After far more than 20 yrs in the producing, now it is formal: APIs are everywhere you go. In a 2021 survey, 73% of enterprises reported that they now publish additional than 50 APIs, and this quantity is continually escalating.
APIs have critical roles to perform in practically just about every industry currently, and their significance is raising steadily, as they go to the forefront of company strategies. This arrives as no surprise: APIs seamlessly hook up disparate applications and products, bringing business enterprise synergies and efficiencies never ever witnessed just before.
Even so, APIs have vulnerabilities just like any other ingredient of the application. Including to that, if they aren’t rigorously analyzed from a security standpoint, they can also introduce a whole new array of attack surfaces and expose you to unparalleled hazards. If you hold out right up until generation to find out API vulnerabilities, you can incur sizeable delays.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
APIs are desirable to attackers, not just firms
Hold in thoughts that APIs do far more than simply just hook up your apps they modify the features in unpredictable means. Many of the special weaknesses that APIs may introduce are nicely recognised to hackers, who have produced diverse methods to attack your APIs in order to access the underlying information and functionality.
In accordance to the OWASP API Major 10, it is not uncommon for authentic, authenticated buyers to exploit the API by using phone calls that seem legit but are basically supposed to manipulate the API. These types of attacks, aiming to manipulate the business enterprise logic and exploit style and design flaws, are desirable to attackers.
You see, each and every API is distinctive and proprietary. As this sort of, its application bugs and vulnerabilities are special and “mysterious” as well. The form of bugs that direct to attacks at the small business logic or small business procedure degree is especially tough to determine as a defender.

Are you giving API security testing sufficient attention?
Change-still left security is by now widely recognized in several organizations, allowing for for steady screening through advancement. API security screening, even so, generally falls by means of the cracks or is done without the need of a sufficient comprehending of the dangers involved. Why is that? Very well, there is extra than a person cause:
So, even though change-left security is by now valued by lots of businesses in normal, API security testing is also often left out of the DevSecOps huge photograph.
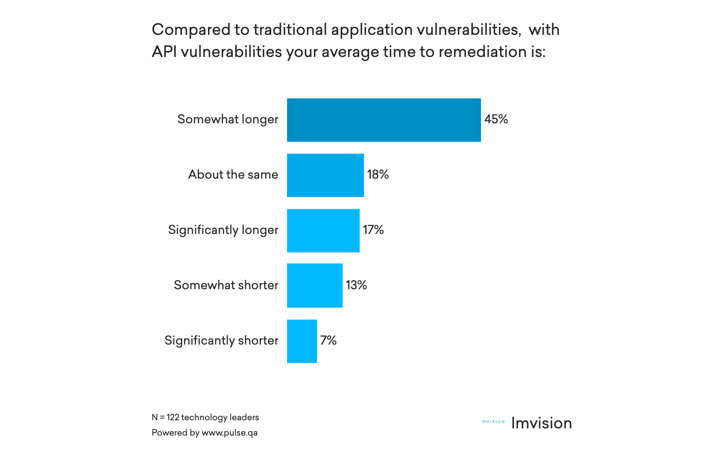
This is unlucky, since API vulnerabilities involve for a longer period to remediate than conventional software vulnerabilities – in a new study, 63% of respondents noted that it can take for a longer period to remediate API vulnerabilities. This number is also possible to increase supplied applications’ speedy adoption of and dependence on APIs.
Whilst most security leaders are mindful of the great importance of API security tests, just underneath 50 percent say they will not nonetheless have an API security tests resolution thoroughly integrated into their enhancement pipeline.
Understand far more on how to protect against attacks by proactively identifying vulnerabilities, from generation again to code.
Why do prevalent security testing strategies fall short to include APIs?
As a initially phase in direction of a in depth technique, it is crucial to analyze the most popular attitudes in direction of software security screening now: static security testing and dynamic security testing.
Static security testing takes a white-box strategy, making checks based mostly on the identified features of the software by reviewing the style and design, architecture, or code, together with the many advanced paths that information can consider as it passes by means of the software.
Dynamic security screening will take a black-box strategy, building exams based on the envisioned effectiveness of the software provided a individual established of inputs, disregarding internal processing or information of the underlying code.
When it will come to APIs, developers and security groups commonly argue about which of the two approaches is most suitable, with the major reasoning in favor of just about every currently being:
- Static testing is the only strategy that can make feeling: considering that there is no person interface for APIs, you have to know what’s heading on within the company logic.
