The computer software-engineering platform is urging people to patch the critical flaw ASAP.
Atlassian has dropped a patch for a critical vulnerability in lots of variations of its Jira Information Centre and Jira Company Administration Knowledge Middle products and solutions, which can guide to arbitrary code execution.
Atlassian is a system which is used by 180,000 shoppers to engineer application and handle initiatives, and Jira is its proprietary bug-monitoring and agile undertaking-administration device.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
On Wednesday, Atlassian issued a security advisory about the vulnerability, which is tracked as CVE-2020-36239. The bug could permit remote, unauthenticated attackers to execute arbitrary code in some Jira Data Center products and solutions.
BleepingComputer acquired ahold of an email Atlassian despatched to organization buyers on Wednesday that urged them to update ASAP.
The vulnerability has to do with a lacking authentication verify in Jira’s implementation of Ehcache, which is an open up-supply, Java dispersed cache for typical-reason caching, Java EE and lightweight containers which is utilized for functionality and which simplifies scalability.
Atlassian stated that the bug was introduced in variation 6.3. of Jira Info Heart, Jira Core Facts Middle, Jira Program Knowledge Heart and Jira Provider Administration Information Middle (identified as Jira Support Desk prior to 4.14).
In accordance to Atlassian’s security advisory, that list of goods uncovered a Ehcache remote strategy invocation (RMI) network assistance that attackers – who can link to the support on port 40001 and possibly 40011 – could use to “execute arbitrary code of their option in Jira” as a result of deserialization, owing to lacking authentication.
RMI is an API that acts as a mechanism to permit remote interaction amongst programs composed in Java. It lets an item residing in one particular Java virtual equipment (JVM) to invoke an object working on an additional JVM Frequently, it will involve just one system on a server and a person on a shopper. The gain of RMI, as BleepingComputer describes it, is that “programmers can invoke methods current in remote objects—such as those current inside of an application running on a shared network, suitable from their application as they would run a neighborhood approach or course of action.”
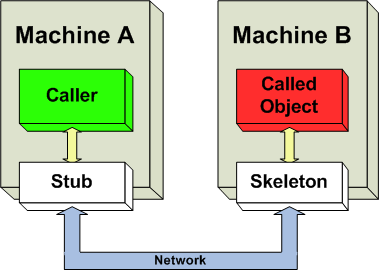
Workings of RMI. Supply: Wikipedia.
Atlassian “strongly suggests” limiting entry to the Ehcache ports to only Details Heart situations, but mentioned that there’s a caveat: “Fixed versions of Jira will now call for a shared mystery in order to make it possible for accessibility to the Ehcache company,” in accordance to the advisory.
Impacted Versions
These are the impacted variations of Jira Data Centre and Jira Company Administration Data Middle:
Jira Facts Heart, Jira Core Details Middle, and Jira Software program Info Center – ranges
- 6.3. <= version < 8.5.16
- 8.6.0 <= version < 8.13.8
- 8.14.0 <= version < 8.17.0
Jira Service Management Data Center – ranges
- 2.0.2 <= version < 4.5.16
- 4.6.0 <= version < 4.13.8
- 4.14.0 <= version < 4.17.0
Jira Data Center, Jira Core Data Center, and Jira Software Data Center
- All 6.3.x, 6.4.x versions
- All 7.0.x, 7.1.x , 7.2.x, 7.3.x, 7.4.x, 7.5.x, 7.6.x, 7.7.x, 7.8.x, 7.9.x, 7.10.x, 7.11.x, 7.12.x, 7.13.x versions
- All 8.0.x, 8.1.x, 8.2.x, 8.3.x, 8.4.x versions
- All 8.5.x versions before 8.5.16
- All 8.6.x, 8.7.x, 8.8.x, 8.9.x, 8.10.x, 8.11.x, 8.12.x versions
- All 8.13.x versions before 8.13.8
- All 8.14.x, 8.15.x, 8.16.x versions
Jira Service Management Data Center
- All 2.x.x versions after 2.0.2
- All 3.x.x versions
- All 4.0.x, 4.1.x, 4.2.x, 4.3.x, 4.4.x versions
- All 4.5.x versions before 4.5.16
- All 4.6.x, 4.7.x, 4.8.x, 4.9.x, 4.10.x, 4.11.x, 4.12.x versions
- All 4.13.x versions before 4.13.8
- All 4.14.x, 4.15.x, 4.16.x versions
Atlassian’s advisory said that customers who have downloaded and installed any affected versions “must upgrade their installations immediately to fix this vulnerability.” Having said that, Atlassian also noted that the “critical” rating is its own assessment and that customers “should evaluate its applicability to your own IT environment.”
