The open up-resource job has rolled out a security deal with for CVE-2021-41773, for which general public cyberattack exploit code is circulating.
Apache Computer software has promptly issued a fix for a zero-day security bug in the Apache HTTP Server, which was initial claimed to the venture final week. The vulnerability is under active exploitation in the wild, it reported, and could allow for attackers to accessibility delicate info.
In accordance to a security advisory issued on Monday, the issue (CVE-2021-41773) could enable path traversal and subsequent file disclosure. Path traversal issues let unauthorized persons to access files on a web server, by tricking possibly the web server or the web application working on it into returning data files that exist outdoors of the web root folder.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

In this situation, the issue has an effect on only model 2.4.49 of Apache’s open-supply web server, which presents cross-platform operability with all modern functioning units, like UNIX and Windows.
“A flaw was identified in a modify created to path normalization in Apache HTTP Server 2.4.49,” according to the advisory. “An attacker could use a route-traversal attack to map URLs to information exterior the envisioned document root. If data files outside the house of the document root are not shielded by ‘require all denied,’ these requests can do well.”
The bug could also expose the resource of interpreted files like CGI scripts, the advisory additional, which which might have sensitive information that attackers can exploit for further more attacks.
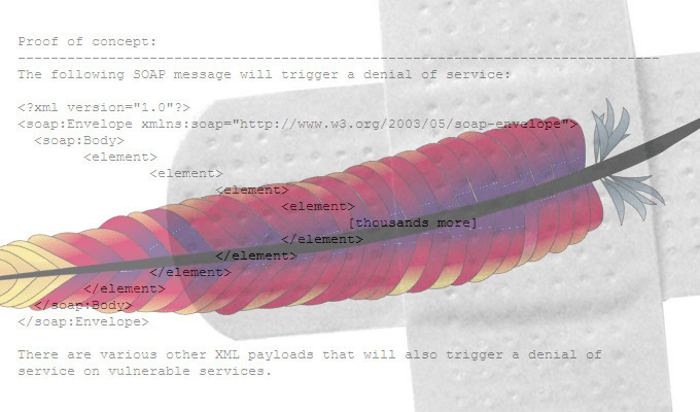
Researchers these kinds of as the offensive workforce at Positive Systems promptly designed evidence-of-notion exploits verifying the attack route, so expect a lot more attack avenues to be availably publicly shortly:
🔥 We have reproduced the contemporary CVE-2021-41773 Route Traversal vulnerability in Apache 2.4.49.
If information exterior of the document root are not safeguarded by “require all denied” these requests can thrive.
Patch ASAP! https://t.co/6JrbayDbqG pic.twitter.com/AnsaJszPTE
— PT SWARM (@ptswarm) Oct 5, 2021
Tenable famous that a Shodan search on Tuesday turned up about 112,000 Apache HTTP Servers that are verified to be managing the vulnerable version, like 43,000 or so in the U.S.
“However, other vulnerable web servers may well be configured to not exhibit version details,” in accordance to the firm’s site.
End users can safeguard by themselves by upgrading to edition 2.4.50. It must be mentioned that “require all denied” (which denies access to all requests) is the default for safeguarding documents exterior of the web root, researchers have reported – which mitigates the issue.
Apache credited Ash Daulton and the cPanel Security Staff for reporting the bug.
Examine out our free upcoming live and on-desire webinar events – exceptional, dynamic conversations with cybersecurity gurus and the Threatpost community.
Some pieces of this short article are sourced from:
threatpost.com

 Northern Irish Voucher Scheme Marred by Identity Snag
Northern Irish Voucher Scheme Marred by Identity Snag