Unofficial patches have been issued to remediate an improperly patched Windows security vulnerability that could enable information disclosure and community privilege escalation (LPE) on susceptible units.
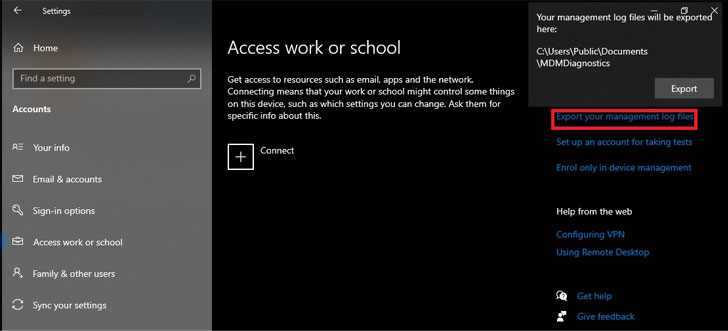
Tracked as CVE-2021-24084 (CVSS rating: 5.5), the flaw worries an information and facts disclosure vulnerability in the Windows Cellular Unit Management ingredient that could permit an attacker to attain unauthorized file technique access and read through arbitrary documents.
Security researcher Abdelhamid Naceri was credited with getting and reporting the bug in Oct 2020, prompting Microsoft to address the issue as part of its February 2021 Patch Tuesday updates.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

But as observed by Naceri in June 2021, not only could the patch be bypassed to realize the very same goal, the researcher this thirty day period identified that the incompletely patched vulnerability could also be exploited to gain administrator privileges and run destructive code on Windows 10 devices functioning the most up-to-date security updates.
“Particularly, as HiveNightmare/SeriousSAM has taught us, an arbitrary file disclosure can be upgraded to regional privilege escalation if you know which files to get and what to do with them,” 0patch co-discovered Mitja Kolsek mentioned in a put up final 7 days.
However, it is really well worth noting that the vulnerability can be exploited to achieve privilege escalation only beneath unique situations, particularly when the system protection feature is enabled on C: Push and at least 1 area administrator account is set up on the laptop.
Neither Windows Servers nor programs working Windows 11 are influenced by the vulnerability, but the following Windows 10 versions are impacted —
- Windows 10 v21H1 (32 & 64 little bit) updated with November 2021 Updates
- Windows 10 v20H2 (32 & 64 little bit) up to date with November 2021 Updates
- Windows 10 v2004 (32 & 64 little bit) updated with November 2021 Updates
- Windows 10 v1909 (32 & 64 little bit) up to date with November 2021 Updates
- Windows 10 v1903 (32 & 64 little bit) up to date with November 2021 Updates
- Windows 10 v1809 (32 & 64 bit) updated with May perhaps 2021 Updates

CVE-2021-24084 is also the 3rd zero-working day Windows vulnerability to rear its head again as a consequence of an incomplete patch issued by Microsoft. Earlier this month, 0patch delivered unofficial fixes for a local privilege escalation vulnerability (CVE-2021-34484) in the Windows Person Profile Assistance that enables attackers to gain Method privileges.
Then last week, Naceri disclosed specifics of a different zero-working day flaw in the Microsoft Windows Installer service (CVE-2021-41379) that could be bypassed to obtain elevated privileges on units managing the most current Windows variations, together with Windows 10, Windows 11, and Windows Server 2022.
Found this short article exciting? Abide by THN on Fb, Twitter and LinkedIn to browse far more distinctive information we publish.
Some areas of this article are sourced from:
thehackernews.com


 Chinotto spyware spies on North Korean defectors and activists
Chinotto spyware spies on North Korean defectors and activists