In an additional locating that could expose builders to increased risk of a offer chain attack, it has emerged that almost 1-3rd of the deals in PyPI, the Python Bundle Index, result in computerized code execution upon downloading them.
“A worrying attribute in pip/PyPI permits code to instantly run when builders are merely downloading a deal,” Checkmarx researcher Yehuda Gelb claimed in a specialized report published this 7 days.
“Also, this element is alarming thanks to the reality that a fantastic offer of the destructive deals we are obtaining in the wild use this characteristic of code execution upon installation to achieve higher an infection costs.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
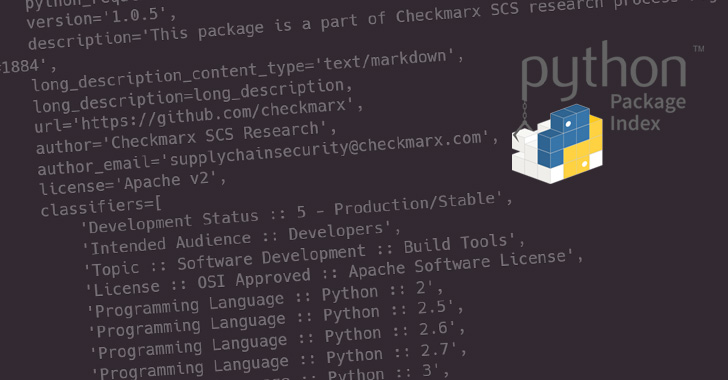
1 of the strategies by which deals can be installed for Python is by executing the “pip set up” command, which, in flip, invokes a file known as “set up.py” that comes bundled together with the module.

“set up.py,” as the name implies, is a set up script which is applied to specify metadata linked with the package, which includes its dependencies.
Although menace actors have resorted to incorporating destructive code in the setup.py file, Checkmarx discovered that adversaries could accomplish the exact same goals by working what’s identified as a “pip down load” command.
“pip download does the same resolution and downloading as pip put in, but as an alternative of putting in the dependencies, it collects the downloaded distributions into the listing supplied (defaulting to the current listing),” the documentation reads.
In other terms, the command can be made use of to download a Python bundle with out having to set up it on the program. But as it turns out, executing the download command also operates the aforementioned “setup.py” script, resulting in the execution of malicious code contained in it.
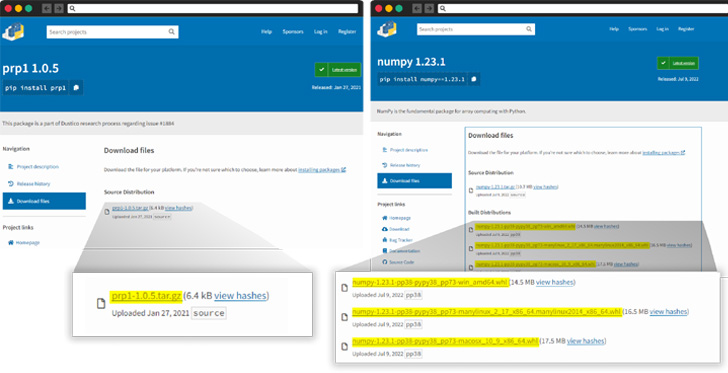
However, it is really worthy of noting that the issue happens only when the deal consists of a tar.gz file as an alternative of a wheel (.whl) file, which “cuts the ‘setup.py’ execution out of the equation.”
“Builders opting to download, alternatively of installing packages, are fairly expecting that no code will run on the machine upon downloading the information,” Gelb observed, characterizing it as a design and style issue rather than a bug.
Whilst pip defaults to working with wheels rather of tar.gz documents, an attacker could get edge of this behavior to intentionally publish python deals without a .whl file, top to the execution of the malicious code current in the setup script.

“When a person downloads a python package from PyPi, pip will preferentially use the .whl file, but will tumble back again to the tar.gz file if the .whl file is missing,” Gelb mentioned.
The results appear as the U.S. Nationwide Security Company (NSA), together with the Cybersecurity and Infrastructure Security Company (CISA) and the Office of the Director of Nationwide Intelligence (ODNI), unveiled steering for securing the computer software supply chain.
“As the cyber menace carries on to grow to be more refined, adversaries have started to attack the computer software source chain, rather than count on publicly regarded vulnerabilities,” the agency claimed. “Right until all DevOps are DevSecOps, the software program development lifecycle will be at risk.”
Discovered this write-up attention-grabbing? Follow THN on Fb, Twitter and LinkedIn to go through additional unique information we write-up.
Some components of this report are sourced from:
thehackernews.com

 ‘Vast majority’ of mobile apps found leaking AWS credentials are on iOS
‘Vast majority’ of mobile apps found leaking AWS credentials are on iOS