At SAS@Household, Luta Security CEO Katie Moussouris pressured that bug bounty plans are not a ‘silver bullet’ for security groups.
SAS@Residence 2020– Right after a Grindr security flaw was disclosed this 7 days, the relationship internet site promised it would start a bug-bounty system in an exertion to “[keep its] company secure.” But Katie Moussouris, CEO of Luta Security and a bug bounty software pro, warned at this week’s SAS@house digital celebration that basically launching a bug-bounty system will not final result in improved security.
The Grindr bug, which allowed attackers to launch password resets without accessing a user’s email inbox, designed information headlines as it was incredibly trivial to exploit. Talking through a Tuesday virtual session, Moussouris said that if businesses have that stage of “low-hanging fruit” when it arrives to vulnerabilities, bug-bounty packages can in some cases pose much more complications than they fix.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“We have a lot of hope for bug-bounty courses, but they are not the ‘easy button’ we considered they were being,” she claimed, speaking on Tuesday at SAS@Dwelling, which is Kaspersky’s digital Security Analyst Summit meeting.
Grindr isn’t alone – lots of businesses are on the lookout to adopt, or have already adopted, bug-bounty packages or vulnerability-disclosure programs (VDPs). It is significant to distinguish the two: A bug-bounty method gives funds rewards for discovering flaws (which in idea must then be fixed by the corporation), even though a VDP handles when a vulnerability is documented by a 3rd social gathering to an corporation. Ideally, people associated would stick to the ISO requirements for vulnerability disclosure (ISO 29147) and vulnerability managing (ISO 30111) processes.
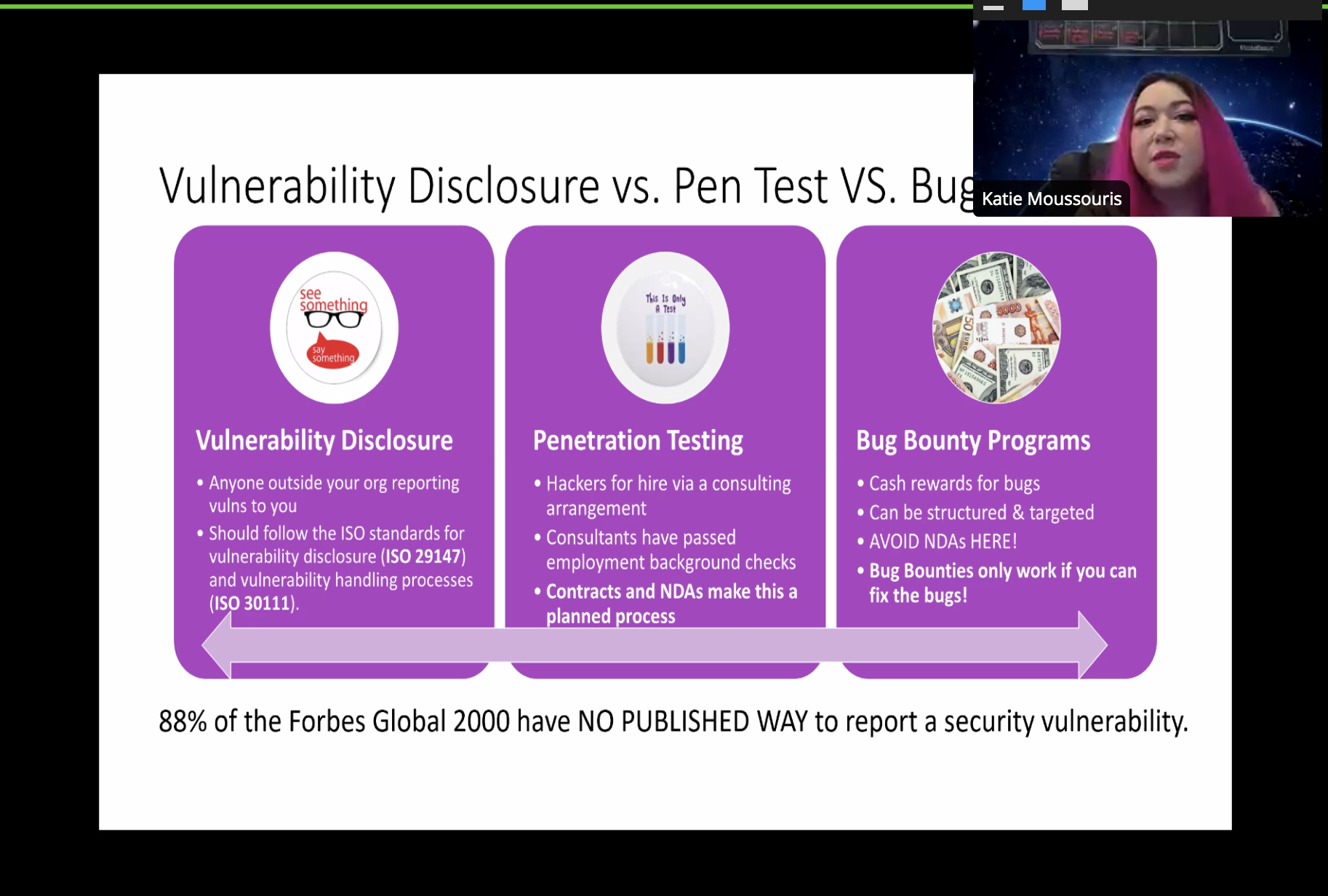
Katie Moussouris talks about the separate definitions of VDPs, bug-bounty courses and pentesting through SAS@Household.
But corporations are rushing in to undertake bug-bounty programs and VDPs without the need of first fleshing out crucial issues — irrespective of whether that’s defining what is in scope, hunting at how an group can take care of an influx of vulnerabilities staying noted, or effectively coaching triage teams.
