Shutterstock
A new form of Android malware has been identified in an application on Google Participate in that can unfold itself utilizing phony WhatsApp messages.
Examine Level Research made the discovery and observed that if a consumer downloaded the pretend application and gave it the acceptable permissions, the malware would be able of automatically replying to the victims’ incoming WhatsApp messages with a payload obtained from a command-and-command (C&C) server.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“This exclusive strategy could have enabled menace actors to distribute phishing attacks, spread fake information or steal qualifications and facts from users’ WhatsApp accounts, and additional,” stated the cyber security researchers.
The malware could ship even more destructive written content by way of automated replies to incoming WhatsApp messages.
The scientists observed the malware concealed in an application referred to as “FlixOnline” which is a fake provider that statements to let people to perspective Netflix written content from all-around the earth on their cellular.
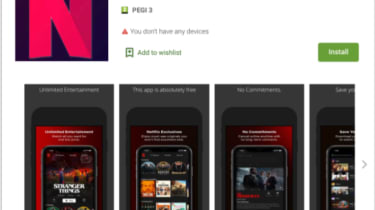
“However, as an alternative of allowing the cellular user to watch Netflix content material, the software is in fact developed to monitor the user’s WhatsApp notifications, and to send out computerized replies to the user’s incoming messages employing content that it gets from a distant command and regulate (C&C) server,” said CPR.
The malware sends this concept to its victims, and lures them with an offer of a free of charge Netflix assistance: “2 Months of Netflix Premium No cost at no cost For Cause OF QUARANTINE (CORONA VIRUS)* Get 2 Months of Netflix High quality Free everywhere in the planet for 60 times. Get it now Below https://bit[.]ly/3bDmzUw.”
Verify Issue reported that with this technique, a threat actor could carry out a broad selection of destructive functions like spreading further malware, stealing facts from users’ WhatsApp accounts and extorting end users by threatening to ship sensitive WhatsApp details or conversations to all of their contacts.
When the application is downloaded and installed, it requests permissions for “Overlay”, “Battery Optimization Ignore” and “Notifications”.
Overlay lets the application to develop new windows on leading of other programs, normally asked for to make a bogus “login” display screen for other applications in purchase to steal the victim’s credentials. The Battery Optimization authorization stops the malware from being shut down by the device’s battery optimization regime. And lastly, while Notification accessibility permits the malware to access all notifications related to messages sent to the product and grants the means to automatically “dismiss” and “reply” to the messages.
Once Verify Point had found the malware, it documented it to Google who promptly removed the application from the Engage in Retailer. “Over the training course of two months, the “FlixOnline” application was downloaded close to 500 occasions,” reported CPR.
Malware is also spreading on other platforms, like LinkedIn where by the Golden Chicken hacking team is targeting its people with phony job features to infect them with a malware strain that granted them entry to victims’ desktops.
Some elements of this write-up are sourced from:
www.itpro.co.uk


 Wormable Netflix Malware Spreads Via WhatsApp Messages
Wormable Netflix Malware Spreads Via WhatsApp Messages