Hundreds of countless numbers of email credentials, quite a few of which double as Energetic Directory domain credentials, came as a result of to credential-trapping domains in clear textual content.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Guardicore security researcher Amit Serper has identified a severe design bug in MIcrosoft Exchange’s autodiscover – a protocol that lets people quickly configure applications this sort of as Microsoft Outlook with just email addresses and passwords.
The flaw has brought about the Autodiscover services to leak almost 100,000 distinctive login names and passwords for Windows domains worldwide, Serper explained in a specialized report released this week.
“This is a severe security issue, because if an attacker can command these domains or has the skill to ‘sniff’ site visitors in the similar network, they can seize area credentials in basic text (HTTP standard authentication) that are being transferred about the wire,” he explained.
“Moreover, if the attacker has DNS-poisoning capabilities on a substantial scale (these as a nation-point out attacker), they could systematically syphon out leaky passwords by means of a large-scale DNS poisoning marketing campaign dependent on these Autodiscover TLDs [top-level domains],” Serpa wrote.
The style and design flaw triggers the protocol to leak web requests to Autodiscover domains outside of the user’s possess domain if they are in the exact TLD – i.e., Autodiscover.com. Guardicore picked up a slew of all those domains and discovered that researchers could set them up to intercept very clear-text account credentials for hapless consumers enduring network troubles or whose admins goofed on configuring DNS.
Area-shopping for Spree
Guardicore Labs picked up 11 Autodiscover domains with TLD suffixes that spanned the world and which are stated down below. Involving April 16 and Aug. 25, 2021, scientists set up these domains to connect with a web server Guardicore managed, therefore configuring the domains to provide as evidence-of-concept credential traps.
- Autodiscover.com.br – Brazil
- Autodiscover.com.cn – China
- Autodiscover.com.co – Columbia
- Autodiscover.es – Spain
- Autodiscover.fr – France
- Autodiscover.in – India
- Autodiscover.it – Italy
- Autodiscover.sg – Singapore
- Autodiscover.uk – United Kingdom
- Autodiscover.xyz
- Autodiscover.on the internet
Those credential traps opened the floodgate to “a massive” leak of legitimate Windows domain qualifications, in accordance to Serper’s writeup. Around that four-thirty day period period of time, Guardicore captured 372,072 Windows domain qualifications and 96,671 special credentials leaked out of apps which include Microsoft Outlook, mobile email clientele and other apps that interface with Microsoft’s Exchange server.
To top rated it all off, Guardicore made an attack that downgrades a client’s authentication scheme, elbowing it off of a protected one particular these types of as OAuth or HTLM and replacing it with HTTP Essential authentication, which sends credentials in very clear textual content.
Thus, those hundreds of countless numbers of email qualifications, a lot of of which double as Lively Directory area qualifications, arrived by way of to the credential-trapping domains in apparent textual content.
The Challenge: A POX Upon Your Protocol
The weak spot Guardicore found out has to do with a distinct implementation of Autodiscover dependent on the POX (aka “plain old XML”) XML protocol, through which purposes exchange raw XML files using typical transfer protocols such as HTTP, SMTP and FTP, or by using proprietary protocols, this kind of as concept-oriented middleware.
Following incorporating a new Microsoft Trade account to Outlook via its auto account setup, a prompt requests a user’s username and password. Just after the person obliges, Outlook tries to use Autodiscover to configure the shopper.
Autodiscover makes an attempt to set jointly a URL to fetch configuration details baked on the email domain in any of these formats that merge email domain, subdomain and a route string:
- https://Autodiscover.example.com/Autodiscover/Autodiscover.xml
- http://Autodiscover.illustration.com/Autodiscover/Autodiscover.xml
- https://example.com/Autodiscover/Autodiscover.xml
- http://example.com/Autodiscover/Autodiscover.xml
Slipping that, it starts off a “back-off” course of action, and therein lies the rub.
As Serper described, this back again-off system “is the perpetrator of this leak for the reason that it is generally trying to take care of the Autodiscover part of the domain and it will constantly check out to ‘fail up,’ so to speak.”
On its up coming attempt to develop an Autodiscover URL, the method would concoct “http://Autodiscover.com/Autodiscover/Autodiscover.xml,” which means that all of the requests that can’t get to the first domain tumble into the lap of whoever owns Autodiscover.com.
