A new ‘fork’ of the Cerberus banking trojan, known as Alien, targets victims’ credentials from extra than 200 cell applications, together with Lender of The united states and Microsoft Outlook.
A freshly uncovered banking trojan known as Alien is invading Android gadgets all over the world, using an state-of-the-art potential to bypass two-aspect authentication (2FA) security steps to steal sufferer credentials.
At the time it has contaminated a device, the RAT aims to steal passwords from at the very least 226 cellular apps – including banking apps like Financial institution of America Cellular Banking and Cash A person Cell, as nicely as a slew of collaboration and social apps like Snapchat, Telegram and Microsoft Outlook.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The malware, which was to start with marketed for hire on underground boards in January, has been used to actively target establishments all over the world, which include Australia, France, Germany, Italy, Poland, Spain, Turkey, the U.K. and the United States. Scientists consider Alien is a “fork” of the infamous Cerberus banking malware, which has gone through a continuous demise in use around the past calendar year.

“Based on our in-depth information of the trojan, we can establish that the Alien malware is a fork of the preliminary variant of Cerberus (v1), active since early January 2020 and rented out at the identical time as Cerberus,” explained scientists with ThreatFabric, in a Thursday analysis. “Cerberus remaining discontinued, its buyers seem to be to be switching to Alien, which has become the well known new MaaS [malware as a service] for fraudsters.”
Alien Malware
The Alien RAT has various normally utilized Android malware capabilities, which includes the means to start overlay attacks, manage and steal SMS messages and harvest make contact with lists – as effectively as keylogging, location-amassing and other abilities.
On the other hand, it also touts a number of extra superior tactics, such as a notification sniffer that allows it to obtain all new updates on infected devices. This features 2FA codes – enabling the malware to bypass 2FA security steps.
Alien leverages this tactic by abusing the “android.authorization.BIND_NOTIFICATION_LISTENER_SERVICE” to get the information of standing bar notifications on the infected system. Although normally the user would need to grant this authorization manually in the configurations, the malware circumvents this roadblock by employing the Accessibility privileges on Android devices, performing all needed user interactions by itself.

Countries qualified by Alien malware. Simply click to enlarge. Credit history: ThreatFabric
It does this working with an highly developed remote accessibility function that abuses the TeamViewer software, providing the bad actor at the rear of the malware remote management over the victim’s equipment. TeamViewer is a proprietary program application utilised for distant command, desktop sharing and on line meetings.
“When TeamViewer is efficiently activated, it gives the actors with whole remote manage of the device’s user interface, enabling them to access and transform product options, install and take away apps, but also to use any application mounted on the gadget (financial institution programs, messengers and social networks),” reported scientists. “By monitoring the machine in authentic-time, actors can also gain worthwhile insight into the user’s actions.”
It’s unclear how Alien is at first unfold, but given that the malware is becoming rented out, several various initial attack vector practices can be utilized, which include spear-phishing, distribution by way of 3rd-social gathering programs and more.
Connection to Cerberus
Cerberus meanwhile first emerged last August on underground forums, provided in a MaaS rental design. At the time it was introduced as a common banking trojan. As not too long ago as July, the malware was uncovered in a malicious Android app on the Google Participate in app marketplace, which had 10,000 downloads.
On the other hand, above the earlier 12 months a slew of specialized issues transpired that led to unhappy customers. The authors of Cerberus consequently decided to conclude the rental provider and refund energetic license holders. On August 10, the malware author shared the supply code of the trojan to the standard public.
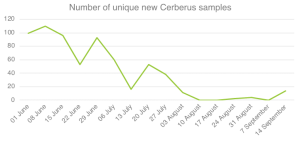
The decrease of Cerberus in 2020. Credit history: ThreatFabric
In the meantime, scientists claimed that in February they commenced looking at simultaneous campaigns working with each trojans – nevertheless, it appeared that the new Alien malware was operated separately and was a little diverse from Cerberus.
The most significant change involving the two samples is Alien’s 2FA-thieving technique, a characteristic that Cerberus lacked, they explained. A further distinct element of Alien is its RAT capability, which has been implemented independently from the major command handler, working with different command-and-command (C2) endpoints.
“Looking at what we know now about what happened with Cerberus and Alien, we could speculate that Cerberus was on the decrease as the builders guiding the trojan shifted absent from the job with the authentic source in purchase to commence their individual,” researchers explained.
Following Ways
Researchers point to this backlink in between Cerberus and Alien as a pattern in the risk landscape to carry on to glance out for. They predicted that a lot more new malware family members, dependent on Cerberus, will emerge in the past quarter of 2020. When it comes to Alien particularly, searching ahead, scientists stated that they be expecting the malware’s authors to constantly improve its remote-accessibility functionality.
“They could also build an ATS [automatic transfer system] function to automate the fraud system,” reported scientists. “What can be deemed for granted is that the quantity of new banking trojans will only carry on rising, many embedding new and enhanced features to improve the good results fee of fraud.”
Researchers urge all financial institutions to recognize their recent and long term menace publicity and for that reason employ the appropriate detection and handle mechanisms.
“The most vital factor to just take care of is securing the on the web banking channels, generating fraud difficult to complete, discouraging criminals to attempt the attacks and generating it significantly less useful for them to build a lot more malware,” they wrote.
Some parts of this article is sourced from:
threatpost.com


 Shopify breach: Help center employees are a unique breed of insider threat
Shopify breach: Help center employees are a unique breed of insider threat