Microsoft on Wednesday disclosed specifics of a focusing on phishing campaign that leveraged a now-patched zero-day flaw in its MSHTML system using specifically-crafted Business files to deploy Cobalt Strike Beacon on compromised Windows systems.
“These attacks utilised the vulnerability, tracked as CVE-2021-40444, as part of an preliminary obtain campaign that distributed custom made Cobalt Strike Beacon loaders,” Microsoft Threat Intelligence Middle said in a specialized create-up. “These loaders communicated with an infrastructure that Microsoft associates with a number of cybercriminal strategies, which includes human-operated ransomware.”
Facts about CVE-2021-40444 (CVSS score: 8.8) initially emerged on September 7 soon after scientists from EXPMON alerted the Windows maker about a “extremely advanced zero-day attack” aimed at Microsoft Office end users by using edge of a remote code execution vulnerability in MSHTML (aka Trident), a proprietary browser engine for the now-discontinued Internet Explorer and which is utilised in Office environment to render web written content inside of Term, Excel, and PowerPoint files.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“The noticed attack vector relies on a destructive ActiveX management that could be loaded by the browser rendering motor working with a destructive Business document,” the scientists noted. Microsoft has since rolled out a correct for the vulnerability as element of its Patch Tuesday updates a week afterwards on September 14.
The organization attributed the pursuits to related cybercriminal clusters it tracks as DEV-0413 and DEV-0365, the latter of which is the company’s moniker for the emerging risk team involved with generating and taking care of the Cobalt Strike infrastructure utilized in the attacks. The earliest exploitation attempt by DEV-0413 dates back to August 18.
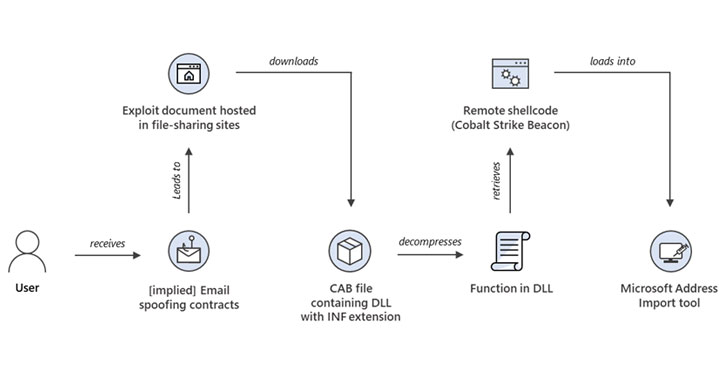
The exploit shipping and delivery system originates from e-mail impersonating contracts and legal agreements hosted on file-sharing internet sites. Opening the malware-laced document prospects to the obtain of a Cabinet archive file containing a DLL bearing an INF file extension that, when decompressed, prospects to the execution of a function in that DLL. The DLL, in flip, retrieves remotely hosted shellcode — a custom made Cobalt Strike Beacon loader — and hundreds it into the Microsoft handle import device.
Moreover, Microsoft mentioned some of the infrastructures that was utilized by DEV-0413 to host the destructive artifacts had been also included in the supply of BazaLoader and Trickbot payloads, a independent established of actions the enterprise monitors below the codename DEV-0193 (and by Mandiant as UNC1878).
“At minimum a single organization that was productively compromised by DEV-0413 in their August marketing campaign was earlier compromised by a wave of likewise-themed malware that interacted with DEV-0365 infrastructure almost two months ahead of the CVE-2021-40444 attack,” the researchers explained. “It is at present not recognised regardless of whether the retargeting of this corporation was intentional, but it reinforces the relationship concerning DEV-0413 and DEV-0365 over and above sharing of infrastructure.”
Discovered this short article interesting? Adhere to THN on Facebook, Twitter and LinkedIn to read far more unique information we put up.
Some elements of this post are sourced from:
thehackernews.com

 You Can Now Sign-in to Your Microsoft Accounts Without a Password
You Can Now Sign-in to Your Microsoft Accounts Without a Password