A now-patched superior-severity security vulnerability in WhatApp’s graphic filter attribute could have been abused to mail a malicious image in excess of the messaging app to examine delicate information and facts from the app’s memory.
Tracked as CVE-2020-1910 (CVSS score: 7.8), the flaw issues an out-of-bounds read through/write and stems from applying unique image filters to a rogue image and sending the altered graphic to an unwitting receiver, therefore enabling an attacker to entry important knowledge saved the app’s memory.
“A lacking bounds verify in WhatsApp for Android prior to v2.21.1.13 and WhatsApp Business for Android prior to v2.21.1.13 could have authorized out-of-bounds study and produce if a consumer utilized particular image filters to a specifically-crafted impression and despatched the ensuing graphic,” WhatsApp noted in its advisory published in February 2021.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
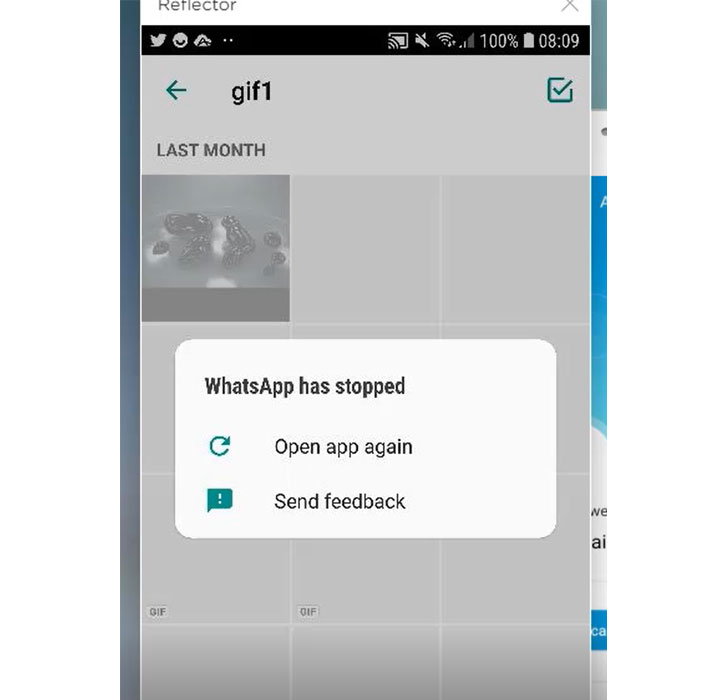
Cybersecurity organization Look at Issue Investigate, which disclosed the issue to the Facebook-owned platform on November 10, 2020, claimed it was in a position to crash WhatsApp by switching involving different filters on the destructive GIF documents.
Precisely, the issue was rooted in an “applyFilterIntoBuffer()” functionality that handles graphic filters, which will take the resource picture, applies the filter chosen by the consumer, and copies the outcome into the location buffer. By reverse-engineering the “libwhatsapp.so” library, the researchers identified that the vulnerable perform relied on the assumption that equally the supply and filtered visuals have the exact dimensions and also the identical RGBA coloration format.
Given that every RGBA pixel is stored as 4 bytes, a destructive graphic getting only 1 byte for every pixel can be exploited to attain an out-of-bounds memory obtain due to the fact the “functionality attempts to read through and duplicate 4 situations the quantity of the allocated supply impression buffer.”
WhatsApp explained it has “no purpose to imagine customers would have been impacted by this bug.” Since WhatsApp model 2.21.1.13, the enterprise has included two new checks on the supply impression and filter picture that make certain that the two source and filter illustrations or photos are in RGBA structure and that the impression has 4 bytes for every pixel to reduce unauthorized reads.
Located this post appealing? Observe THN on Fb, Twitter and LinkedIn to read more unique content material we submit.
Some components of this write-up are sourced from:
thehackernews.com


 Bad Bots Focus Attacks on E-Commerce Targets
Bad Bots Focus Attacks on E-Commerce Targets