Phil Richards, vice president and CSO at Ivanti, points out how organizations can layout DevOps procedures and programs to thwart cyberattacks.
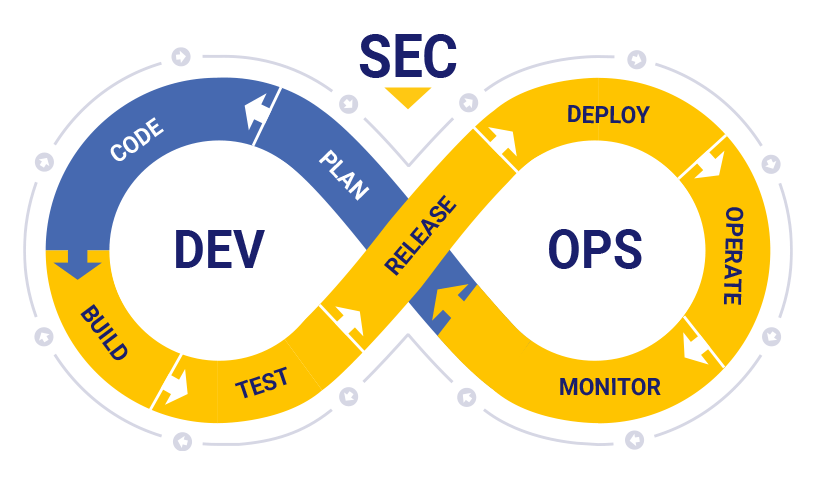
Security ought to hardly ever be an afterthought when developing software program and apps. Having said that, as technological improvements continue to consider keep, the security instruments several depend on are changing in real-time, and combatting opportunity breaches or hacks of your wares before they arise now calls for new methods. To stay a single step ahead of terrible actors, it’s time to reimagine the application-advancement procedure from “DevOps” to “DevSecOps.”
DevOps is an evolution of the agile growth lifecycle for software program that bridges the gap amongst improvement and operations teams. It breaks down silos and will increase an organization’s capability to provide purposes and providers a lot quicker than classic software package-development styles. Formerly, the regular “waterfall method” needed extended cycles upfront and resulted in arduous and cumbersome processes – and by the time these solutions have been considered ready for release, the current market experienced very likely altered.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
These days, agile software package groups have release cycles that are a issue of days or several hours, which boosts the risk of creating problems and introducing vulnerabilities. So, how can organizations produce much more protected code and apps when doing work at breakneck speeds, and thwart probable cyberattacks when they do not but know what those people attacks glimpse like? To bolster cybersecurity for their products and solutions, solutions and partners, a enterprise have to shift from a DevOps lifestyle to “DevSecOps” culture.
Begin Protected, Remain Secure
DevSecOps places security at the forefront of the enhancement procedure as a whole, guaranteeing that excellent cyber-cleanliness continues to be top-of-intellect for developers and operators from start out to finish. This shift in state of mind encourages organizations to obtain the best probable techniques to building secure code and purposes – and there are a range of assets and techniques to aid improvement teams do specifically that.
In this article are some of the most significant:
- Security Frameworks: It is always very best to get started with a roadmap – and by wanting to third-party resources for finest techniques, corporations can be certain their application is geared up for just about any problem. For example, The Making Security In Maturity Design, a.k.a. BSIMM, is a good source listing about 120 security finest tactics (this kind of as security screening automation by means of static and dynamic investigation), to assistance enhancement teams hold these measures prime of thoughts when coming up with their options.
- Security Code Education: Builders never know what they do not know – so it is up to businesses to coach them on critical threats and very best practices. By applying ongoing security-consciousness trainings, organizations can rest confident that their groups are adequately ready to detect and suitable any vulnerabilities in their code and products and solutions.
- Security Gates: In DevOps construct processes, security gates can block a release – offering security and engineering groups sufficient time to decide what level of severity of these bugs will break the in general create. Implementing security gates will assistance teams determine specifically what requirements to be mounted in advance of release.
- Applying a Multi-Layered Security Method: To make sure security across the board, corporations ought to make security everyone’s accountability. For illustration, this could start off by supplying builders resources to detect vulnerabilities as they compose code, and then making use of an inner staff to run static and dynamic software security equipment routinely. For more security, companies can then bring in exterior testers to perform black-box and grey-box screening or, they can set up a bug-bounty software and fork out security scientists to glance for vulnerabilities that are a lot more complicated to locate.
Why Third-Party Libraries Are Your Duty
3rd-party libraries like Apache Struts, Telerik UK (a third-party .NET library) and other folks are considered both equally a blessing and a curse for corporations. On the just one hand, businesses can leverage work crafted by other people, adapt it and generate much more loaded ordeals on prime of it, allowing for them to carry their abilities without acquiring to make everything from scratch. On the other hand, continued updates and upgrades of the libraries is required to retain a clear code base. It’s simple to import malicious code from code repositories, too.
Builders will require to update toolkits to ensure third-party elements have their vulnerabilities patched consistently and in actual-time, simply because even the most insignificant oversights by your team or your partners can outcome in the most considerable breaches. In reality, the Cybersecurity and Infrastructure Security Agency (CISA) a short while ago unveiled a list of the most-exploited software vulnerabilities and Apache Struts was the second-most attacked technology on the list.
Attackers also normally exploit vulnerabilities in open up-supply web products and services, these kinds of as Apache Tomcat, which is bundled in an untold amount of solutions.
The Ongoing Match of Whack-a-Mole
Threats and attack models that do not exist right now will attempt to exploit vulnerabilities in your systems tomorrow. Having said that, by inserting security at the forefront and employing a DevSecOps lifestyle, companies are greater positioned to mitigate threats as they seem – and in advance of they induce any issues or interruptions.
The following wave of threats is coming. Is your business organized?
Phil Richards is CSO at Ivanti.
Love added insights from Threatpost’s InfoSec Insider neighborhood by visiting our microsite.
Some elements of this report are sourced from:
threatpost.com

 Trickbot Malware Rebounds with Virtual-Desktop Espionage Module
Trickbot Malware Rebounds with Virtual-Desktop Espionage Module