Google has disclosed that a now-patched vulnerability influencing Android gadgets that use Qualcomm chipsets is currently being weaponized by attackers to start focused attacks.
Tracked as CVE-2020-11261 (CVSS score 8.4), the flaw issues an “improper input validation” issue in Qualcomm’s Graphics element that could be exploited to induce memory corruption when an attacker-engineered application requests access to a huge chunk of the device’s memory.
“There are indications that CVE-2020-11261 may possibly be under minimal, specific exploitation,” the look for huge said in an updated January security bulletin on March 18.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
CVE-2020-11261 was discovered by Google’s Android Security team on July 20, 2020, and described to Qualcomm, following which it was fixed in January 2021.
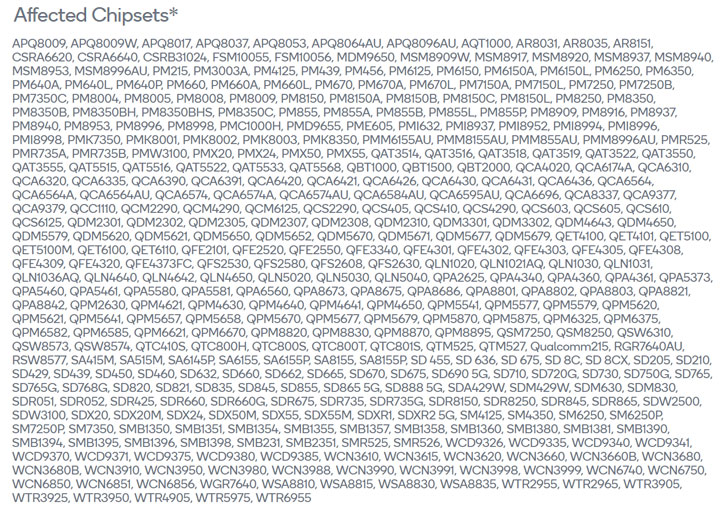
It can be worthy of noting that the obtain vector for the vulnerability is “community,” indicating that exploitation demands local accessibility to the system. In other terms, to start a productive attack, the negative actor should possibly have bodily obtain to the susceptible smartphone or use other implies – e.g., a watering hole – to supply destructive code and set off the attack chain.
Though particulars about the attacks, the identity of the attacker, and the specific victims have not been introduced, it is not unusual for Google to withhold sharing these information and facts to protect against other risk actors from having gain of the vulnerability.
If anything at all, the improvement at the time once more underscores the want to instantly put in monthly security updates as shortly as they are available to avert Android devices from remaining exploited. We have attained out to Google for comment and will update this short article if we hear back.
Discovered this write-up interesting? Stick to THN on Facebook, Twitter and LinkedIn to study far more exclusive content material we publish.
Some parts of this posting are sourced from:
thehackernews.com

 Securing the Super Bowl: Lessons in network lockdown during mega events
Securing the Super Bowl: Lessons in network lockdown during mega events