Two flaws – just one of them nevertheless to be preset – are afflicting a third-celebration plugin used by Magento e-commerce web sites.
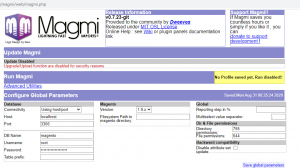
Researchers have disclosed two flaws that could allow distant code execution assaults on the Magento Mass Import (Magmi) plugin, an open source databases consumer that imports information into Magento.
Magmi is a Magento database client prepared in PHP, which is utilized to conduct raw bulk operations on the types of an online store. A patch has only been published for one particular of the two flaws (CVE-2020-5777), in Magmi model .7.24, Sunday. At the time of disclosure, however, there was however no patch accessible for two 2nd flaw (CVE-2020-5776), reported researchers.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Satnam Narang, staff members investigation engineer at Tenable, told Threatpost that scientists just can’t definitively say how several Magento web-sites are susceptible – on the other hand, they were being ready to detect at least 1,500 web sites indexed by way of research engines that use the Magmi plugin (and it is probably there are a lot more).
“To minimize your risk in the meantime, we endorse disabling or uninstalling the plugin completely right until a patch is obtainable, as very well as refraining from active web browsing even though authenticated to Magmi,” reported researchers with Tenable in a Tuesday article.
Scientists on Tuesday also produced proof-of-thought (PoC) exploit code on GitHub for equally of the flaws.
The Flaws
The unpatched flaw, CVE-2020-5776, is a cross-internet site ask for forgery (CSRF) vulnerability affecting Magmi up to model .7.24. While this flaw has a CVSSv2 rating of 6.8 out of 10 (building it medium severity), vulnerability databases VulDB classified it as critical.
The flaw, which impacts an mysterious functionality of a unique file (/index.php/newsletter/subscriber/new/), exists due to the fact the GET and Post endpoints for Magmi really do not carry out CSRF defense – which means an attacker could exploit the flaw vulnerability to carry out a CSRF attack. CSRF takes place when a destructive web site sends a request to a web application that a victim is presently authenticated in opposition to. This way an attacker can access the features in a target web software by way of the victim’s now authenticated browser.
In this unique attack, risk actors could trick a Magento Administrator into clicking on a backlink when they are authenticated to Magmi. The attacker could then hijack the administrator’s sessions, allowing for them to execute arbitrary code on the server where by Magmi is hosted, scientists explained.
The second, now patched flaw, CVE-2020-5777, is an authentication bypass flaw in Magmi for Magento variation .7.23 and underneath. This flaw also has a CVSSv2 rating of 6.8 out of 10, creating it medium severity, researchers explained to Threatpost.
Magmi’s authentication process takes advantage of HTTP Basic authentication and checks the username and password from the Magento database’s admin_user table. On the other hand, if the link to the Magento databases fails, Magmi will acknowledge default credentials, which are magmi:magmi.
“As a consequence, an attacker could power the databases link to fail because of to a databases denial of assistance (DB-DoS) attack, then authenticate to Magmi making use of the default qualifications,” claimed researchers. “The affect of this attack is distant code execution (RCE) on the server in which Magmi is hosted.”
Researchers properly performed a Magento DB-DoS attack when the utmost selection of concurrent MySQL connections was greater than the highest range of concurrent Apache HTTP connections.
“By sending a substantial selection of concurrent connection requests that exceed the MySQL connections limit, but not the optimum Apache HTTP relationship limit, attackers could quickly block entry to the Magento databases and simultaneously make an authenticated request to Magmi applying the default credentials,” explained scientists.
Disclosure
Researchers said that they achieved out to the developer of the Magmi plugin on June 3. Following adhere to-up communications on June 17 and July 6, they been given acknowledgement on July 6 that the discovered issues were in the course of action of being set.
“We have given that sent requests for updates and have not been given any. Nonetheless, the developers introduced a new edition of the plugin on August 30 to deal with one particular of the two vulnerabilities (CVE-2020-5777),” they explained.
“This launch fixes a security issue owing to a possible exploit on Magmi default authentication,” according to Magmi’s description of its most up-to-date edition, 7.24. Threatpost has arrived at out to the developers of Magmi for more comment.
It’s not the first time that the Magento open up-source e-commerce platform has confronted security issues because of to third-get together plugins (as properly as flaws in Magento itself). An FBI flash security alert that became community in Could 2020 regarding in-the-wild exploitation of CVE-2017-7391, a cross-web page scripting vulnerability in Magmi that was utilised to target vulnerable Magento internet sites. In 2018, attackers used a couple of IP addresses to scan for vulnerable versions of Magmi.
On Wed Sept. 16 @ 2 PM ET: Learn the tricks to operating a thriving Bug Bounty Plan. Register today for this FREE Threatpost webinar “Five Essentials for Working a Effective Bug Bounty Program“. Hear from top Bug Bounty System experts how to juggle public compared to personal packages and how to navigate the tough terrain of managing Bug Hunters, disclosure guidelines and budgets. Join us Wednesday Sept. 16, 2-3 PM ET for this LIVE webinar.


 Beware CISOs: attack vectors are coming from within the household
Beware CISOs: attack vectors are coming from within the household