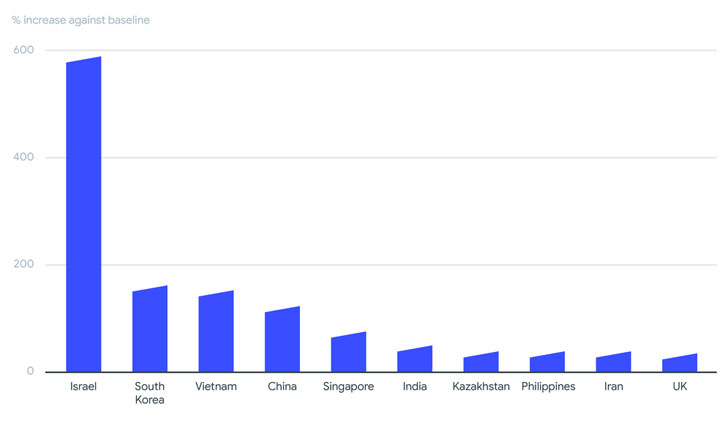
As many as 130 various ransomware people have been identified to be lively in 2020 and the very first 50 percent of 2021, with Israel, South Korea, Vietnam, China, Singapore, India, Kazakhstan, Philippines, Iran, and the U.K. rising as the most impacted territories, a comprehensive evaluation of 80 million ransomware-similar samples has revealed.
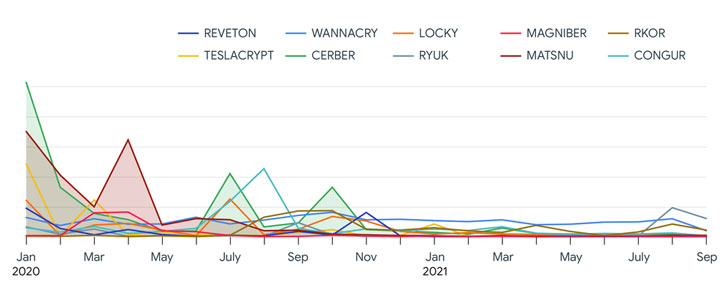
Google’s cybersecurity arm VirusTotal attributed a considerable chunk of the exercise to the GandCrab ransomware-as-a-assistance (RaaS) team (78.5%), followed by Babuk (7.61%), Cerber (3.11%), Matsnu (2.63%), Wannacry (2.41%), Congur (1.52%), Locky (1.29%), Teslacrypt (1.12%), Rkor (1.11%), and Reveon (.70%).


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“Attackers are applying a assortment of ways, which include very well-recognized botnet malware and other Remote Entry Trojans (RATs) as automobiles to deliver their ransomware,” VirusTotal Danger Intelligence Strategist Vicente Diaz reported. “In most scenarios, they are using new or new ransomware samples for their campaigns.”
Some of the other important factors uncovered in the research are as follows —
- GandCrab accounted for most of the ransomware action in the very first two quarters of 2020, with the Babuk ransomware loved ones driving a surge of bacterial infections in July 2021.
- 95% of ransomware information detected were Windows-centered executables or dynamic hyperlink libraries (DLLs), while 2% were Android-based.
- All-around 5% of the analyzed samples were being affiliated with exploits similar to Windows elevation of privileges, SMB information disclosures, and distant execution.
- Emotet, Zbot, Dridex, Gozi, and Danabot have been the most important malware artifacts applied to distribute ransomware.
The conclusions come in the wake of a relentless wave of ransomware attacks aimed at critical infrastructure, with cybercriminal gangs aggressively pursuing victims in critical sectors, together with pipeline operators and health care amenities, even as the landscape has witnessed a continual shift wherein ransomware teams evolve, splinter, and reorganize under new names, or fall off the radar to evade scrutiny.
If nearly anything, the explosion of new malware households has drawn new actors into participating in these valuable strategies, turning ransomware into a financially rewarding felony organization product.
“Even though massive strategies occur and go, there is a constant baseline of ransomware action of somewhere around 100 ransomware households that under no circumstances stops,” the report said. “In conditions of ransomware distribution attackers do not seem to need exploits other than for privilege escalation and for malware spreading inside internal networks.”
Identified this short article interesting? Observe THN on Facebook, Twitter and LinkedIn to study more exclusive content we put up.
Some pieces of this post are sourced from:
thehackernews.com


 Hackers fake DocuSign and offer fraudulent signing methods
Hackers fake DocuSign and offer fraudulent signing methods