The ransomware gang promises to have pulled off thriving attacks in opposition to two airways and 1 airport with help from its Accenture attack.
Soon after Bangkok Airways disclosed that it experienced been clobbered by a cyberattack previous week, the LockBit 2. ransomware gang tossed its have countdown clock in the trash and went ahead and revealed what it statements are the airline’s encrypted information on its leak web-site.
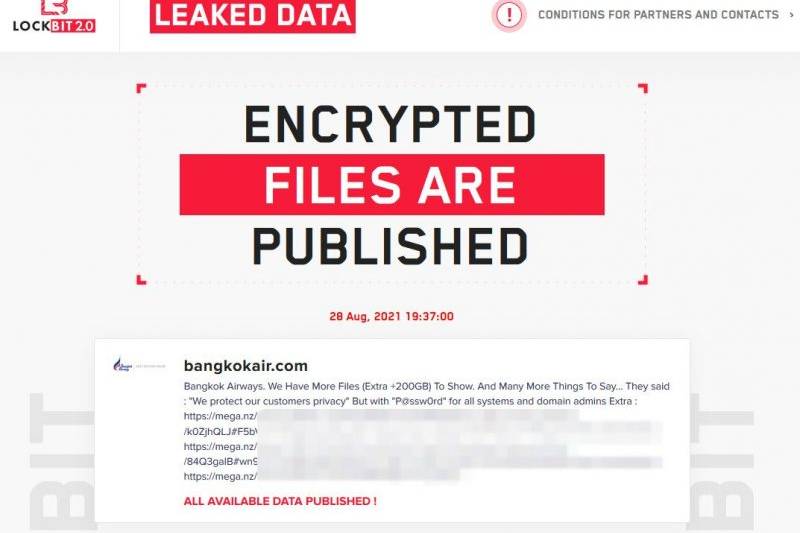
BleepingComputer posted an picture (demonstrated under) of LockBit’s “Encrypted Documents Are Published” write-up, dated Saturday, Aug. 28, 19:37:00. That’s three days previously than its original countdown clock: In that publish, the ransomware-as-a-service (RaaS) gang promised that encrypted documents would be printed yesterday (Tuesday) if the airline did not spend the ransom. The sum of the demanded extortion hasn’t been reported.Saturday’s LockBit publish reads:

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“Bangkok Airways. We Have Far more Information (More +200GB) To Present And Several Additional Items To Say … They said : We secure our clients privacy” But with P@ssw0rd for all program and domain admins Excess :”
The submit involved a series of redacted inbound links.
Screen seize from LockBit 2.0’s leak web page. Resource: BleepingComputer.
The news outlet, which has been speaking with the gang, described that ahead of LockBit went right after Bangkok Airways on Aug. 23, the team also published encrypted information from yet another airline: Ethiopian Airlines.
The risk actor explained to the publication that the Accenture breach from earlier this thirty day period yielded the qualifications made use of in each of the airline attacks. LockBit also claimed to have encrypted the devices of an unnamed airport employing Accenture program.
Bangkok Airways Breach
Bangkok Airways introduced the breach past 7 days, on Thursday, and LockBit 2. begun a countdown clock the subsequent day. In its preliminary article, the gang claimed to have stolen 103GB really worth of compressed data files that it would release yesterday, on Tuesday, and that they experienced a great deal much more – people +200GB of information it pointed out once again in Saturday’s write-up – that they could incorporate to the distress.
Bangkok Airways mentioned at the time it disclosed the Aug. 23 attack that it’s doing work on beefing up its defenses.
The breach involved many own details belonging to passengers, like:
- Passenger identify
- Family members identify
- Nationality
- Gender
- Phone amount
- Email address
- Other make contact with information
- Passport data
- Historic vacation info
- Partial credit rating-card information
- Unique meal information and facts
The attackers evidently did not deal with to accessibility Bangkok Airway’s operational or aeronautical security systems, the firm said in its general public disclosure.
Accenture Breach Could Unfold Far Far more Ripples
Before this thirty day period, LockBit attacked Accenture, a global organization consulting business with an insider monitor on some of the world’s most significant, most powerful corporations. It’s hardly astonishing that airlines (and, heading by what LockBit claimed, at the very least just one airport) have seemingly fallen prey to LockBit, provided the cornucopia of credentials the gang presumably drained out of Accenture.
Accenture’s clients incorporate 91 of the Fortune World 100 and much more than 3-quarters of the Fortune Global 500. According to its 2020 annual report, that incorporates e-commerce giant Alibaba, Cisco and Google. Valued at $44.3 billion, Accenture is a person of the world’s premier tech consultancy corporations, and employs about 569,000 people throughout 50 international locations.
These corporations must be anxious, to say the the very least. Not only did their security supplier get drained, so perhaps compromising an untold variety of its clients, but it received drained by a team with an progressively effective arsenal: According to a report released not long ago by Pattern Micro, attacks in July and August have employed LockBit 2. ransomware that element a souped-up encryption process.
Check out our free of charge approaching dwell and on-need webinar activities – one of a kind, dynamic discussions with cybersecurity authorities and the Threatpost community.
Some parts of this write-up are sourced from:
threatpost.com

 Cybercriminals Abusing Internet-Sharing Services to Monetize Malware Campaigns
Cybercriminals Abusing Internet-Sharing Services to Monetize Malware Campaigns