In December, for instance, a CISA directive was proposed that would demand all U.S. organizations to establish and put into practice vulnerability disclosure processes for their internet-connected techniques. Whilst CISA advised that companies take into consideration steering all-around what’s in-scope and who to call, Moussouris mentioned that holes remained in conditions of placing up the back again-conclusion processes to receive reports, or gaining the means that are needed to repair the bugs claimed.
Another prospective issue that quite a few organizations fail to remember about is acquiring the ideal instruments and methods to deal with a possible influx of vulnerabilities claimed, as observed with Zoom. Even though Zoom had a bug-bounty platform at a single place, it was not equipped to deal with the security issues that arrived with a flood of distant workforces employing its system all through the pandemic. Immediately after troves of security vulnerabilities had been found out in the on line video conferencing platform, Zoom announced it would revamp its bug-bounty program with the assist of Moussouris.
Moussouris proposed that organizations looking to apply bug-bounty systems and VDPs will need to do the prerequisite function and deal with their vulnerability processes internally. Although performing with Zoom for instance, she served bolster the team’s interior assets so that it was greater geared up to tackle reports internally.
And last but not least, Moussouris encouraged that businesses remember that “security is an ongoing journey” and that there is no silver bullet.
“People wondering VDP is a great to start with phase for bug bounty plans have got it backwards,” she mentioned. “Secure deployment [is] a fantastic first phase – not casting it out in the planet and anticipating results.”
On Oct 14 at 2 PM ET Get the newest details on the increasing threats to retail e-commerce security and how to end them. Register today for this Free of charge Threatpost webinar, “Retail Security: Magecart and the Increase of e-Commerce Threats.” Magecart and other threat actors are riding the soaring wave of on the web retail utilization and racking up massive numbers of consumer victims. Discover out how websites can prevent starting to be the subsequent compromise as we go into the getaway time. Be part of us Wednesday, Oct. 14, 2-3 PM ET for this LIVE webinar.
Some areas of this report are sourced from:
threatpost.com

 Male Chastity Device Comes with Massive Security Flaws
Male Chastity Device Comes with Massive Security Flaws