Researchers from Sucuri found out the tactic, which creatively hides destructive activity until eventually the facts can be retrieved, for the duration of an investigation into a compromised Magento 2 e-commerce website.
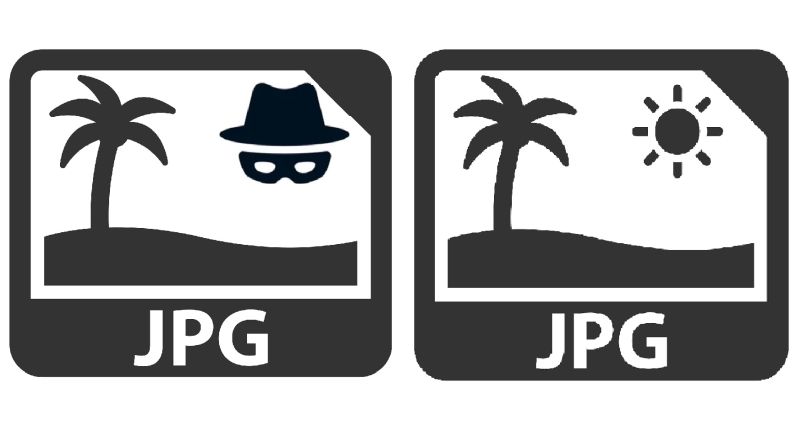
Magecart attackers have observed a new way to disguise their nefarious on the web action by saving facts they’ve skimmed from credit history playing cards on the internet in a .JPG file on a web site they’ve injected with malicious code.
Scientists at site security firm Sucuri identified the elusive tactic just lately for the duration of an investigation into a compromised web site using the open up-source e-commerce platform Magento 2, Luke Leal from Sucuri’s malware investigate staff said in a report posted on line final 7 days.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“The artistic use of the phony .JPG allows an attacker to conceal and retail store harvested credit score card details for upcoming use with out attaining as well significantly consideration from the web site proprietor,” he wrote.
Peering beneath the hood of the compromised site exposed a destructive injection that was capturing Submit request info from web site website visitors, Leal stated. “Located on the checkout page, it was uncovered to encode captured info right before conserving it to a .JPG file,” he wrote.
A Post request process asks a web server to accept info enclosed in the entire body of the request message, typically so it can be stored. It’s often utilized in Web transactions when an individual has uploaded a file to a website or submitted a done web sort.
Particularly, Sucuri identified that attackers injected PHP code into a file termed ./vendor/magento/module-client/Model/Session.php, then utilised the “getAuthenticates” perform to load malicious code, Leal mentioned. The code also made a .JPG file, which attackers applied to retailer any knowledge they captured from the compromised web-site, he said.
“This attribute lets the attacker to effortlessly accessibility and obtain the stolen details at their ease when concealing it inside a seemingly benign JPG,” Leal wrote.
Certainly, menace actors aiming to steal details from on-line transactions are regularly hoping to find new methods to evade detection by concealing their activity in artistic ways.
Magecart attackers–different menace teams who all compromise e-commerce internet websites with card-skimming scripts on checkout web pages to steal shopper payment and own data–are specially adept at this exercise. They normally disguise their skimming procedures in operation that appears reliable as properly as use the platforms they attack to cannibalize themselves to obtain their effects.
A Magecart campaign identified all around Christmastime, for instance, concealed itself inside of convincing PayPal iframes in the PayPal checkout process of e-commerce sites to steal person credentials and credit-card data.
The most up-to-date campaign also leveraged the Magento code framework to do its soiled function of harvesting the information captured and concealed in the .JPG file, Leal described. The malicious PHP code relied on the Magento operate “getPostValue“ to seize the checkout page facts in just the “Customer_ Article parameter,” he mentioned.
It also utilised the Magento function “isLoggedIn” to check irrespective of whether a target is logged into the internet site as a consumer and, if this was the case, attackers also elevate the user’s email handle from the transaction, he reported.
“Nearly all of the details submitted by the sufferer on the checkout page is saved within just the ‘Customer_ parameter,’ which includes total names and addresses, payment card particulars, telephone figures, and consumer agent specifics,” he wrote.
After attackers get their hand on client payment facts, they can then go on to use it for numerous criminal pursuits, this sort of as credit score-card fraud or qualified e-mail-based mostly spam or phishing strategies, Leal included.
When this newest Magecart anti-detection technique may make the infection difficult to at first location, it would assist site owners to recognize new data files in the environment or detect possibly destructive alterations right before they do hurt if they apply web-site checking solutions or integrity command checks, Sucuri recommended.
Examine out our free upcoming live webinar events – special, dynamic discussions with cybersecurity experts and the Threatpost neighborhood:
- March 24: Economics of -Working day Disclosures: The Fantastic, Terrible and Unsightly (Learn additional and sign up!)
- April 21: Underground Marketplaces: A Tour of the Dark Financial state (Study additional and sign up!)
Some parts of this short article are sourced from:
threatpost.com

 UK Nurseries Get First Official Cyber-Attack Warning
UK Nurseries Get First Official Cyber-Attack Warning