A important selection of victims in the consumer and enterprise sectors situated across Australia, Japan, the U.S., and India have been impacted by an evasive information and facts-stealing malware identified as ViperSoftX.
ViperSoftX was initial documented in 2020, with cybersecurity firm Avast detailing a campaign in November 2022 that leveraged the malware to distribute a malicious Google Chrome extension capable of siphoning cryptocurrencies from wallet apps.
Now a new examination from Trend Micro has discovered the malware’s adoption of “much more innovative encryption and basic anti-assessment approaches, these as byte remapping and web browser interaction blocking.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The arrival vector of ViperSoftX is generally a computer software crack or a vital generator (keygen), whilst also utilizing genuine non-malicious computer software like multimedia editors and process cleaner applications as “carriers.”
One particular of the essential actions performed by the malware ahead of downloading a initially-phase PowerShell loader is a sequence of anti-virtual equipment, anti-checking, and anti-malware checks.
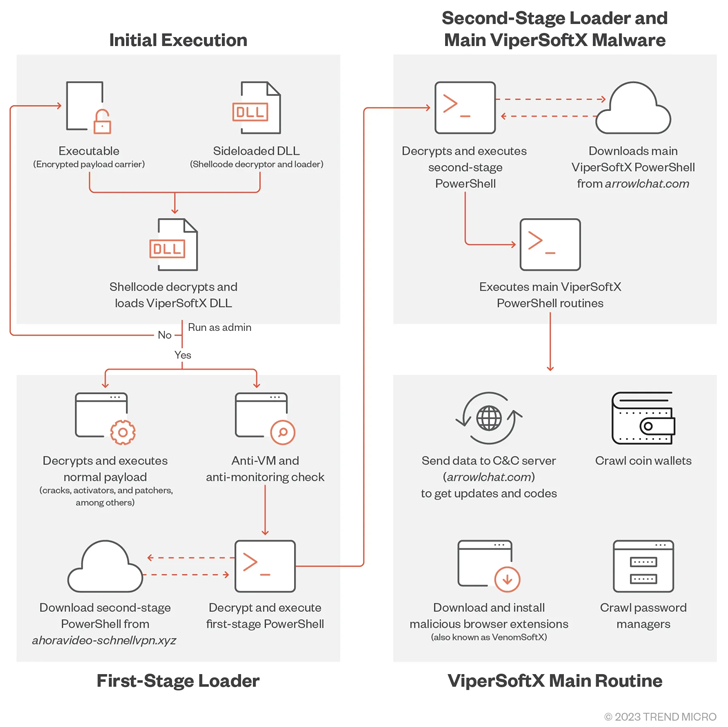
The loader then decrypts and executes a second-phase PowerShell script retrieved from a remote server, which then normally takes treatment of launching the most important regime responsible for putting in rogue browser extensions to exfiltrate passwords and crypto wallet details.
The most important command-and-management (C&C) servers utilised for the second stage down load have been observed to modify on a month to month basis, suggesting attempts on the portion of the actor to sidestep detection.
Upcoming WEBINARLearn to Cease Ransomware with True-Time Defense
Sign up for our webinar and study how to stop ransomware attacks in their tracks with authentic-time MFA and support account safety.
Conserve My Seat!
“It also utilizes some primary anti-C&C analyses by disallowing communications working with web browsers,” Trend Micro researcher Don Ovid Ladores mentioned, introducing the current model of ViperSoftX scans for the existence of KeePass 2 and 1Password password managers.
As mitigations, it’s recommended that buyers obtain application only from official platforms and sources, and stay clear of downloading unlawful application.
“The cybercriminals driving ViperSoftX are also expert enough to execute a seamless chain for malware execution although keeping less than the radar of authorities by picking out a single of the most productive techniques for offering malware to consumers,” Ovid Ladores extra.
Discovered this report intriguing? Comply with us on Twitter and LinkedIn to go through more exceptional material we put up.
Some elements of this write-up are sourced from:
thehackernews.com

 Man Gets Four Years for Stealing Bitcoins Seized by Feds
Man Gets Four Years for Stealing Bitcoins Seized by Feds