A researcher was equipped to remotely management the lights, mattress and air flow in “smart” hotel rooms via Nasnos vulnerabilities.
LAS VEGAS – A series of vulnerabilities in internet of factors (IoT) products often uncovered in related resort rooms allowed a researcher to just take control of several rooms’ amenities – and punish a loud neighbor.
An inadvertent bug hunt began when Kya Supa, security consultant at LEXFO, was touring overseas on vacation. He used a couple nights in a so-termed “capsule resort,” which refers to lodging that consist of small rooms stacked side-by-side. In an hard work to make up for area constraints, these varieties of digs are inclined to provide a handful of digital bells and whistles, and in accordance to Supa, this distinct hotel was no different.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
In a Wednesday session at Black Hat 2021, “Hacking a Capsule Hotel – Ghost in the Bedrooms,” Supa explained that an iPod contact given at verify-in enables customers to manage their lights, transform the placement of their adjustable beds, and manage the ventilation fans.
All very well and excellent – and Supa would not have seemed under the hood of the technology making it possible for the area handle besides for the fact that a noisy neighbor prompted him to see if he could bypass any security protections to acquire handle of other bedrooms in the hotel. It turns out that he was equipped to do just that using 6 diverse exploits that ended up chained with each other.
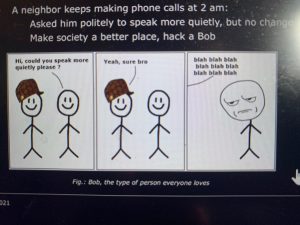
“I achieved my pal ‘Bob,’” the researcher discussed. “This neighbor woke me up two moments all through very last working day. He woke me up due to the fact he was earning phone phone calls at 2 a.m. in the early morning, and he was talking truly loudly. So, the next night time I went to see him and I asked him politely to discuss much more quietly. He informed me ‘yeah, confident, no difficulty.’ But there was no adjust.”
Supa went on to even further travels but arrived back to the identical lodge a several times later – and ‘Bob’ was continue to there, exhibiting the same actions. So, the researcher resolved to do a little pen tests.
Using Stock of the Capsule Lodge Home
“The iPod touch will come with an application that can help to command your bed room, and it is linked to gadgets working with Bluetooth or Wi-Fi,” Supa spelled out. “So there ought to be a way to talk with no matter what is managing the bed room.”
An exploration of the bedroom uncovered the presence of a Nasnos CS8020 distant, which can be used to regulate up to 5 Nasnos devices – the same kinds that the iPod contact connects to. It is utilized in scenario the iPod contact is lost or if the software doesn’t get the job done.
He also deduced the existence of a Nasnos CS8700 router within every room’s wall, which allows the handle of the Nasnos products about Wi-Fi, either from the iPhone touch or the distant (and most likely from Android smartphones or other iOS products).
Armed with the know-how of what the room’s IoT architecture seemed like, he moved into the exploitation phase.
Exploiting Nasnos Router Vulnerabilities
The iPod touch in this situation has a one software that a hotel customer is permitted to accessibility, with uncomplicated buttons linking to the several “smart room” capabilities.
“When I initial attempted to exit the application, I observed that it was not possible,” Supa mentioned. “I are unable to exit the application or turn off the iPod touch, but when I triple-tapped on the base, I see that a passcode was requested for. By exploring on the internet I found that this actions was due to an iOS feature referred to as Guided Access.”
Guided Accessibility limitations a device to distinct purposes and makes it possible for users to control which characteristics are available – a type of parental controls. It can be overridden with a passcode – but Supa found that the safety is only configured at operate time.
“This usually means the protection is no lengthier current if we reboot the unit,” he stated. “Yes, we can’t turn off the iPod…but we can nevertheless drain its battery, connect it to energy later on and reboot the gadget. As soon as you do that, the safety is no for a longer time existing and we can entry almost everything – other apps and the iPod touch options.”
In inspecting the iPod touch’s product settings, the researcher identified that it was enrolled in a cell gadget administration (MDM) resolution, with two saved Wi-Fi networks. One of these was named Nasnos-CS8700, and it was safeguarded utilizing only WEP – a incredibly old encryption technique that is been crackable for practically 20 decades.
In simple fact, it is quite simple to retrieve a WEP key, the researcher discussed.
