A supply-chain attack could have siphoned delicate info out of Jira, these types of as security issues on Atlassian cloud, Bitbucket and on-prem products.
Atlassian, a platform employed by 180,000 prospects to engineer application and take care of tasks, could have been hijacked with a single click thanks to security flaws, researchers have disclosed.
On Thursday, Examine Level Investigate (CPR) printed a report (PDF) outlining how an attacker could have exploited the bugs to obtain Atlassian’s Jira: a proprietary bug-monitoring and agile undertaking management tool. Jira counts some heavyweights among the its lover foundation: the software program-progress instrument is made use of by around 65,000 buyers, such as the likes of Visa, Cisco, Pfizer, Fedora Commons, Hibernate, and the Apache Software program Foundation.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
CPR scientists reported that with just a single click on, an attacker could have siphoned delicate facts out of Jira, this kind of as “security issues on Atlassian cloud, Bitbucket and on-premise goods.”
The flaws could have also enabled an attacker to just take over accounts and to management some of Atlassian’s apps, like Jira and Confluence: a web-centered company wiki that arrives with a constructed-in Tomcat web server and hsql database and which also supports other databases. Extra than 60,000 buyers use Confluence, together with LinkedIn, NASA and the New York Times.
Bugs Could Have Led to SolarWinds-esque Offer-Chain Attack
With that stage of management above Atlassian, a single imagines that an exploit could have been fashioned that would have been comparable to the SolarWinds supply-chain attack, in which attackers utilised a default password as an open up door into a software program-updating mechanism.
The threat actors in the significantly-ranging marketing campaign were being in a position to use SolarWinds’ Orion network management system to infect targets by pushing out a customized backdoor called Sunburst by means of trojanized solution updates. Much-ranging is an understatement: The provide-chain attack succeeded in compromising the head of the Office of Homeland Security (DHS) under former president Trump, other top rated-ranking members of the department’s cybersecurity workers, numerous huge enterprises and other U.S. governing administration agencies.
Of note, Orion is an infrastructure monitoring and administration device that sits in a network sweet location, wherever it reaches other property and so helps make an best base camp for an attacker to have out malicious routines.
In fact, it was the SolarWinds catastrophe that influenced CPR to examine Atlassian n the initial location: Scientists claimed that they grew curious about offer-chain attacks adhering to the incident.
In the training course of its investigation, CPR managed to bypass Atlassian’s security steps, “proving that an attacker could have injected malicious code, executed steps on behalf of consumers, and hijacked user classes,” CPR researchers wrote.
They pointed out that Bitbucket, a Git-centered source code repository hosting support, could also have performed a aspect in a provide chain attack to goal Atlassian companions and customers. The vulnerability afflicted numerous Atlassian-maintained internet sites that help clients and partners but doesn’t impact Atlassian cloud-centered or on-prem products and solutions.
Oded Vanunu, head of merchandise vulnerabilities study at Examine Point Application, was quoted in a launch as declaring that supply chain attacks “have piqued our curiosity all year, at any time because the SolarWinds incident.” He noted that Atlassian platforms are “central to an organization’s workflow.”
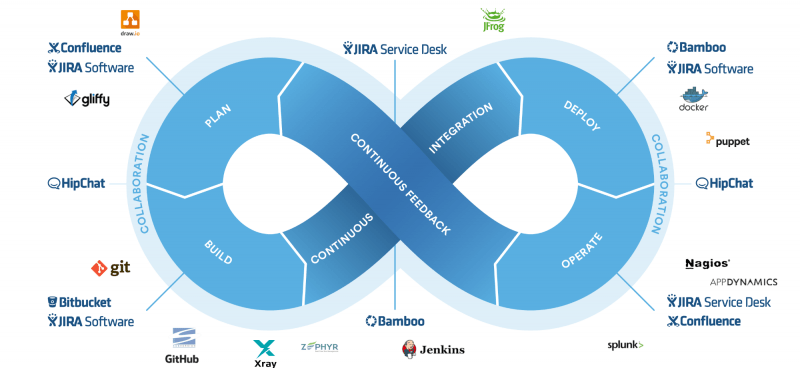
“An incredible volume of source chain information flows via these purposes, as perfectly as engineering and challenge administration,” Vanunu ongoing. “Hence, we started asking a relatively provocative query: What details could a malicious user get if they accessed a Jira or a Confluence account?”
Account Takeover
The solution: a ton of sensitive info. In its investigations, CPR achieved account takeover on Atlassian accounts available by subdomains below atlassian.com. These are the subdomains that scientists observed to be susceptible:
- jira.atlassian.com
- confluence.atlassian.com
- getsupport.atlassian.com
- associates.atlassian.com
- developer.atlassian.com
- support.atlassian.com
- schooling.atlassian.com
Exploiting Atlassian required, first off, finding a way to inject code into Atlassian. Researchers did so through an XSS vulnerability on the subdomain “training.atlassian.com”, which delivers users programs or credits. When the product form is “training_credit”, an further parameter identified as “options._coaching_credit history_account” is additional to ask for: a parameter that was vulnerable to XSS.
The Material Security Plan (CSP) was configured “poorly” on this subdomain, the researchers discussed, with “unsafe-inline” and “unsafe-eval” directives, which lets script execution. This made the subdomain “a fantastic starting point” for study, they explained. They had been capable to exploit the XSS bug to snag all the cookies and the area storage of the concentrate on.
Future, given that the stored XSS could only be run when including things to the procuring cart, the scientists experienced to make the user include a malicious item without having their discover. Supplied that there was no CSRF token, they could complete a CSRF attack on the purchasing listing and execute their payload. To do so, they uploaded a proof of concept and sent it to the target. For the reason that that payload was Saved XSS, it was stored in the databases and included to the Browsing List, and their destructive item was included to the searching cart.
The scientists made use of this code injection to increase a new session cookie to the user’s account, and, in blend with a session fixation vulnerability in Atlassian domains, they managed to choose over accounts.
What Attackers Could Have Completed
The bugs would have enabled an attacker to pull off a laundry checklist of malicious activities, these types of as cross-web site scripting (XSS) attacks cross-web-site request forgery (CSRF) attacks or session fixation attacks.
“In other phrases, an attacker could use the security flaws found by CPR to choose handle above a victim’s account, conduct actions on behalf of him, and attain obtain to Jira tickets,” the scientists pointed out. “Furthermore, an attacker could have edited a company’s Confluence wiki, or [viewed] tickets at GetSupport. The attacker could have absent on to attain personal information and facts. All of this could be accomplished in just a single click on.”
Attack Methodology
A thriving attack chain would have entailed these methods:
CPR disclosed its study findings to Atlassian on Jan. 8. According to CPR researchers, Atlassian said it deployed a patch on Could 18.
“In a environment wherever distributed workforces increasingly depend on remote systems, it’s imperative to be certain these technologies have the most effective defenses from destructive info extraction,” Vanunu concluded. “We hope our hottest study will assist corporations to raise the recognition on offer chain attacks.”
Threatpost has attained out to Atlassian for comment. As of Wednesday evening, the organization hadn’t supplied any input.
Be a part of Threatpost for “Tips and Tactics for Much better Danger Hunting” — a Dwell event on Wed., June 30 at 2:00 PM ET in partnership with Palo Alto Networks. Learn from Palo Alto’s Device 42 specialists the greatest way to hunt down threats and how to use automation to enable. Sign up In this article for no cost.
Some components of this short article are sourced from:
threatpost.com

 30M Dell Devices at Risk for Remote BIOS Attacks, RCE
30M Dell Devices at Risk for Remote BIOS Attacks, RCE