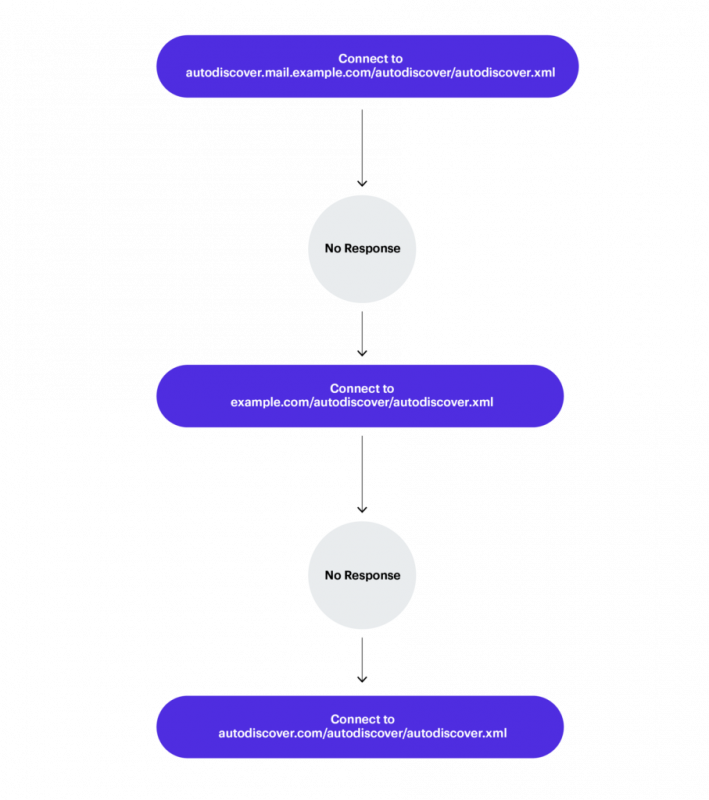
The Autodiscover again-off process. Source: Guardicore.
Following the HTTP GET requests to its purchased domains started to arrive, Guardicore was amazed to find out that lots of asked for the relative path of /Autodiscover/Autodiscover.xml with the Authorization header pre-populated with credentials.
“The exciting issue with a substantial quantity of the requests that we been given was that there was no attempt on the client’s side to examine if the useful resource is offered, or even exists on the server, ahead of sending an authenticated ask for,” Serper commented. “Usually, the way to put into action this kind of a scenario would be to initial look at if the useful resource that the client is requesting is legitimate, due to the fact it could be non existent (which will induce an HTTP 404 error) or it may possibly be password shielded (which will bring about an HTTP 401 mistake code).”
He ongoing, “Between Apr 16, 2021 to Aug 25, 2021 we have captured a significant amount of qualifications this way, useless to say, devoid of sending a single packet other than what’s needed to establish an HTTP/HTTPS session amongst our server and the miscellaneous purchasers.”

Requests breakdown. Source: Guardicore.
The requests – and their leaked credentials – came in from a huge vary of resources: publicly traded Chinese companies. Expenditure banks, food items companies, electrical power plants, energy shipping and delivery, serious estate, shipping and delivery and logistics, and jewelry corporations.
Specified that Microsoft Exchange is aspect of Microsoft’s “domain suite” of goods, the simple fact that anybody who has qualifications to log in to Trade inboxes of such companies – and, in most cases, also to their area qualifications – sets the phase for a earth of cybersecurity harm. “The implications of a area credential leak in this sort of scale are substantial, and can put organizations in peril” Serber stressed. “Especially in today’s ransomware-attacks ravaged-globe – the easiest way for an attacker to get entry into an firm is to use legit and legitimate credentials.”
Guardicore sees a bit of irony in all this: Attackers consider difficult to weasel qualifications out of customers, be it as a result of social engineering, phishing or what ever have you. This credentials leakage is like pennies from heaven for menace actors, although, coming as it does owing to a design flaw in protocol meant to streamline IT operations when it will come to email customer configuration. It “emphasises the importance of appropriate segmentation and Zero rely on,” Serper wrote.
A Structure Flaw That is Been Regarded About for Years
As of Thursday, the flaw hadn’t been patched, and Microsoft Senior Director Jeff Jones explained to Ars Technica that Guardicore disclosed the flaw publicly prior to reporting it to the firm. But as a Guardicore spokesperson advised Threatpost on Friday, it is not the first time that the flaw has been publicly documented.
“We did not notify Microsoft originally mainly because the protocol flaw is not new,” the Guardicore representative mentioned via email. “We had been just in a position to exploit it at a huge scale.”
In reality, as Guardicore’s paper outlined, the flaw was identified in 2017 by Condition Security and explained in a paper that thorough how the leak can be triggered by Autodiscover implementations on email customers on cell telephones, this sort of as Samsung’s email shopper on Android and Apple Mail on iOS (CVE-2016-9940, CVE-2017-2414).
In this article we are, four a long time later, and the situation has just gotten even worse, Guardicore claimed in the report:
The vulnerabilities disclosed by Form Security had been patched, still, right here we are in 2021 with a significantly larger sized menace landscape, working with the exact same trouble only with extra third-party programs outdoors of email purchasers. These applications are exposing their people to the exact threats. We have initiated dependable disclosure procedures with some of the sellers afflicted.
In a Thursday Tweet stream, Serper named out Microsoft for lagging – for yrs – in a reaction to this regarded flaw. “Microsoft had a good deal of time to resolve or address this issue, possibly by patching goods [or] just acquiring all of the autodiscover TLDs (which they are accomplishing ideal now),” he wrote.
