An unpatched security vulnerability influencing Google’s Compute Motor platform could be abused by an attacker to choose above virtual equipment around the network.
“This is done by impersonating the metadata server from the specific virtual machine’s position of view,” security researcher Imre Rad explained in an evaluation released Friday. “By mounting this exploit, the attacker can grant entry to them selves around SSH (general public vital authentication) so then they can login as the root consumer.”
Google Compute Engine (GCE) is an infrastructure-as-a-service (IaaS) component of Google Cloud System that permits buyers to produce and start digital equipment (VMs) on desire. GCE gives a process for storing and retrieving metadata in the sort of the metadata server, which offers a central stage to set metadata in the sort of important-worth pairs that is then supplied to virtual devices at runtime.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

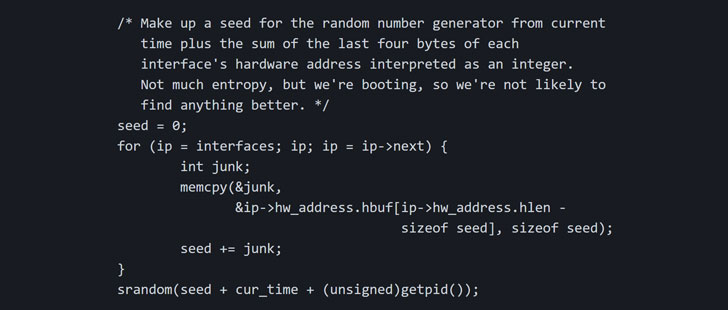
In accordance to the researcher, the issue is a consequence of weak pseudo-random figures utilized by the ISC DHCP client, ensuing in a state of affairs wherein an adversary crafts many DHCP packets employing a established of precalculated transaction identifiers (aka XIDs) and floods the victim’s DHCP consumer, in the end major to the impersonation of the metadata server.
Dynamic Host Configuration Protocol (DHCP) is a network administration protocol used to automate the course of action of configuring gadgets on IP networks. A DHCP server dynamically assigns an IP tackle and other network configuration parameters to every single consumer gadget on a network so that they can communicate with other networks.
“If the XID is suitable, the sufferer equipment applies the network configuration,” Rad spelled out in the technological produce-up. “This is a race issue, but given that the flood is speedy and exhaustive, the metadata server has no serious probability to get. At this stage the attacker is in the place of reconfiguring the network stack of the sufferer.”
Given that a metadata server can be applied to distribute and handle SSH keys, a shopper — now possessing recognized a TCP link to the rogue server — can retrieve the attacker’s SSH general public vital, which can then be made use of by the attacker to open a remote shell as the root consumer.
In a possible serious-planet circumstance, the aforementioned attack chain can be abused by an adversary to acquire full access to a specific virtual equipment as it can be staying rebooted or more than the internet in situations when the cloud platform’s firewall is turned off.

Google was informed about the issue on Sept. 27, 2020, which has since acknowledged the report, describing it as a “awesome capture,” but has however to roll out a patch, or present a timeline for when the correction will be built readily available.
“Until finally the deal with comes, really don’t use DHCP or set up a host degree firewall rule to be certain the DHCP interaction arrives from the metadata server (169.254.169.254),” Rad pointed out. “Block UDP/68 in between VMs, so that only the metadata server could have out DHCP.”
This is far from the 1st time Rad has identified issues in the Google Cloud Platform.
In September 2020, Google rectified a nearby privilege escalation vulnerability in the OS Config tool that could be exploited by an actor with code execution rights on the impacted GCE VMs to complete unauthorized operations.
Then earlier this January, Rad also identified that it was possible to reach arbitrary code execution in a virtual device by getting a shell on the Cloud SQL databases provider. The issue was dealt with by Google on Feb. 16, 2021.
Uncovered this posting appealing? Observe THN on Fb, Twitter and LinkedIn to examine a lot more exclusive material we post.
Some parts of this article are sourced from:
thehackernews.com


 Details of RCE Bug in Adobe Experience Manager Revealed
Details of RCE Bug in Adobe Experience Manager Revealed