GO SMS Pro, a popular messaging app for Android with about 100 million installs, has been found to have an unpatched security flaw that publicly exposes media transferred involving end users, which include personal voice messages, images, and videos.”This indicates any sensitive media shared in between users of this messenger app is at risk of being compromised by an unauthenticated attacker or curious person,” Trustwave Senior Security Consultant Richard Tan explained in a report shared with The Hacker Information.In accordance to Trustwave SpiderLabs, the shortcoming was noticed in model 7.91 of the app, which was launched on the Google Participate in Shop on February 18, 2020.
The cybersecurity firm explained it tried to make contact with the application makers multiple times since August 18, 2020, without the need of obtaining a response.But checking the app’s changelog, GO SMS Pro obtained an update (v7.92) on September 29, adopted by a different subsequent update, which was revealed yesterday. The most current updates to the application, even so, however would not handle the weak spot talked about previously mentioned.
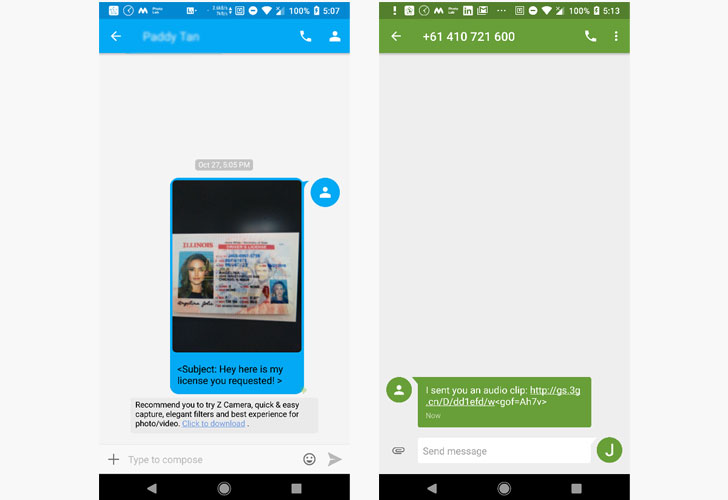
The vulnerability stems from the way media information is displayed when recipients really don’t have the GO SMS Pro app set up on their devices, leading to likely publicity.”If the receiver has the GO SMS Pro application on their unit, the media would be displayed quickly within just the application,” Tan reported. “Nevertheless, if the recipient does not have the GO SMS Pro application mounted, the media file is despatched to the recipient as a URL by way of SMS. The person could then simply click on the hyperlink and view the media file via a browser.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Not only is this website link (e.g. “https://gs.3g.cn/D/dd1efd/w”) available to any one without prior authentication, the URL is generated irrespective of no matter whether the receiver has the app put in, thereby enabling a destructive actor to entry any media information sent through the application.
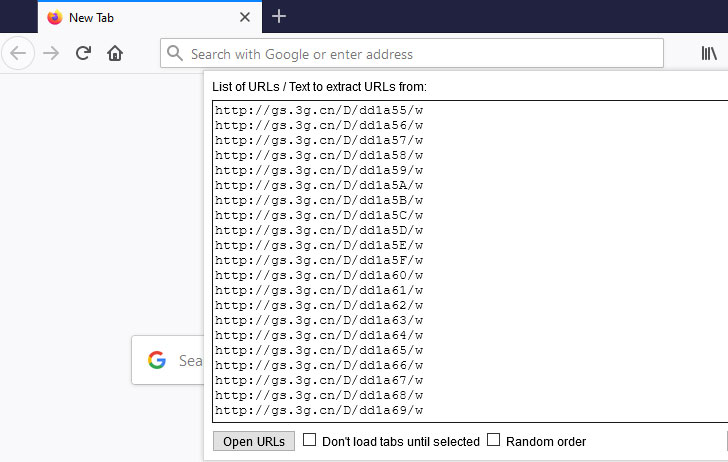
Exclusively, by incrementing the sequential hexadecimal values in the URL (e.g., “https://gs.3g.cn/D/e3a6b4/w”), the flaw will make it achievable to view or hear to other media messages shared in between other users. An attacker can leverage this procedure to make a listing of URLs and steal consumer information without having their understanding.It is really very likely that the flaw impacts the iOS version of GO SMS Pro as properly, but until there is a resolve in area, it is remarkably advisable to keep away from sending media information utilizing the afflicted messenger app.We have achieved out to the developers of GO SMS Pro, and we will update the tale if we listen to back.
Identified this write-up interesting? Stick to THN on Facebook, Twitter and LinkedIn to browse far more special content we publish.
Some elements of this write-up are sourced from:
thehackernews.com

 Cybercriminals Batter Automakers With Ransomware, IP Theft Cyberattacks
Cybercriminals Batter Automakers With Ransomware, IP Theft Cyberattacks