some elements of this post are sourced from:
thehackernews.com

 Over Three-Quarters of UK Adults Hit by Online Scams
Over Three-Quarters of UK Adults Hit by Online Scams