LockBit made available Accenture’s purported databases and made a requisite jab at its purportedly unhappy security. Accenture claims it recovered just high-quality from backups.
The LockBit ransomware-as-a-company (RaaS) gang has printed the identify and symbol of what is purportedly a person of its latest victims: Accenture, the world wide business enterprise consulting company with an insider monitor on some of the world’s biggest, most highly effective providers.
Accenture’s customers involve 91 of the Fortune Global 100 and much more than 3-quarters of the Fortune World-wide 500. In accordance to its 2020 once-a-year report, that contains e-commerce giant Alibaba, Cisco and Google. Valued at $44.3 billion, Accenture is one of the world’s largest tech consultancy companies: It employs all around 569,000 individuals across 50 nations around the world.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
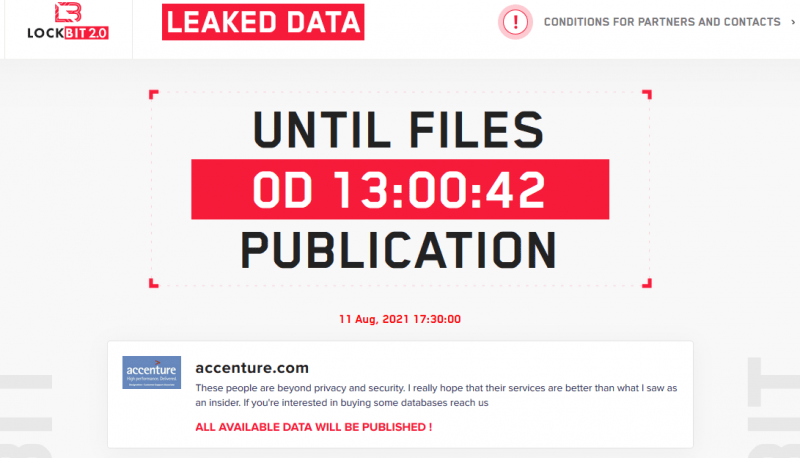
In a put up on its Dark Web internet site, LockBit provided up Accenture databases for sale, together with a requisite jab at what the gang considered to be Accenture’s pathetic security.
“These men and women are past privacy and security. I really hope that their expert services are better than what I saw as an insider. If you are intrigued in buying some databases, reach us.”
—LockBit website post.
LockBit dark-web internet site display seize. Source: Cybereason.
According to Security Affairs, at the conclude of a ransom payment clock’s countdown, a leak web page confirmed a folder named W1 that incorporates a selection of PDF documents allegedly stolen from the business. LockBit operators claimed to have gained entry to Accenture’s network and have been getting ready to leak documents stolen from Accenture’s servers at 17:30:00 GMT.
LockBit countdown clock. Source: Cyble.
The information hit the headlines late Wednesday early morning Eastern Time, following CNBC reporter Eamon Javers tweeted about the gang’s assert that it would be releasing information in coming hrs and that it was supplying to offer insider Accenture details to interested functions.
A hacker team applying Lockbit Ransomware claims they have hacked the consulting firm Accenture and will release info in several hours, CNBC has figured out. They are also giving to provide insider Accenture details to fascinated functions.
— Eamon Javers (@EamonJavers) August 11, 2021
Blessed Be the Backups
Of course, we were strike, but we’re A-Okay now, Accenture confirmed: “Through our security controls and protocols, we determined irregular exercise in a person of our environments. We straight away contained the issue and isolated the afflicted servers,” it mentioned in a assertion. “We completely restored our afflicted units from backup, and there was no effects on Accenture’s operations, or on our clients’ systems.”
According to BleepingComputer, the group that threatened to publish Accenture’s facts – allegedly stolen throughout a the latest cyberattack – is recognised as LockBit 2..
As described by Cybereason’s Tony Bradley in a Wednesday post, the LockBit gang is comparable to its RaaS brethren DarkSide and REvil: Like all those other operations. LockBit makes use of an affiliate design to rent out its ransomware system, taking a reduce of any ransom payments that outcome.
Bradley pointed out that the LockBit gang is seemingly on a choosing spree in the wake of DarkSide and REvil both equally shutting down functions. “The wallpaper displayed on compromised techniques now includes text inviting insiders to support compromise systems – promising payouts of millions of bucks,” Bradley wrote, referring to a new BleepingComputer report about LockBit actively recruiting insiders to assist them breach and encrypt networks.
