Large-profile corporations and neighborhood governments positioned largely in Asia are the topics of targeted attacks by a formerly undocumented espionage team dubbed Worok that has been active considering the fact that late 2020.
“Worok’s toolset includes a C++ loader CLRLoad, a PowerShell backdoor PowHeartBeat, and a C# loader PNGLoad that uses steganography to extract concealed destructive payloads from PNG documents,” ESET researcher Thibaut Passilly stated in a new report revealed right now.
Worok is reported to share overlaps in instruments and passions with a different adversarial collective tracked as TA428, with the group joined to attacks in opposition to entities spanning energy, money, maritime, and telecom sectors in Asia as perfectly as a government agency in the Center East and a private business in southern Africa.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Malicious activities undertaken by the group professional a obvious break from Could 2021 to January 2022, prior to resuming the up coming month. The Slovak cybersecurity organization assessed the group’s objectives to be aligned with facts theft.
Preliminary foothold to focus on networks by means of 2021 and 2022 entailed the use of ProxyShell exploits in select occasions, followed by deploying further custom made backdoors for entrenched obtain. Other preliminary compromise routes are mysterious as however.
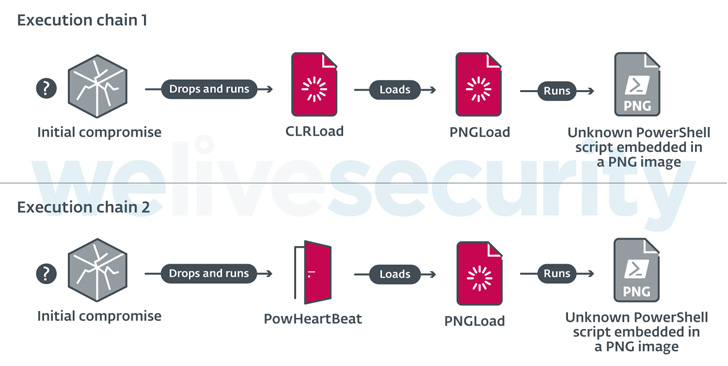
Among the the applications in Worok’s malware arsenal is a very first-stage loader termed CLRLoad, which is succeeded by a .NET-based mostly steganographic loader codenamed PNGLoad that is capable of executing an unfamiliar PowerShell script embedded in a PNG graphic file.
Infection chains in 2022 have since dropped CLRLoad in favor of a entire-highlighted PowerShell implant referred to as PowHeartBeat that is subsequently employed to launch PNGLoad, in addition to communicating with a distant server by way of HTTP or ICMP to execute arbitrary commands, send out and receive documents, and carry out connected file operations.

ESET explained it was not able to retrieve any of the last-stage PNG payloads, despite the fact that it’s suspected that the malware could be concealed in legitimate, innocuous-wanting PNG photographs and thus “disguise in plain sight” with no attracting interest.
“Worok is a cyber espionage group that develops its own tools, as perfectly as leveraging existing equipment, to compromise its targets,” Passilly reported.
“Thieving information and facts from their victims is what we believe the operators are after simply because they concentrate on superior-profile entities in Asia and Africa, focusing on various sectors, both personal and general public, but with a certain emphasis on federal government entities.”
Discovered this article appealing? Observe THN on Facebook, Twitter and LinkedIn to go through a lot more exceptional content we post.
Some elements of this write-up are sourced from:
thehackernews.com


 Half of Firms Report Supply Chain Ransomware Compromise
Half of Firms Report Supply Chain Ransomware Compromise