VMware has released security updates for multiple solutions to handle a critical vulnerability that could be exploited to attain obtain to private facts.
Tracked as CVE-2021-22002 (CVSS rating: 8.6) and CVE-2021-22003 (CVSS score: 3.7), the flaws affect VMware Workspace 1 Accessibility (Access), VMware Id Supervisor (vIDM), VMware vRealize Automation (vRA), VMware Cloud Foundation, and vRealize Suite Lifecycle Manager.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
CVE-2021-22002 issues an issue with how VMware Workspace A person Obtain and Id Supervisor let the “/cfg” web application and diagnostic endpoints to be accessed by using port 443 by tampering with a host header, resulting in a server-side ask for.
“A destructive actor with network entry to port 443 could tamper with host headers to facilitate obtain to the /cfg web app, in addition a malicious actor could obtain /cfg diagnostic endpoints without authentication,” the corporation mentioned in its advisory. Suleyman Bayir of Trendyol has been credited with reporting the flaw.
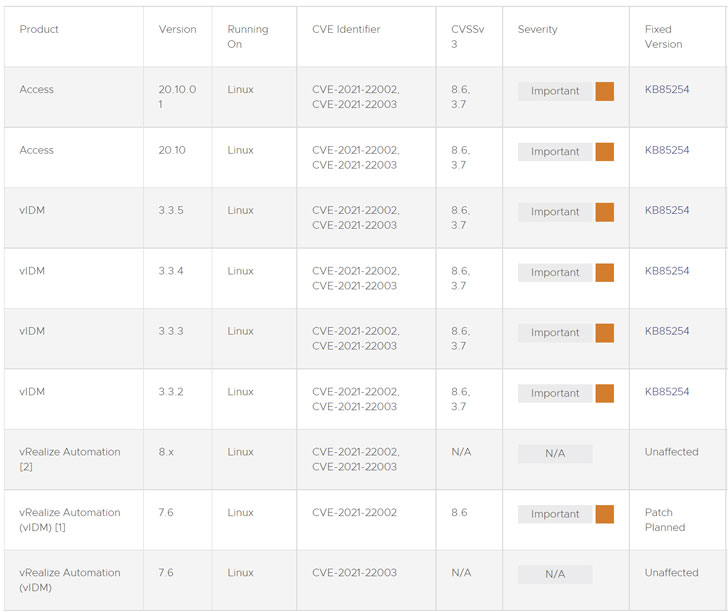
Also resolved by VMware is an data disclosure vulnerability impacting VMware Workspace 1 Access and Identity Manager through an inadvertently exposed login interface on port 7443. An attacker with network access to port 7443 could probably stage a brute-pressure attack, which the firm mentioned: “may perhaps or may not be realistic based on lockout plan configuration and password complexity for the focus on account.”

For shoppers who simply cannot enhance to the newest variation, VMware is supplying a workaround script for CVE-2021-22002 that can be deployed independently with no using the vRA appliances offline. “The workaround disables the means to take care of the configuration page of vIDM. This endpoint is not employed in vRA 7.6 environments and will not trigger any impact to functionality,” the enterprise explained.
Located this article attention-grabbing? Follow THN on Fb, Twitter and LinkedIn to read through more exceptional written content we article.
Some sections of this write-up are sourced from:
thehackernews.com


 #BHUSA: DHS Chief: ‘We are Competing for the Future of Cyberspace’
#BHUSA: DHS Chief: ‘We are Competing for the Future of Cyberspace’