State-sponsored actors allegedly operating for Russia have focused the US Treasury, the Commerce Department’s National Telecommunications and Details Administration (NTIA), and other govt companies to monitor inside email visitors as component of a widespread cyberespionage marketing campaign.
The Washington Publish, citing unnamed sources, said the newest attacks ended up the work of APT29 or Cozy Bear, the identical hacking group that’s considered to have orchestrated a breach of US-centered cybersecurity business FireEye a handful of times ago foremost to the theft of its Pink Team penetration testing resources.
The motive and the entire scope of what intelligence was compromised stays unclear, but symptoms are that adversaries tampered with a program update introduced by Texas-centered IT infrastructure company SolarWinds previously this 12 months to infiltrate the programs of federal government companies as effectively as FireEye and mount a extremely-innovative supply chain attack.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
SolarWinds’ networking and security products are utilized by much more than 300,000 clients around the globe, which includes Fortune 500 firms, federal government businesses, and education establishments.
It also serves the important US telecommunications organizations, all 5 branches of the US Military, and other distinguished federal government companies this sort of as the Pentagon, Condition Division, NASA, Nationwide Security Company (NSA), Postal Services, NOAA, Office of Justice, and the Office of the President of the United States.
An Evasive Marketing campaign to Distribute SUNBURST Backdoor
FireEye, which is tracking the ongoing intrusion marketing campaign less than the moniker “UNC2452,” said the source chain attack can take advantage of trojanized SolarWinds Orion company software updates in get to distribute a backdoor referred to as SUNBURST.
“This marketing campaign might have begun as early as Spring 2020 and is now ongoing,” FireEye claimed in a Sunday examination. “Post compromise action pursuing this offer chain compromise has integrated lateral movement and facts theft. The campaign is the get the job done of a highly competent actor and the procedure was carried out with major operational security.”
This rogue model of SolarWinds Orion plug-in, moreover masquerading its network visitors as the Orion Enhancement System (OIP) protocol, is claimed to connect by way of HTTP to distant servers so as to retrieve and execute destructive instructions (“Positions”) that cover the spyware gamut, which include these for transferring documents, executing files, profiling and rebooting the goal method, and disabling technique expert services.
Orion Enhancement System or OIP is mainly employed to obtain functionality and usage studies data from SolarWinds users for merchandise improvement reasons.
What is much more, the IP addresses employed for the marketing campaign were obfuscated by VPN servers positioned in the exact same state as the sufferer to evade detection.
Microsoft also corroborated the conclusions in a separate investigation, stating the attack (which it phone calls “Solorigate”) leveraged the have confidence in associated with SolarWinds software program to insert destructive code as element of a larger sized marketing campaign.
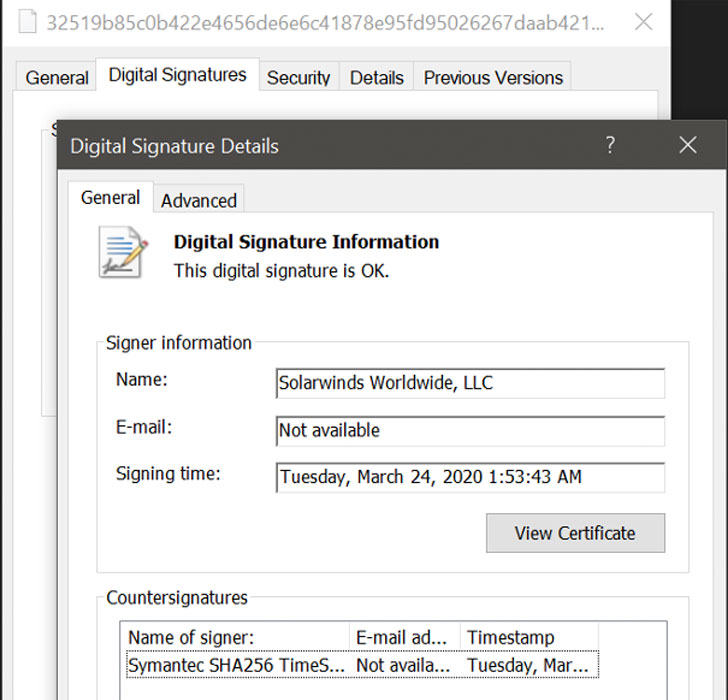
“A malicious software program class was integrated amongst quite a few other respectable courses and then signed with a legitimate certificate,” the Windows maker stated. The ensuing binary involved a backdoor and was then discreetly distributed into targeted corporations.”
SolarWinds Releases Security Advisory
In a security advisory posted by SolarWinds, the corporation stated the attack targets versions 2019.4 by way of 2020.2.1 of the SolarWinds Orion Platform program that was launched between March and June 2020, when recommending customers to upgrade to Orion System launch 2020.2.1 HF 1 quickly.
The company, which is at the moment investigating the attack in coordination with FireEye and the US Federal Bureau of Investigation, is also anticipated to launch an further hotfix, 2020.2.1 HF 2, on December 15, which replaces the compromised element and provides many added security enhancements.
FireEye last week disclosed that it fell target to a highly sophisticated overseas-governing administration attack that compromised its software program tools utilized to examination the defenses of its prospects.
Totaling as quite a few as 60 in amount, the stolen Crimson Staff instruments are a combine of publicly readily available instruments (43%), modified variations of publicly accessible equipment (17%), and all those that had been designed in-house (40%).
Moreover, the theft also features exploit payloads that leverage critical vulnerabilities in Pulse Safe SSL VPN (CVE-2019-11510), Microsoft Energetic Directory (CVE-2020-1472), Zoho ManageEngine Desktop Central (CVE-2020-10189), and Windows Remote Desktop Providers (CVE-2019-0708).
The campaign, in the end, seems to be a supply chain attack on a international scale, for FireEye stated it detected this activity across numerous entities throughout the world, spanning federal government, consulting, technology, telecom, and extractive firms in North The united states, Europe, Asia, and the Middle East.
The indicators of compromise (IoCs) and other applicable attack signatures intended to counter SUNBURST can be accessed below.
Discovered this short article interesting? Stick to THN on Fb, Twitter and LinkedIn to examine additional unique content we write-up.
Some areas of this article are sourced from:
thehackernews.com


 From the startup to the enterprise: where cyber fits in a business’s growth trajectory
From the startup to the enterprise: where cyber fits in a business’s growth trajectory