“You can return a WEP essential by capturing close to 80,000 packets [from the access point],” he explained, which he was equipped to do with a basic JavaScript payload that constantly generates address resolution protocol (ARP) requests. ARP broadcasts a ask for packet to all the machines on a offered network and asks if any of them know they are making use of that unique IP address. Supa set up a rogue obtain issue (AP) employing his Android smartphone, linked the iPod touch to it, cached the payload, connected the iPod touch again to the Nasnos AP and executed the code. Soon he was ready to retrieve the crucial, and soon identified that the router was accessible with default credentials.
A slide from Supa’s digital presentation.
“The password starts off with 123, and I will let you guess what goes just after,” Supa reported.
He linked his notebook to the susceptible AP working with the qualifications in buy to established up a gentleman-in-the-center architecture to inspect traffic flowing from the router: The iPod touch related to the rogue Android AP the Android AP was also linked to a Wi-Fi card in Supa’s laptop computer. In the meantime, a second Wi-Fi card in the laptop was linked to the Nasnos AP, and many thanks to IP forwarding, the researcher was ready to observe that packets were being despatched to the Nasnos router on TCP port 8000 with no authentication or encryption necessary.
“After that, I just formulated a application that sends the identical packets [from the laptop to the router] based on the action essential,” he mentioned. “This suggests we are now in a position to command the bed room from a laptop. But can we manage all bedrooms?”
In other words, could he mess with “Bob?”
Managing All Capsule Bedrooms
The initially factor Supa needed to do was figure out if the Wi-Fi vital is generated dynamically or set manually.
To locate out, he reverse-engineered an software from Nasnos which is readily available on Google Participate in. store. It allows end users to established up the Wi-Fi configuration of a Nasnos router. In examining the app, Supa arrived throughout one more vulnerability: Packets are sent to the router on UDP port 988 as part of the remote configuration services but it does not involve authentication for configuring (or reconfiguring) the router.
This didn’t expose regardless of whether the keys are static or dynamic on the other hand. But when coming again to the capsule lodge the second time, Supa was assigned a distinctive space.
“I recognized a similarity with the Wi-Fi key of my outdated bedroom – only the four very last characters seemed to improve,” he said. “If this is the circumstance throughout all 119 bedrooms, this will mean there are only 65,536 alternatives, which is nothing…we can start a dictionary attack with a file containing all the doable keys.”
Armed with a list of keys, the up coming move was matching the correct essential to the proper SSID for “Bob.”
“I employed my laptop computer to change on the gentle of each individual SSID’s home, and when I noticed a modify in his room, I knew that it was the accessibility level I was hunting for,” Supa discussed. “I went and attempted to picture the greatest scenario I could for ‘Bob.’ A excellent a person would be to build a script that each two words and phrases would transform the mattress into a sofa and back again, transform on and off the lights and so on. Influence him there are ghosts.”
Unpatched Vulnerabilities?
In all, Supa identified six distinctive bugs:
- Guided Accessibility bypass
- Utilization of WEP
- Basic router interface with default qualifications
- Nasnos assistance out there devoid of authentication
- Browse/create obtain to distant configuration capacity for the router
- Use of non-random AP keys
Supa explained that he contacted each Nasnos and the resort about the weaknesses.
“The hotel was definitely awesome and took this issue very seriously,” he mentioned. “It’s now using a new architecture so it is not attainable to exploit vulnerabilities in that resort any longer.”
However, Nasnos did not react to his report, he mentioned, so if non-random keys are made use of in all of its routers, many other environments are inclined to comparable exploits.
Masnos did not quickly answer to a ask for for remark.
Apprehensive about the place the subsequent attack is coming from? We’ve received your back. REGISTER NOW for our future live webinar, How to Imagine Like a Danger Actor, in partnership with Uptycs. Obtain out exactly where attackers are targeting you and how to get there 1st. Sign up for host Becky Bracken and Uptycs researchers Amit Malik and Ashwin Vamshi on Aug. 17 at 11AM EST for this LIVE discussion.
Some sections of this short article are sourced from:
threatpost.com


 Several Malware Families Targeting IIS Web Servers With Malicious Modules
Several Malware Families Targeting IIS Web Servers With Malicious Modules