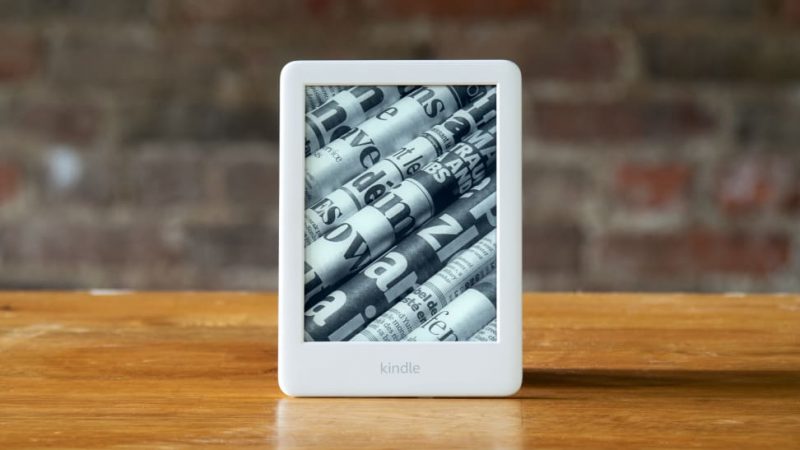
The “KindleDrip” attack would have allowed attackers to siphon money from unsuspecting victims.
3 vulnerabilities in the Amazon Kindle e-reader would have authorized a remote attacker to execute code and operate it as root – paving the way for siphoning dollars from unsuspecting customers.
Yogev Bar-On, researcher at Realmode Labs, identified that it was attainable to email destructive e-textbooks to the units by using the “Send to Kindle” element to commence a chain of attack – a discovery that earned him $18,000 from the Amazon bug-bounty software.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“The initial vulnerability permitted an attacker to mail an e-e-book to the victim’s Kindle unit,” he explained in a Thursday posting. “Then, the second vulnerability was applied to operate arbitrary code even though the e-reserve is parsed, under the context of a weak person. The 3rd vulnerability makes it possible for the attacker to escalate privileges and run code as root.”
To make the attack perform (which the researcher calls KindleDrip), an attacker would initial need to have to know the email handle assigned to the victim’s machine. There’s also a predefined listing of authorised e-mails that any e-books would have to have to be despatched from. In accordance to Bar-On, neither necessity is considerably of a hurdle.
The distinctive vacation spot email deal with assigned by Amazon is normally just the user’s standard email underneath the kindle.com domain (e.g. [email protected] gets to be [email protected]), which “can be brute compelled,” he stated.
And as for the checklist of accredited addresses, spoofing can easily get all-around this. “Email authentication is nonetheless not as widespread as you may well imagine,” he wrote. “Since numerous email servers nonetheless really don’t help authentication, it is not unreasonable to presume that Amazon will not confirm the authenticity of the sender.” And certainly, he was able to spoof an email information to ship an e-book to his own unit.
The KindleDrip Attack
With the emails sorted, the very first step in a KindleDrip attack is to send out a destructive e-reserve to a concentrate on. The file is despatched as an attachment and routinely reveals up in a user’s library. Even so, the sufferer doesn’t obtain an notify that one thing new has been mounted in the bookshelf.
“To make issues worse, there is no sign that the e-reserve was acquired from an email concept,” reported Bar-On. “It also appeared on the house web site of the Kindle with a go over picture of our alternative, which would make phishing attacks a lot much easier.”
Then, the sufferer enters the harmless-looking e book and touches one particular of the links in the desk of contents. The backlink opens the created-in browser with an HTML website page that is made up of a malicious JPEG XR graphic.
The graphic is parsed, and malicious code now runs as root. The payload changes the boot background and restarts the unit. Then, the attacker receives non-public qualifications from the machine and can log into the victim’s account.
Technical Aspects
To booby-lure the e-reserve with destructive code, the researcher located that the Kindle web browser supports the use of an obscure picture structure named JPEG XR. Conveniently, the Kindle by itself has a firmware library known as libjpegXR.so, which parses JPEG XR.
He located that it was feasible to trigger a buffer overflow whilst parsing JPEG XR with the Kindle, with controlled bytes from an JPEG XR image file.
Quickly pursuing the overflowed buffer, there is a pointer struct jxr_tile_qp *tile_quant. Bar-On observed that applying the overflow, the pointer could be overridden to be able to compose info to an attacker-controlled address – what’s identified as an absolute-produce primitive.
“Using the complete-write primitive, a shellcode could be published to the executable segment,” he spelled out. “Then, the primitive could be made use of once more to ‘spray’ the Global Offset Table (Received) with the handle of the shellcode. The mesquite process is multi-threaded, so a person of the other threads would inevitably contact a functionality from the Received, causing the shellcode to execute.”
With code executed, the third action in the attack is privilege escalation.
“The mesquite approach is run underneath chroot with a weak person identified as framework,” he wrote. “So the prior vulnerability couldn’t be utilised to even reboot the product. Privilege escalation was necessary.”
In seeking for root processes that hear on a regional socket, he uncovered some thing termed stackdumpd.
“This approach is dependable for generating stack dumps of crashed procedures,” he explained. “It receives info like the crashed approach id and thread id, and passes it to /usr/bin/dump-stack. This is a shell script that connects to the crashed process with GDB…and like the title indicates, dumps the stack.”
GDB is a distant debugger. He identified that it can operate arbitrary commands given in the command argument, and so could be utilized to run arbitrary code as root. There are two security checks prior to one particular is ready to do so, which can be bypassed with a “simple string,” he explained. “Thus, we experienced a vulnerability that authorized us to execute arbitrary code less than the context of the root person.”
The 3 issues chained together makes it possible for root RCE on a vulnerable Kindle, as shown in a evidence-of-concept online video:
Armed with this attack, a menace actor can snoop on users’ web classes, steal credentials – or, far more worryingly, can steal income from the victim. To siphon hard cash, the attacker could publish an e-e-book and then log into the victim’s account, making use of their saved credit history card to get it.
The attack will work on Kindles with firmware model 5.13.2 or under Amazon fastened KindleDrip in the most up-to-date update, firmware variation 5.13.4.
“Using a few distinct vulnerabilities, I managed to execute arbitrary code on the Amazon Kindle as the root consumer, specified only the email deal with assigned to the machine,” claimed Bar-On. “This could have authorized an attacker to access gadget credentials and make purchases on the Kindle retail outlet. This could also have been utilized to jailbreak the most recent Kindle units. Amazon took the report significantly and set the issues in a reasonable time.”
Download our exclusive Free Threatpost Insider E-book Health care Security Woes Balloon in a Covid-Era Globe, sponsored by ZeroNorth, to master additional about what these security threats imply for hospitals at the day-to-working day amount and how healthcare security teams can implement best tactics to protect providers and clients. Get the entire story and Down load the Ebook now – on us!
Some components of this short article are sourced from:
threatpost.com

 New Cyber-attack Advice for European Hospitals
New Cyber-attack Advice for European Hospitals