Marvel has been entertaining us for the final 20 many years. We have witnessed gods, super-troopers, magicians, and other irradiated heroes struggle baddies at galactic scales. The everlasting combat of great versus evil. A very little bit like in cybersecurity, products fellas preventing cybercriminals.
If we select to go with this pleasurable analogy, is there anything useful we can master from people flicks?
Earth-ending baddies usually arrive with an army
When we observe the distinct Avenger videos, the very first issue we realize is that major baddies never fight alone. Consider Ultron and his bot military, Thanos or Loki with the Chitauri. They all arrive with large, generic clone proxy armies that heroes have to combat prior to finding to the ultimate manager.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
In the identical way, significant cyberattacks are planned and sent by arranged and structured teams of cybercriminals these types of as APT groups with often hundreds of associates. In genuine-life scenarios, attacks are coming from IPs (one particular or many) that have been stolen, hacked, or bought by the criminals. IPs are their faceless proxy army and if you want to get to the attackers, you need to have initially to burn off that IP military down.
So how to do that? You can fight them by yourself and most almost certainly fall short, or you can staff up with other superheroes as the Avengers do, and you might have a combating-again probability. The search term below is teaming up and leveraging collaboration or group intelligence.
Much more concretely, this usually means sharing details on attacks, for example. Most attacks depart traces in diverse techniques, service or application logs that can give indications on the attacker’s IPs and attack types. Sharing all those with other users can assistance remediation preventively if individuals IPs exhibit up on other people’s logs.
Think about this: Ultron’s minion IPs attack your server. Your IDS will detect their exercise in your logs, and if you have an efficient IPS, you might block those people IPs from executing even further injury. But how about you share those Ultron IPs with your neighbor? Or all other folks on Earth? How about all people today on Earth will preventively block those people IPs? Ultron’s military can not do any far more damage. All it can do now is prevent conquering Earth (or build a new military). But in any situation, you won. All this is because of the energy of the crowd.
Iron Man did not defeat Thanos by yourself
Let’s get a nearer appear at the Avenger’s group roster. You all know their names and respective powers. But did you think about how complementary they are? Hulk is the tank, Thor the large hitter. Cap is the strategist, and he can deliver some close problems if wanted. Iron Male is the range attack expert. Hawkeye is the hardly ever missing sniper. And Widow the perfect spy. They all bring distinctive capabilities and powers to the desk, producing the crew so effective (and great).
But back again to cybersecurity. There are a lot of resources out there that can help protect against attacks. Some may possibly be efficient in particular cases, but there is no one particular ring to rule them all (ooops, completely wrong universe 😉). An EDR solution can safeguard your endpoints but will not be useful to counter a DDoS. A SIEM instrument will help you centralize intelligence but will not help actively countering malicious action. An IDS will detect funky stuff ongoing in the logs but will not act upon them.
So like the Avengers, you require a group of answers that enjoy properly jointly and deal with as numerous scenarios as achievable. First, you will need to detect and act. Choose an IDS and an IPS. Combine it with a CTI to get third-party knowledge to enrich your menace databases. Insert some cybersecurity competencies to function competently. You get the most economical combo to counter threats.
Is it straightforward to put in motion? Well, it absolutely necessitates function. Interfacing individuals resources, generating absolutely sure the data is flowing proficiently between all those parts can be challenging but, at the finish, most satisfying.
From the Avengers to actual-lifetime heroes
Group intelligence and built-in alternative. This was the idea driving the generation of CrowdSec.
Cybersecurity is an uneven recreation with attackers normally obtaining the initiative, earning the problem tough to solve for most firms and people. You can toss money or technology at the issue, but absolutely nothing will promise its usefulness.
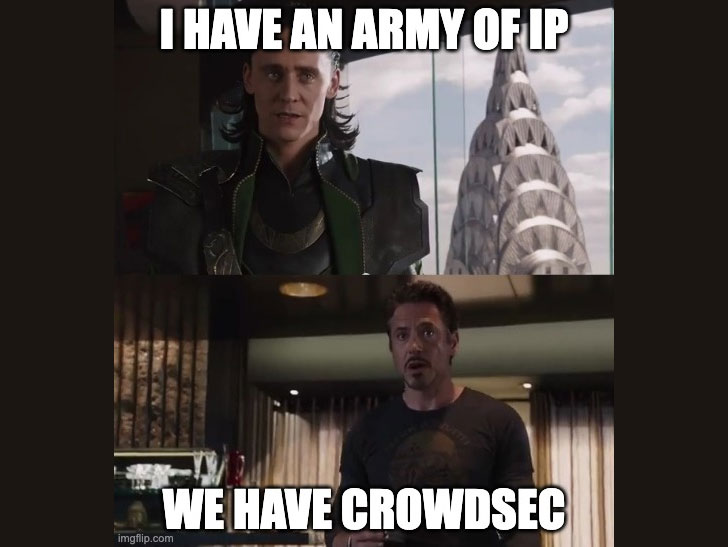
CrowdSec is proposing some thing new, a little something that has never been tried using before at this scale. A collaborative IPS and IDS that makes use of crowd intelligence to block attacks. Collaboration in between customers to produce a reputational and curated IP databases to make sure people are safeguarded in authentic-time versus Ultrons and Thanoses of this environment. In essence place, customers lead with signals – IP action flagged as suspicious: it can be something from brute power to credit rating card stuffing or scalping by DDoS – and regularly get an up to date blocklist of IPs that are to be “shot-at-sight” if they demonstrate up in logs. Assume, Waze of cybersecurity.
Attackers conceal guiding IPs. If we, as a neighborhood, can burn off people IPs, attackers will have no ammos still left and will back down.

If you want to be a part of the CrowdSec local community, check out out the official web site. Oh, and it truly is totally free and open up-resource!
Observed this posting interesting? Follow THN on Fb, Twitter and LinkedIn to study extra special content we put up.
Some elements of this article are sourced from:
thehackernews.com


 Researchers Detail Privilege Escalation Bugs Reported in Oracle VirtualBox
Researchers Detail Privilege Escalation Bugs Reported in Oracle VirtualBox