DOJ expenses 6 Russian nationals for their alleged portion in the NotPetya, Ukraine electricity grid and Olympics cyberattacks.
The Section of Justice (DOJ) on Monday introduced rates from 6 Russian nationals who are allegedly tied to the Sandworm APT. The danger group is considered to have launched various superior-profile cyberattacks about the previous several many years – together with the harmful NotPetya cyberattack that focused hundreds of firms and hospitals around the world in 2017.
In accordance to the DOJ criticism, the 6 Russian nationals are tied to a division of the Russian military services intelligence assistance and also affiliated with the APT Sandworm, also acknowledged as TeleBots. The DOJ said cyberattacks connected to the six defendants have been “breathtaking” in their scope and “harmed regular individuals about the world,” reported Scott Brady, U.S. lawyer with the Western District of Pennsylvania, in a DOJ press convention on Monday.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The 6 defendants are: Yuriy Sergeyevich Andrienko (32) Sergey Vladimirovich Detistov (35) Pavel Valeryevich Frolov (28) Anatoliy Sergeyevich Kovalev (29) Artem Valeryevich Ochichenko (27) and Petr Nikolayevich Pliskin (32).
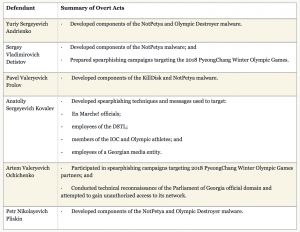
A breakdown of the fees towards each individual defendant. Credit rating: DoJ
Just about every were charged in seven counts: conspiracy to carry out laptop fraud and abuse, conspiracy to commit wire fraud, wire fraud, harming safeguarded desktops, and aggravated id theft, according to the DOJ.
In accordance to the DOJ, the alleged destructive exercise of the 6 dates back again to November 2015, with the group producing malware known as BlackEnergy, Industroyer and KillDisk. The team made use of the malware in attacks in opposition to Ukraine’s electric power grid, Ministry of Finance, and State Treasury Company from Dec. 2015 to Dec. 2016, according to the DOJ.
In April and May perhaps 2017 the group allegedly launched spearphishing campaigns concentrating on French President Macron’s “La République En Marche!” (En Marche!) political party prior to the 2017 French elections.

The 6 defendants. Credit history: DoJ
They were being also allegedly at the rear of the June 2017 damaging malware attacks that infected personal computers throughout the world, working with the NotPetya malware, resulting in the infection of 400 computer systems. The malware crippled lots of critical devices, which include mission critical techniques applied by hospitals like the Pennsylvania-primarily based Heritage Valley Well being Devices.
In February 2018, the team allegedly sent spearphishing strategies and malicious cellular programs concentrating on South Korean citizens and officials, Olympic athletes, partners, and guests, and Worldwide Olympic Committee (IOC) officers they then allegedly compromised computer systems supporting the 2018 PyeongChang Winter season Olympic Video games. This led to the Feb. 9, 2018, destructive malware attack versus the opening ceremony, applying malware known as Olympic Destroyer.
Ultimately, the group is alleged to have sent spearphishing e-mail to governing administration corporations investigating the poisoning of a former GRU officer and his daughter in the United Kingdom in April 2018 and to have targeted the country of Georgia in 2018 with a spearphishing attack that led to the defacement of 15,000 sites.
“Groups like this use ways, this kind of as spearphishing, that are just as possible to achieve targets on both equally computer systems, smartphones, or tablets,” Hank Schless, Senior Supervisor, Security Options at Lookout, informed Threatpost. “They know that the chance of a effective phishing attack will increase drastically if the focus on receives it on a cellular machine. They can phish login credentials from distinct end users that would permit them to get into the corporate infrastructure, then move laterally about the infrastructure for surveillance purposes or to exfiltrate beneficial information.”
Menace scientists applauded the crackdown, expressing that, whilst the arrest and extraction of the 6 Russian nationals seems unlikely, the indictments will limit their capability to use the Western financial method or travel to any state that may perhaps have an extradition settlement with the US.
“The prices submitted from Sandworm characterize not only the to start with felony rates against Sandworm for its most damaging attacks but the initial time that most of the charged menace actors have been publicly identified as customers of the cybercriminal team,” Kacey Clark, Threat Researcher at Electronic Shadows, informed Threatpost. “They also signify Sandworm’s to start with world regulation enforcement reaction to their deployment of the NotPetya ransomware that has crippled networks all over the world.”
Google’s Threat Investigation Team (TAG), Cisco’s Talos Intelligence Team, Facebook and Twitter have been credited in aiding the DOJ with its investigation.
Some elements of this report are sourced from:
threatpost.com


 iPhone 12 poses potential security risk for WhatsApp users
iPhone 12 poses potential security risk for WhatsApp users