Non-Affected Versions
Here’s the list of products that aren’t affected by the flaw:
- Atlassian Cloud
- Jira Cloud
- Jira Provider Administration Cloud
- Non-Data Heart circumstances of Jira Server (Core & Program) and Jira Services Management
Also, shoppers who have upgraded Jira Information Heart, Jira Main Info Center, Jira Program Details Heart to versions 8.5.16, 8.13.8, 8.17. and/or Jira Assistance Administration Details Middle to variations 4.5.16, 4.13.8 or 4.17. are off the hook: They really do not need to up grade.
Atlassian is Attacker Catnip
Some of the premier enterprises with the most refined item growth use Atlassian items. Between its additional than 65,000 users, Jira counts some significant followers, which includes the likes of the Apache Software Basis, Cisco, Fedora Commons, Hibernate, Pfizer and Visa.
Sadly, its reputation – specifically with the significant fish – and its capabilities make it a tempting focus on for attackers.
In June, scientists uncovered Atlassian bugs that could have led to a person-simply click takeover: A situation that introduced to intellect the potential for an exploit that would have been related to the SolarWinds offer-chain attack, in which attackers employed a default password as an open doorway into a software program-updating mechanism.
Chris Morgan, senior cyber-threat intelligence analyst at digital-risk company Digital Shadows, said that the vulnerability at the heart of Wednesday’s advisory is just the hottest in a series of bugs experiencing software engineering and administration platforms that, if exploited, “could direct to a selection of pernicious outcomes.”
While there’s no evidence of lively exploitation at this time, we can be expecting attempts to display up in the coming one to 3 months, Morgan predicted. “CVE-2020-36239 can be remotely exploited to obtain arbitrary code execution and will possible be of wonderful curiosity to both cybercriminals and nation-condition-associated actors,” he explained. He pointed to quite a few new source-chain attacks, such as attacks in opposition to software program vendors Accellion and Kaseya, that have leveraged vulnerabilities to obtain initial entry and to compromise computer software builds “known to be used by a assorted client foundation.”
Other security authorities agreed with Morgan’s evaluation. Andrew Barratt, taking care of principal of solutions and investigations at cybersecurity advisory business Coalfire, explained to Threatpost on Thursday that the vulnerability Atlassian disclosed on Wednesday “shows that attackers are even now hunting to leverage economies of scale and compromise various functions working with solitary platform-extensive vulnerabilities.”
Anticipate Exploitation, In the Wild Attacks
TLDR: Apply the update ASAP, or put into action Atlassian’s workarounds, Morgan emphasised.
That claimed, the true impression depends on the exposure of the RMI APIs, Barratt proposed. “This could lead to focused campaigns that aim on developers (traditionally who have a lot of privileges and useful resources on their machines) that then request to fall malware that exploits the Atlassian vulnerabilities for additional manipulation of product progress,” he said.
On the optimistic side, the issue could blow about prior to it gets dire, supplied that Atlassian is presently issuing patches and advising on short term mitigations, Barratt additional. “Hopefully the window for this to be a issue will be small – and some abide by-up evaluation of the techniques to verify for indicators of compromise will give self esteem that almost nothing critical has absent erroneous.”
Barratt thinks that the most relating to thing need to be “the renewed concentrate on perhaps a gold mine of chance.” Whilst focusing on builders isn’t new, he explained, targeting their equipment, platform and reducing potential self esteem in the item “shows the require for security orchestration tools that can help convey the variety of the trouble to solitary-administration check out.”
On the complex side of issues, Shawn Smith – director of infrastructure at application security supplier nVisium – posited that provide-chain attacks are a excellent argument in opposition to car-updating dependencies, but “this also usually means that security groups have to observe and take care of them effectively and proficiently,” as he explained to Threatpost through email on Thursday.
“Any updates to dependencies must be vetted prior to use, and units really should be applying model-locked dependencies to stop CI/CD programs from grabbing the most recent updates by default,” he added. “At the similar time, security groups must be checking to make sure that vulnerabilities are not tainting versions that are currently being used and advise developers and functions groups as issues crop up.”
Test out our no cost impending are living and on-need webinar functions – one of a kind, dynamic conversations with cybersecurity industry experts and the Threatpost local community.
Some areas of this write-up are sourced from:
threatpost.com

 What is Maze Ransomware?
What is Maze Ransomware?