AgentTesla, LimeRAT, W3Cryptolocker and Redline Stealer are now applying Paste.nrecom in spear-phishing attacks.
Cybercriminals are progressively turning to a legit, Pastebin-like web company for downloading malware — these types of as AgentTesla and LimeRAT — in spear-phishing assaults.
Pastebin, a code-hosting services that enables end users to share plain textual content by way of community posts called “pastes,” presently has 17 million unique regular monthly users and is popular among cybercriminals (such as the FIN5 APT team and Rocke danger team) for hosting their payloads or command-and-command (C2) infrastructure. But now, extra malware and ransomware households are commencing to benefit from yet another assistance, with the area Paste.nrecom[.]net.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
This service been all over given that Could 2014, and has a related functionality as Pastebin. It also has an API (driven by open-resource PHP based pastebin Stikked) that makes it possible for for scripting. Researchers with Juniper Networks reported that the API element is valuable for cybercriminals, who can leverage it to simply insert and update their details programmatically.

“Although working with authentic web solutions is not novel, this is the 1st time that we have witnessed threat actors use paste.nrecom[.]net,” stated Paul Kimayong, researcher with Juniper Networks, in a Monday evaluation. “Among the malware we have determined are AgentTesla, LimeRAT, [W3Cryptolocker] Ransomware and Redline Stealer.”

The amount of malware family members utilizing the new Pastebin-like assistance. Credit: Juniper Networks
Researchers said that the attacks using the company normally start with a spear-phishing email that consists of an attachment (these kinds of as a document, archive or an executable). The recipient is tricked into opening a malicious attachment (as the very first phase of the attack), which then downloads the following levels from paste.nrecom[.]internet.
“We have also seen malware hosting their configuration info in the very same assistance,” explained scientists.
AgentTesla is the most energetic malware loved ones working with this provider, researchers claimed. The spy ware is able of thieving personalized facts from web browsers, mail shoppers and FTP servers, as perfectly as amassing screenshots and video clips, and capturing clipboard data.
Scientists highlighted particular AgentTesla strategies that concentrate on various industries associated to delivery, supply chains and banking companies, applying spear-phishing email messages with archive attachments (these types of as .iso, .rar or .uue). These attachments, as soon as opened, then put in AgentTesla utilizing paste.nrecom.
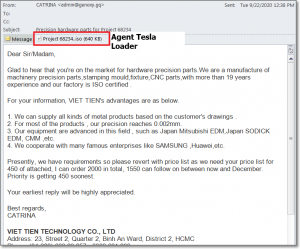
The AgentTesla malware attack that uses paste.nrecom. Credit: Juniper Networks
The builders of LimeRAT, an open up-source distant administration trojan coded in .Net (used just lately by the APT-C-36 team to concentrate on Colombian authorities institutions) have also utilized the web services to down load malware.
Other, more recent malware and ransomware are also turning to paste.nrecom. A single of these is W3Cryptolocker, a rather new ransomware that surfaced in July. Scientists discovered that the preliminary-phase loader was hosted on a most likely hacked web page, italake.com. When the loader was downloaded, W3Cryptolocker was executed, right after which it encrypted most information in all drives and created a “Read_Me.txt” file on just about every folder with the ransom message.
And, Redline Stealer, a malware that surfaced as just lately as March and has focused healthcare and production companies in the U.S., also tends to make use of the support. Scientists explained they identified samples posing as a Bitcoin miner archived into a RAR file. The RAR file contained an executable (MinerBitcoin.exe) that downloaded the Redline Stealer payload from paste.nrecom.
Looking in advance, scientists warned that a lot more malware family members will flip to authentic web providers to host their destructive infrastructure.
“Using legitimate web-expert services like pastebin or paste.nrecom for malware infrastructure provides cybercriminals an advantage, as these services cannot be easily taken down because of to their authentic use,” explained researchers.
On October 14 at 2 PM ET Get the hottest information and facts on the climbing threats to retail e-commerce security and how to prevent them. Register today for this No cost Threatpost webinar, “Retail Security: Magecart and the Rise of e-Commerce Threats.” Magecart and other menace actors are driving the soaring wave of on the net retail usage and racking up massive numbers of customer victims. Obtain out how web sites can avoid turning into the up coming compromise as we go into the vacation time. Be part of us Wednesday, Oct. 14, 2-3 PM ET for this LIVE webinar.
Some areas of this write-up are sourced from:
threatpost.com


 Rare Bootkit Malware Targets North Korea-Linked Diplomats
Rare Bootkit Malware Targets North Korea-Linked Diplomats