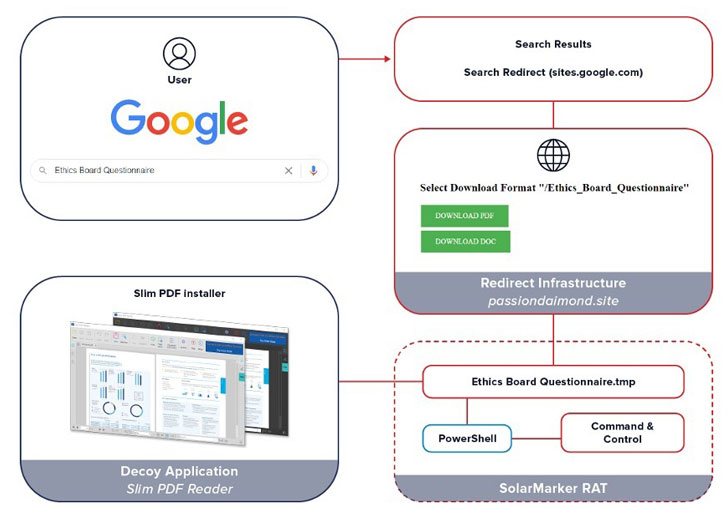
Cybercriminals are resorting to research engine poisoning approaches to entice small business pros into seemingly legit Google internet sites that put in a Distant Obtain Trojan (RAT) capable of carrying out a wide range of attacks.
The attack will work by leveraging queries for enterprise kinds such as invoices, templates, questionnaires, and receipts as a stepping stone toward infiltrating the devices. People attempting to download the alleged doc templates are redirected, with out their knowledge, to a malicious internet site that hosts the malware.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
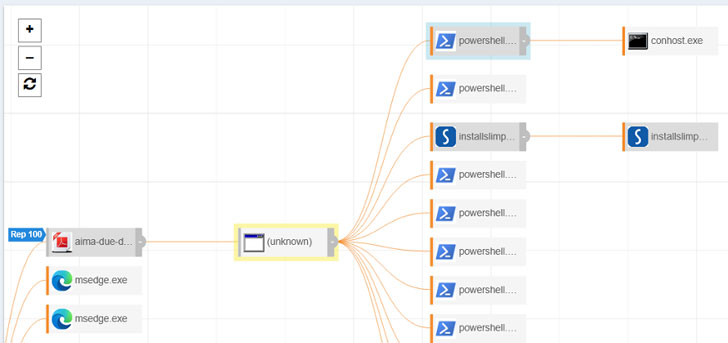
“The moment the RAT is on the victim’s laptop or computer and activated, the danger actors can deliver commands and upload supplemental malware to the contaminated technique, these types of as ransomware, a credential stealer, a banking trojan, or merely use the RAT as a foothold into the victim’s network,” researchers from eSentire claimed in a create-up published on Tuesday.
The cybersecurity company stated it discovered about 100,000 distinctive web web pages that include preferred small business phrases or keyword phrases this kind of as template, bill, receipt, questionnaire, and resume, thus letting the web pages to be ranked bigger on the lookup results, and hence, raising the chance of achievements.

When a sufferer lands on the attacker-managed internet site and downloads the document remaining searched for, it results in being an entry stage for far more refined threats, ultimately ensuing in the installation of a .NET-primarily based RAT named SolarMarker (aka Yellow Cockatoo, Jupyter, and Polazert).
In 1 circumstance investigated by eSentire, which included an staff of a fiscal management organization, the malware executable was disguised as a PDF document that, when launched, deployed the RAT alongside with a genuine edition of Slim PDF as a decoy.
“Another troubling factor of this campaign is that the SolarMarker team has populated many of their destructive web internet pages with key terms relating to economic files,” stated Spence Hutchinson, eSentire’s manager of risk intelligence.
“A economical cybercrime team would think about an worker, operating in the finance office of a firm, or an worker, doing work for a economic organization, a superior price concentrate on. Regrettably, after a RAT is easily installed, the prospective fraud actions are various.”
Uncovered this post interesting? Observe THN on Fb, Twitter and LinkedIn to read extra distinctive written content we put up.
Some sections of this article are sourced from:
thehackernews.com


 Global Attacker Dwell Time Drops to Just 24 Days
Global Attacker Dwell Time Drops to Just 24 Days