Security flaws have been identified in Xiaomi Redmi Observe 9T and Redmi Be aware 11 products, which could be exploited to disable the cell payment mechanism and even forge transactions by using a rogue Android application put in on the units.
Look at Level stated it identified the flaws in units powered by MediaTek chipsets all through a security examination of the Chinese handset maker’s “Kinibi” Trustworthy Execution Surroundings (TEE).
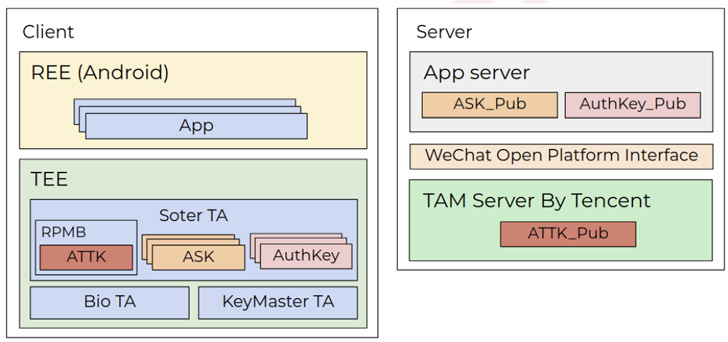
A TEE refers to a secure enclave inside the primary processor that’s made use of to system and store sensitive data these types of as cryptographic keys so as to be certain confidentiality and integrity.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

Specifically, the Israeli cybersecurity business found out that a dependable application on a Xiaomi system can be downgraded thanks to a lack of variation manage, enabling an attacker to substitute a more recent, secure model of an application with an more mature, vulnerable variant.
“As a result, an attacker can bypass security fixes manufactured by Xiaomi or MediaTek in reliable applications by downgrading them to unpatched versions,” Check out Position researcher Slava Makkaveev mentioned in a report shared with The Hacker News.
Also, various vulnerabilities have been discovered in “thhadmin,” a dependable app that’s responsible for security administration, which could be abused by a destructive app to leak stored keys or to execute arbitrary code in the context of the app.
“We learned a set of vulnerabilities that could enable forging of payment deals or disabling the payment technique right from an unprivileged Android application,” Makkaveev explained in a assertion shared with The Hacker Information.
The weaknesses get aim at a dependable application designed by Xiaomi to carry out cryptographic functions connected to a company named Tencent Soter, which is a “biometric conventional” that features as an embedded mobile payment framework to authorize transactions on third-party apps utilizing WeChat and Alipay.

But a heap overflow vulnerability in the soter dependable app intended that it could be exploited to induce a denial-of-service by an Android application that has no permissions to converse with the TEE immediately.
That is not all. By chaining the aforementioned downgrade attack to exchange the soter reliable app to an more mature edition that contained an arbitrary study vulnerability, Test Stage discovered it was doable to extract the private keys utilized to indication payment packages.
“The vulnerability […] totally compromises the Tencent soter system, enabling an unauthorized user to indicator bogus payment packages,” the enterprise observed.
Xiaomi, following accountable disclosure, has rolled out patches to handle CVE-2020-14125 on June 6, 2022. “The downgrade issue, which has been confirmed by Xiaomi to belong to a third-party vendor, is being fixed,” Look at Issue added.
Found this short article interesting? Adhere to THN on Fb, Twitter and LinkedIn to browse more special articles we put up.
Some sections of this posting are sourced from:
thehackernews.com


 #BHUSA : Failure to Challenge is a Social Engineering Risk
#BHUSA : Failure to Challenge is a Social Engineering Risk