The researcher pointed to this flaw’s historical past of research papers (these as Shape Security’s paper), Black Hat convention talks (there was 1 this kind of final month: It protected how Autodiscover formed a section of the ProxyShell vulnerabilities and attacks) and news articles “proving that these issues had been identified.”
1/n Thread: Very last issue about the total Microsoft conundrum due to the fact I really have extra urgent issues to deal with: Microsoft’s try through their PR male and the MVPs that have been dogpiling on me here and on LinkedIn are missing a position. This issue was acknowledged for many years
— Amit Serper (@0xAmit) September 23, 2021
Microsoft hadn’t responded to Threatpost’s request for comment by the time this report was printed. Guardicore is scheduling to launch far more facts as a followup to the paper it launched this week.
How to Plug the Leaks
Regretably, the information is not excellent for the standard public: Just after all, Autodiscover was built to spare them from sinking up to their elbows in the guts of email consumer configuration, and mitigation requires rolling up shirtsleeves. But for buyers who really do not mind plunging in, Guardicore did offer these protecting measures:
- Make guaranteed that you are actively blocking Autodiscover. domains (these kinds of as Autodiscover.com/Autodiscover.com.cn, and so forth) in your firewall.
- When deploying/configuring Exchange setups, make sure that assist for essential authentication is disabled – employing HTTP fundamental authentication is the very same as sending a password in clear text around the wire.
- A detailed textual record of all major stage domains can be located in the following url: https://data.iana.org/TLD/tlds-alpha-by-area.txt
- We have prepared a txt file with all feasible Autodiscover.TLD domains which can be included to your area hosts file or firewall configuration in purchase to mitigate the risk of having these types of Autodiscover domains resolve. Make sure you verify our github repository for additional information:
https://github.com/guardicore/labs_strategies/tree/master/Autodiscover
- We have prepared a txt file with all feasible Autodiscover.TLD domains which can be included to your area hosts file or firewall configuration in purchase to mitigate the risk of having these types of Autodiscover domains resolve. Make sure you verify our github repository for additional information:
For developers and vendors, the business made available this tip:
- Make positive that when you are utilizing the Autodiscover protocol in your item you are not permitting it “fail upwards”, this means that domains such as “Autodiscover.” need to by no means be made by the “back-off” algorithm.
The Buck Stops With Microsoft
Saryu Nayyar, CEO of risk-analytics supplier Gurucul, explained to Threatpost that we can all thank our lucky stars that the qualifications had been grabbed by Guardicore – the “good guys,” as she referred to as them.
“That doesn’t indicate that we can relaxation simple, nonetheless,” she cautioned. “If scientists understand the character of the vulnerability and know how to exploit it, it’s a small backlink to attackers exploiting it. Individuals corporations making use of specific security analytics can very easily decide if a login or access request is legit and examine and remediate if important. This is a crystal clear and critical weakness, but a single that businesses can detect and react to.”
Alicia Townsend, technology evangelist at id and accessibility administration organization OneLogin, told Threatpost that it would seem “incredible” that a products would deliver a user’s username and password to an untrusted endpoint.
“The fact that this is going on with an very popular Microsoft product these as Exchange is even much more disheartening,” she mentioned. “But it’s possible the response lies in the point that it is taking place in a product that has been all around for so prolonged.”
Townsend pointed out it’s not very clear how extended this structure flaw has been all-around, provided that the Trade Autodiscover feature was launched in Exchange 2007. Possibly way, it does not glow a fantastic light-weight on Microsoft. “Whether the oversight was on the aspect of early builders or was launched by a lot more new developers, it is very clear that Security To start with was not their primary aim,” she stated.
Nevertheless, the buck stops in Redmond, Townsend stated. “It is the responsibility of all program makers equally on prem and in the cloud to make sure that their developers are educated on how to produce and take a look at for safe code. We need to have to be regularly assessing our products for feasible security risks. We need to have to consider not just new operation but current performance, mainly because as we can see with the Exchange Autodiscover element, anything could have been created into the element yrs in the past and no 1 has been conscious of it. Clients set their belief in us and we will need to be at any time vigilant.”
Rule #1 of Linux Security: No cybersecurity solution is feasible if you don’t have the principles down. Be part of Threatpost and Linux security pros at Uptycs for a Live roundtable on the 4 Golden Regulations of Linux Security. Your major takeaway will be a Linux roadmap to receiving the essentials right! Sign-up NOW and join the Reside celebration on Sept. 29 at Midday EST. Becoming a member of Threatpost is Uptycs’ Ben Montour and Rishi Kant who will spell out Linux security best methods and just take your most pressing questions in serious time.
Some areas of this report are sourced from:
threatpost.com


 Florida Yet to Spend $30M Allocated for Cybersecurity
Florida Yet to Spend $30M Allocated for Cybersecurity