Insider Task?
Cyble researchers suggested in a Tweet stream that this could be an insider career. “We know #LockBit #threatactor has been employing corporate employees to get accessibility to their targets’ networks,” the company tweeted, along with a clock counting down how significantly time was left for Accenture to cough up the ransom.
Potential insider position? We know #LockBit #threatactor has been selecting corporate staff to obtain entry to their targets’ networks.#ransomware #cyber #cybersecurity #infosec #accenture pic.twitter.com/ZierqRVIjj
— Cyble (@AuCyble) August 11, 2021
Cyble reported that LockBit claimed to have manufactured off with databases of around 6TB and that it demanded $50 million as ransom. The danger actors them selves alleged that this was an insider career, “by a person who is still employed there,” even though Cyble referred to as that “unlikely.”
Sources acquainted with the attack told BleepingComputer that Accenture verified the ransomware attack to at least a single personal computer telephony integration (CTI) seller and that it’s in the system of notifying extra prospects. In accordance to a tweet from menace intelligence firm Hudson Rock, the attack compromised 2,500 personal computers used by personnel and associates, leading the business to recommend that “this facts was definitely utilized by threat actors.”
In a security inform issued past week, the Australian Cyber Security Centre (ACSC) warned that LockBit 2. ransomware attacks against Australian companies experienced started out to increase past month, and that they have been coupled with threats to publish knowledge in what is regarded as double-extortion attacks. “This activity has happened throughout many market sectors,” according to the notify. “Victims have obtained requires for ransom payments. In addition to the encryption of facts, victims have obtained threats that facts stolen in the course of the incidents will be posted.”
The ACSC noted (PDF) that it is just lately noticed LockBit menace actors actively exploiting current vulnerabilities in the Fortinet FortiOS and FortiProxy solutions, recognized as CVE-2018-13379, in buy to attain first obtain to distinct sufferer networks. That vulnerability, a route-traversal flaw in the SSL VPN, has been exploited in multiple attacks around the decades:
In April, the FBI and the Cybersecurity and Infrastructure Security Company (CISA) warned that highly developed persistent danger (APT) country-state actors ended up actively exploiting it to acquire a foothold within just networks right before shifting laterally and carrying out recon, for case in point.
Recognized Vulnerability Exploited?
Ron Bradley, vice president of 3rd-party risk-administration business Shared Assessments, instructed Threatpost on Wednesday that the Accenture incident is “a key example of the distinction involving business resiliency and company continuity. Small business resiliency is like remaining in a boxing match, you consider a body blow but can continue on the battle. Company continuity comes into participate in when operations have ceased or severely impaired and you have to make major initiatives to recuperate.
“This individual illustration with Accenture is exciting in the simple fact that it was a identified/published vulnerability,” Bradley continued. It highlights the worth of making confident systems are correctly patched in a well timed fashion. The skill for Accenture to take care of the repercussions of most likely stolen info will be an critical lesson for quite a few corporations heading forward.”
Hitesh Sheth, president and CEO at the cybersecurity organization Vectra mentioned that all businesses should really anticipate attacks like this, but significantly a international consultancy agency with back links to so many companies. “First reviews counsel Accenture had facts backup protocols in put and moved immediately to isolate impacted servers,” he advised Threatpost on Wednesday. “It’s also soon for an exterior observer to evaluate harm. Nonetheless, this is yet a different reminder to corporations to scrutinize security benchmarks at their distributors, associates, and suppliers. Every business should hope attacks like this – probably primarily a worldwide consulting company with inbound links to so many other businesses. It is how you foresee, plan for and recuperate from attacks that counts.”
Anxious about in which the upcoming attack is coming from? We’ve obtained your again. Sign-up NOW for our future dwell webinar, How to Believe Like a Menace Actor, in partnership with Uptycs on Aug. 17 at 11 AM EST and find out specifically where attackers are targeting you and how to get there very first. Be a part of host Becky Bracken and Uptycs scientists Amit Malik and Ashwin Vamshi on Aug. 17 at 11AM EST for this Live dialogue.
Some pieces of this write-up are sourced from:
threatpost.com

 Prison for Software Firm Fraudster
Prison for Software Firm Fraudster