The Iran-linked APT is concentrating on Israeli scholars and U.S. government personnel in a credential-thieving effort.
The Iran-affiliated APT regarded as Charming Kitten is back with a new tactic, impersonating Persian-speaking journalists by way of WhatsApp and LinkedIn, in purchase to con victims into opening malicious inbound links. The targets are Israeli scholars from Haifa and Tel Aviv universities, and U.S. government staff members, scientists mentioned.
In accordance to an examination from Clearsky, the hottest gambit was very first spotted in July. The attackers have been pretending to be recognised writers for the Deutsche Welle and/or Jewish Journal retailers, and approach targets by means of email, and WhatsApp messages and calls. To lend verisimilitude to their impersonations, the cybercriminals also established up bogus LinkedIn profiles corresponding to the journalists’ names, and have been sending out LinkedIn messages to corner victims as very well. The stop sport is to encourage a target to click on a destructive website link, which usually takes end users to a phishing page to steal credentials.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“The malicious hyperlink is embedded in a respectable, compromised Deutsche Welle area, with waterhole procedures,” in accordance to a writeup from Clearsky, issued past week. “Each victim receives a personalized connection, tailor-made to their specific email account. We discovered an attempt to mail a malicious ZIP file to the target as nicely, extra to a message that was despatched to the victim via a fake LinkedIn profile.”
This method is a marked departure from Charming Kitten’s normal M.O., which tends to rely on emails and SMS.
“These two platforms allow the attacker to arrive at the victim effortlessly, investing minimal time in producing the fictitious social-media profile,” in accordance to Clearsky. “However, in this marketing campaign Charming Kitten has utilized a trusted, effectively-produced LinkedIn account to guidance their email spear-phishing attacks…[we also] observed a willingness of the attackers to talk on the phone right with the target, employing WhatsApp calls, and a genuine German phone range. This [tactic, technique and procedure] (TTP) is unusual and jeopardizes the faux id of the attackers.”
A faux LinkedIn webpage.
To get all around the opportunity language issue, Charming Kitten commonly chooses to impersonate Persian- or Farsi-talking journalists, to neutralize detection by accent when possessing the phone phone. Clearsky researchers pointed out that a cadre of Deutsche Welle reporters, for occasion, are basically at first from Iran.
Remarkably Specific
The most latest campaign had a several various prongs, but email was the first attack vector throughout the board.
In accordance to the analysis, some emails impersonated an Iranian Deutsche Welle journalist that speaks fluent Farsi with a local accent. Many others impersonated an Israeli scholar from Tel Aviv University, with e-mail inviting targets to an alleged Zoom assembly in Hebrew. Nevertheless other folks impersonated a reporter from Jewish Journal asking the concentrate on to sign up for a webinar on “citizenship and liberty of ladies and girls in Iran and it is long run.”
In all situations, the attackers attempt to get a dialogue likely in order to establish have faith in. For instance, in the scenario of the Jewish Journal webinar, the attackers tried out to entice the sufferer with nominating them as its most important speaker, “chosen from more than a hundred participants.”
Soon after these discussions with the focus on, the attacker requests that they change to WhatsApp for more discussion, according to the examination – making an attempt to have interaction the concentrate on by using many messages for up to 10 days.
“Charming Kitten despatched various and repeating messages, sometimes in pretty brief time, until finally the goal responded,” researchers wrote. “The messages ended up sent from a German variety (prefix +49) to build a sense of reliability, and the WhatsApp account bears the picture of the journalist getting impersonated.” If the target is not ready to share a individual phone amount, the attackers will send the human being a message from the bogus LinkedIn accounts.
These 2nd-phase messages incorporate destructive hyperlinks that purport to guide to registration for various on-line phone calls or gatherings. The url will choose buyers to a web page exactly where they can “activate their accounts” by signing up on the internet site “Akademie DW” (which is actually just a phishing site). The malicious backlink pointing to this webpage was most a short while ago hosted on a Deutsche Welle genuine domain (dw[.]de), the scientists explained.
“Each sufferer receives a personalised backlink for their individual email handle – the term ‘?id=’ adopted by the word ‘SSH’ and 3 sets of five letters and numbers, “according to the scientists. On the phishing webpage, “If the target enters their correct password, they are despatched to a two-aspect authentication (2FA) web site,” stated the scientists. “A erroneous password provides an mistake message. The attackers will then tension the sufferer to try out once more working with their university email.”
The attackers also offer you to have interaction in a direct phone contact with the targets to assistance them with the course of action.
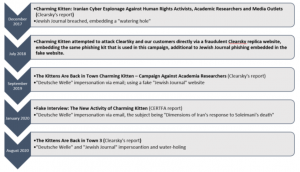
A timeline of Charming Kitten action.
Charming Kitten, a.k.a. APT35 or Ajax, has been lively given that 2014. It is acknowledged for politically motivated and socially engineered attacks, and normally works by using phishing as an attack vector. Its primary targets are Iranian academia professionals, human-legal rights activists, journalists, the Baha’I community, ambassadors and previous employees of the U.S. Point out Department, and COVID-19-related organizations this kind of as Gilead and the Earth Wellbeing Organization.
The team was also a short while ago seen making an attempt to hack into email accounts tied to the Trump 2020 re-election marketing campaign, ramping up individuals initiatives with new spearphishing tactics. This is also only the most up-to-date marketing campaign the place the group has impersonated journalists. In February, the group purported to be from the Wall Avenue Journal, and was found emailing a victim to request for an interview in an exertion to obtain rely on.
On Wed Sept. 16 @ 2 PM ET: Learn the secrets to managing a prosperous Bug Bounty Program. Resister today for this FREE Threatpost webinar “Five Necessities for Functioning a Productive Bug Bounty Program“. Hear from top Bug Bounty Program experts how to juggle general public versus private applications and how to navigate the difficult terrain of handling Bug Hunters, disclosure insurance policies and budgets. Join us Wednesday Sept. 16, 2-3 PM ET for this LIVE webinar.


 Internet Outage Causes Chess Championship Draw
Internet Outage Causes Chess Championship Draw