Scientists have located an fully new attack vector for eavesdropping on Zoom and other digital meetings.
Digital conferences are vulnerable to a new, exotic attack termed Glowworm, which actions an audio output device’s LED power mild variations and converts them to audio reproductions — enabling cyberattackers to listen to delicate discussions.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
As an expanding total of business is currently being done about platforms like Microsoft Teams, Zoom, Skype and some others, the results current an fully new attack vector for these electronic communications.
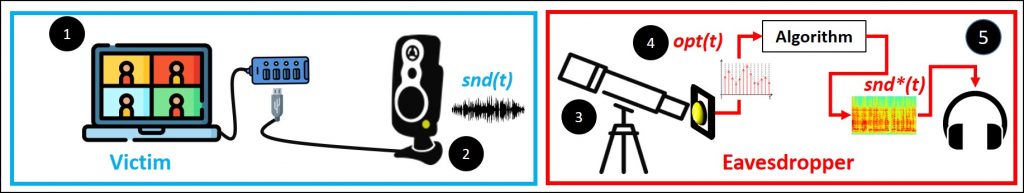
A crew of researchers at Ben-Gurion College have revealed a paper on the Glowworm vector, which is technically acknowledged as a Telecommunications Electronics Content Protected from Emanating Spurious Transmissions (TEMPEST) attack — the U.S. Countrywide Security Agency designation for unintended digital alerts which can be picked up and utilized to compromise data security.
Federal agencies are expected to guard labeled details from TEMPEST attacks.
In this circumstance, the spurious transmission is a virtually imperceptible flicker on a speaker, USB hub, splitters or microcontroller LED electrical power.
“By exploiting imperceptible variations in the intensity of a device’s energy indicator LED, which are induced by the improvements in the device’s electricity consumption, Glwowworm is capable of recovering speech,” the crew defined in a movie accompanying the launch of their paper.
“Our experiments present that several merchandise of many manufacturers are susceptible to the Glowworm attack,” the group discussed.
Glowworm Experiment
The scientists shown how a Glowworm attack might perform by pointing a telescope with an electro-optical sensor from 35 meters absent at speakers linked to laptop computer. The sensor was aimed at the speakers’ electrical power-indicator LED and the laptop computer display screen was not visible.
The group was efficiently equipped to capture a statement performed on the speakers and translated by Glowworm.
Supply: Ben Gurion College.
While most business enterprise remaining executed above platforms like Skype is considerably from sensitive sufficient to attract eavesdroppers armed with telescopes and Glowworm, the finding is a excellent reminder that manufacturers simply cannot always be relied upon to think about these kinds of TEMPEST attacks, regardless of the government’s ideal attempts.
“This is a pretty appealing attack that for the mind-boggling number of people has no genuine risk,” John Bambenek from Netenrich told Threatpost in response to the paper. “That mentioned, for devices and environments the place espionage is critical, actual physical security continues to be crucial. No visibility from unprotected area should be probable into very delicate environments and units should really be created to be segmented so delicate information and facts just can’t be gleaned since suppliers were as well lazy to put LEDs on a clear line in the box.”
Worried about where the subsequent attack is coming from? We have bought your back. REGISTER NOW for our approaching stay webinar, How to Assume Like a Risk Actor, in partnership with Uptycs. Come across out exactly the place attackers are targeting you and how to get there first. Be a part of host Becky Bracken and Uptycs researchers Amit Malik and Ashwin Vamshi on Aug. 17 at 11AM EST for this LIVE discussion.
Some components of this report are sourced from:
threatpost.com


 Martial Arts Instructor Accused of Spying on Students
Martial Arts Instructor Accused of Spying on Students