The researcher uncovered that he could achieve unauthorized digicam accessibility by using a shared iCloud document that could also “hack every web-site you have at any time frequented.”
A researcher who confirmed Apple how its webcams can be hijacked by using a common cross-web site scripting bug (UXSS) Safari bug has been awarded what is reportedly a report $100,500 bug bounty. The bug could be made use of by an adversary as aspect of an attack to gain whole accessibility to just about every web site at any time visited by the target.
The bug-finder is Ryan Pickren, founder of proof-of-concept sharing platform BugPoC and a former Amazon Web Products and services security engineer. This is not the initial time he’s found bugs that let him hoodwink Apple’s cameras: In 2020, he identified vulnerabilities in the Safari browser that could be used to snoop on iPhones, iPads and Mac pcs working with their microphones and cameras, just by convincing a target to click a person destructive website link.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Wonderful study after once again from Ryan Pickren for those people seeking for Apple bugs: Gaining unauthorized digicam access via Safari UXSShttps://t.co/SP8duGpq8T
— Jon Bottarini (@jon_bottarini) January 25, 2022
This time all-around, according to Pickren, he observed a collection of flaws – in Safari 15 and iCloud Sharing – that could once more guide to unauthorized digital camera obtain, which would once again allow for an attack to be launched from a destructive web-site.
But his much more current uncover is even worse: It could also help a shared iCloud document to “hack every single web-site you’ve ever frequented,” he stated, and could steal permissions to use multimedia – in other words, the microphone, camera and screensharing.
Pickren claimed that the exact hack could outcome in an attacker attaining total accessibility to a device’s full filesystem, y exploiting Safari’s webarchive information, which are the documents Safari generates as an substitute to HTML when it saves a internet site domestically.
Pickren submitted the bugs to Apple past July. The iPhone-maker patched the issues earlier this thirty day period and subsequently awarded the $100,500 bug bounty to Pickren.
The Bugs
The issues are uncovered in ShareBear, a at the rear of-the-scenes iCloud file-sharing application that prompts users when they try out to open a shared document for the first time – and only the initially time. Considering the fact that consumers are not offered with the show yet again as soon as they’ve accepted the prompt to open the file, Pickren observed that everyone who has accessibility to the file can alter the file’s material soon after that occurs.
“ShareBear will then download and update the file on the victim’s device devoid of any person interaction or notification,” Pickren spelled out in his technical create-up. “In essence, the sufferer has specified the attacker permission to plant a polymorphic file on to their device and the authorization to remotely start it at any instant.”
These three measures are associated in working with ShareBear to down load and open up a webarchive file:


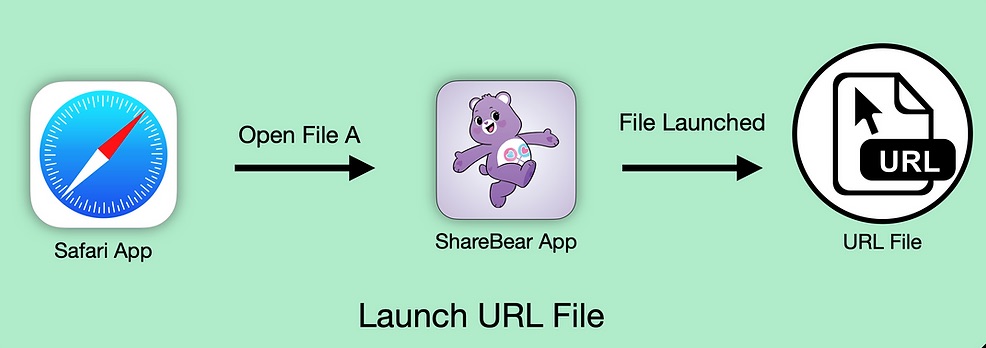
Levels of ShareBear attack. Resource: Ryan Pickren.
Pickren identified 4 zero-day bugs, the subsequent of which have been given CVE monitoring figures:
- CVE-2021-30861: A logic issue in Webkit, rated at 5.5 in criticality, that Apple addressed with enhanced state administration in macOS Monterey 12..1. The bug could allow for a destructive software to bypass checks finished by Gatekeeper: a macOS security characteristic that attempts to cut down the likelihood of inadvertently executing malware by enforcing code signing and verifying downloaded apps just before permitting them to operate.
- CVE-2021-30975: An issue in macOS Monterey’s Script Editor with a base criticality rating of High – 8.6 – that may perhaps allow for a destructive OSAX scripting addition to bypass Gatekeeper checks and circumvent sandbox restrictions. Apple dealt with the issue by disabling execution of JavaScript when viewing a scripting dictionary.
“This job was an fascinating exploration of how a style flaw in 1 application can allow a range of other, unrelated, bugs to grow to be a lot more hazardous,” Pickren concluded. “It was also a terrific illustration of how even with macOS Gatekeeper enabled, an attacker can still reach a good deal of mischief by tricking authorized applications into executing malicious items.”
Examine out our absolutely free approaching reside and on-desire on the internet city halls – exceptional, dynamic discussions with cybersecurity experts and the Threatpost neighborhood.
Some sections of this report are sourced from:
threatpost.com


 Prison for Dark Overlord Collaborator
Prison for Dark Overlord Collaborator