- Dynamic screening is all that is required, considering the fact that device assessments use static products and have previously been completed at an before phase of the pipeline.
Sorry to damage the party, but the two of these details are only partially true. As a subject of truth, the two strategies are important to assure broad coverage and deal with a wide range of doable eventualities. Specifically with the current increase of API-based attacks, you can not just take any likelihood when it arrives to scalability, depth, and frequency.
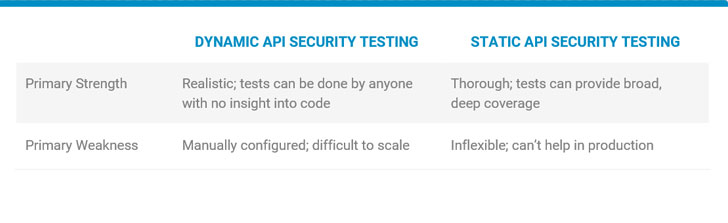
‘Grey-box’ API security screening could supply an interesting alternative. Since there’s no user interface, obtaining awareness of the app’s inner workings (e.g., parameters, return types) can assistance you competently make purposeful checks that emphasis on the organization logic.
Preferably, combining facets of API security screening would get you nearer to producing a grey-box answer that compensates for the weaknesses of each and every of these individual strategies. This kind of a small business logic tactic would intelligently study benefits of other examination styles and can adapt to apply enhanced assessments, both automatically or manually.
It is time for a Business enterprise Logic API Security Screening Technique
There is certainly growing marketplace awareness surrounding the have to have to protected APIs across their lifecycle, putting APIs front and heart in your security controls.
To do this, you ought to uncover ways to simplify and streamline your organization’s API security testing, integrating and enforcing API security tests requirements in the enhancement cycle. This way, along with runtime monitoring, the security crew can gain visibility into all recognized vulnerabilities in 1 put. As a reward, taking steps to change-left API security screening will slice charges and accelerate time to remediation.
Also, once your testing workflows are automatic, you can expect to also have crafted-in aid for retesting: a cycle of take a look at, remediate, retest, and deploy, retaining your pipeline managing efficiently and preventing bottlenecks entirely.
A organization logic method to API security screening can elevate the maturity of your Full Lifecycle API Security application, and boost your security posture.
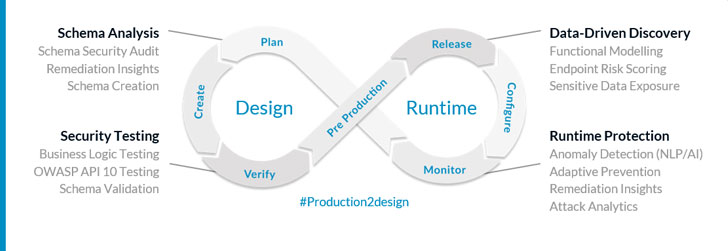
Even so, this modern-day approach requires a software that can learn as it goes, improving upon its efficiency more than time by ingesting runtime knowledge to achieve insights into the application’s composition and logic.
This would include making an adaptive take a look at engine that can study as it goes, developing a further awareness of the API’s behavior in get to reverse-engineer its hidden inner workings intelligently. Making use of runtime facts and organization logic info, you can take pleasure in the greatest of the two worlds – the black and white box method to increased visibility and command with automation.
Learn far more on how to reduce attacks by proactively pinpointing vulnerabilities, from output again to code.
To wrap up
In addition to their raising attractiveness, APIs also produce greater vulnerability for web purposes. A big number of corporations do not even know what the extent of their APIs and vulnerabilities are. Recognized and unfamiliar weaknesses can quickly be probed by hackers through obtainable APIs.
Having said that, API security testing is generally missed and managed the same as web apps. Most tests techniques, these as black-box and white-box tests, are not conducive to API tests.
A mix of organic language processing and artificial intelligence (AI) presents a feasible “gray box” solution that automates, scales, and simplifies the advanced approach of API security tests.
Identified this write-up intriguing? Follow THN on Facebook, Twitter and LinkedIn to read through extra special written content we publish.
Some sections of this post are sourced from:
thehackernews.com


 Dutch Police Arrest Two Hackers Tied to “Fraud Family” Cybercrime Ring
Dutch Police Arrest Two Hackers Tied to “Fraud Family” Cybercrime Ring