Scientists have found a new data-thieving trojan, which targets Android units with an onslaught of info-exfiltration abilities — from accumulating browser lookups to recording audio and phone phone calls.
Whilst malware on Android has previously taken the guise of copycat apps, which go beneath names related to legit pieces of software program, this innovative new destructive application masquerades itself as a Method Update application to choose manage of compromised devices.
“The adware makes a notification if the device’s display screen is off when it receives a command employing the Firebase messaging support,” Zimperium scientists reported in a Friday assessment. “The ‘Searching for update..’ is not a genuine notification from the operating procedure, but the spyware.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
When put in, the subtle spy ware marketing campaign sets about its job by registering the system with a Firebase command-and-manage (C2) server with data such as battery percentage, storage stats, and whether or not the phone has WhatsApp set up, adopted by amassing and exporting any facts of desire to the server in the kind of an encrypted ZIP file.
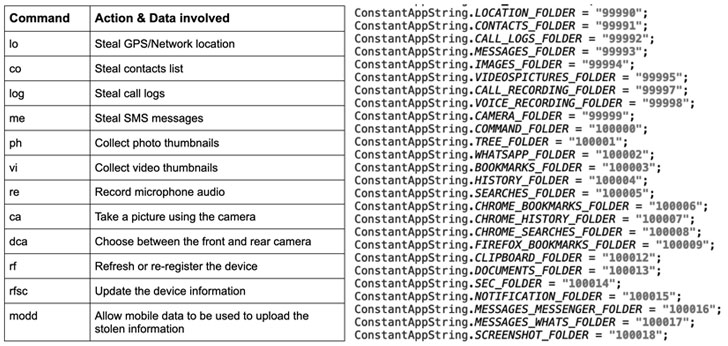
The adware characteristics myriad abilities with a focus on stealth, together with strategies to pilfer contacts, browser bookmarks, and research history, steal messages by abusing accessibility providers, file audio, and phone calls, and acquire pictures applying the phone’s cameras. It can also monitor the victim’s site, research for files with precise extensions, and seize knowledge from the device’s clipboard.
“The spyware’s performance and information exfiltration are induced beneath numerous situations, these as a new speak to included, new SMS received or, a new software mounted by producing use of Android’s contentObserver and Broadcast receivers,” the researchers claimed.
What is much more, the malware not only organizes the gathered info into a number of folders within its private storage, it also wipes out any trace of malicious exercise by deleting the ZIP data files as soon as it gets a “good results” concept from the C2 server publish exfiltration. In a additional bid to evade detection and fly less than the radar, the adware also minimizes its bandwidth usage by uploading thumbnails as opposed to the true visuals and videos existing in exterior storage.
Though the “Technique Update” app was hardly ever distributed by means of the formal Google Participate in Retail store, the investigate once yet again highlights how third-party application outlets can harbor harmful malware. The id of the malware authors, the specific victims, and the greatest motive driving the campaign remains unclear as however.
Uncovered this short article fascinating? Follow THN on Facebook, Twitter and LinkedIn to read through a lot more exclusive information we article.
Some areas of this short article are sourced from:
thehackernews.com


 Apple Issues Urgent Patch Update for Another Zero‑Day Under Attack
Apple Issues Urgent Patch Update for Another Zero‑Day Under Attack