Cyber attackers are actively location their sights on unsecured SAP programs in an endeavor to steal information and sabotage critical procedures, in accordance to new investigation.
“Noticed exploitation could lead in lots of situations to complete control of the unsecured SAP application, bypassing typical security and compliance controls, and enabling attackers to steal sensitive information and facts, execute monetary fraud or disrupt mission-critical small business processes by deploying ransomware or halting functions,” cybersecurity organization Onapsis and SAP stated in a joint report posted currently.
The Boston-centered organization said it detected more than 300 successful exploitations out of a complete of 1,500 makes an attempt concentrating on previously recognised vulnerabilities and insecure configurations unique to SAP units concerning mid-2020 to March 2021, with numerous brute-drive makes an attempt made by adversaries aimed at large-privilege SAP accounts as very well as chaining together numerous flaws to strike SAP purposes.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Applications that have been qualified consist of, but not confined to enterprise resource preparing (ERP), provide chain management (SCM), human capital management (HCM), merchandise lifecycle management (PLM), consumer relationship administration (CRM), and other folks.
Troublingly, Onapsis report outlines weaponization of SAP vulnerabilities in considerably less than 72 hours from the launch of patches, with new unprotected SAP applications provisioned in cloud environments becoming found out and compromised in considerably less than 3 several hours.
In 1 circumstance, a day just after SAP issued a patch for CVE-2020-6287 (far more down below) on July 14, 2020, a evidence-of-idea exploit emerged in the wild, which was followed by mass scanning exercise on July 16 and the release of a entirely-purposeful general public exploit on July 17, 2020.
The attack vectors ended up no a lot less sophisticated. The adversaries have been identified to adopt a diversified established of techniques, equipment, and processes to acquire original accessibility, escalate privileges, fall web shells for arbitrary command execution, make SAP administrator consumers with superior privileges, and even extract database qualifications. The attacks them selves were launched with the aid of TOR nodes and dispersed digital private servers (VPS).
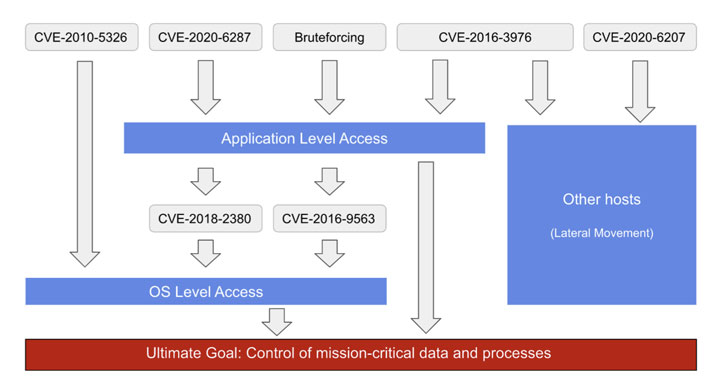
The 6 flaws exploited by risk actors involve —
- CVE-2010-5326 (CVSS rating: 10) – Remote code execution flaw in SAP NetWeaver Application Server (AS) Java
- CVE-2016-3976 (CVSS score: 7.5) – Listing traversal vulnerability in SAP NetWeaver AS Java
- CVE-2016-9563 (CVSS score: 6.4) – XML External Entity (XXE) growth vulnerability in BC-BMT-BPM-DSK ingredient of SAP NetWeaver AS Java
- CVE-2018-2380 (CVSS score: 6.6) – Listing traversal vulnerability in Internet Gross sales element in SAP CRM
- CVE-2020-6207 (CVSS rating: 9.8) – Missing authentication test in SAP Option Manager
- CVE-2020-6287 (CVSS rating: 10) – RECON (aka Remotely Exploitable Code On NetWeaver) flaw in LM Configuration Wizard component
Initially disclosed in July 2020, successful exploitation of CVE-2020-6287 could give an unauthenticated attacker total accessibility to the influenced SAP method, counting the “capacity to modify money data, steal personally identifiable information (PII) from personnel, buyers and suppliers, corrupt information, delete or modify logs and traces and other actions that set important small business functions, cybersecurity and regulatory compliance at risk.”
Onapsis also mentioned it was equipped to detect scanning activity for CVE-2020-6207 relationship again to October 19, 2020, practically 3 months prior to the community release of a completely-performing exploit on January 14, 2021, implying that risk actors had understanding of the exploit prior to the general public disclosure.
Furthermore, a different attack observed on December 9 was located to chain exploits for 3 of the flaws, particularly CVE-2020-6287 for creating an admin consumer and logging in to the SAP program, CVE-2018-2380 for privilege escalation, and CVE-2016-3976 for obtain to substantial-privileged accounts and the database.
“This all happened within just 90 minutes,” Onapsis scientists pointed out.
When no buyer breaches have been uncovered, both of those SAP and Onapsis are urging corporations to complete a compromise assessment of apps, apply related patches, and address misconfigurations to stop unauthorized accessibility.
“The critical findings […] describe attacks on vulnerabilities with patches and safe configuration pointers out there for months and even many years,” Onapsis CEO Mariano Nunez explained. “Sad to say, too numerous businesses however operate with a important governance hole in terms of the cybersecurity and compliance of their mission-critical apps, making it possible for exterior and inner danger actors to entry, exfiltrate and get entire manage of their most delicate and regulated data and procedures.”
“Corporations that have not prioritized immediate mitigation for these regarded dangers should take into consideration their techniques compromised and take rapid and suitable action,” Nunez extra.
Located this article appealing? Comply with THN on Fb, Twitter and LinkedIn to study far more exceptional material we submit.
Some pieces of this article are sourced from:
thehackernews.com


 Hackers actively targeting unsecured SAP installs, DHS, SAP and Onapsis warn
Hackers actively targeting unsecured SAP installs, DHS, SAP and Onapsis warn