“I am thoroughly screwed,” 1 consumer wailed after discovering a long time of information nuked. Western Digital recommended yanking the NAS storage units offline ASAP: There is an exploit.
If you have not previously, halt looking at and go yank your My E-book Reside storage unit offline, lest you join the ranks of those who woke up on Thursday to obtain that decades of info had been wiped clean up on products all-around the earth.
Western Digital’s My Book storage device is intended for buyers and companies. It usually plugs into personal computers through USB. The precise model involved in the info-demolition incident is regarded as My E book Dwell: a product that works by using an Ethernet cable to link to a area network. Customers can remotely obtain documents and make configuration alterations by way of Western Digital’s cloud infrastructure.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Western Digital is blaming the remote wipes – which have took place even if the network-connected storage (NAS) units are at the rear of a firewall or router – on the exploitation of a distant command-execution (RCE) vulnerability.
The compromise delivers the data slaughter in the form of a factory reset that “appears to erase all knowledge on the device,” in accordance to Western Digital’s advisory.
It was BleepingComputer’s Lawrence Abrams that 1st arrived across the issue remaining reported on the Western Digital community forum. A single user applying the manage “sunpeak” claimed that their folders all had an edit date of June 23 (Wednesday), all over 3 p.m. PT/6 p.m. ET. Scores of other discussion board customers verified obtaining the factory-reset messages, and verified the timing.
Sunpeak went on to explain how they learned that 2T of facts – an nearly complete disk – went up in a puff of smoke, leaving the directories continue to there but echoing, all emptied out.
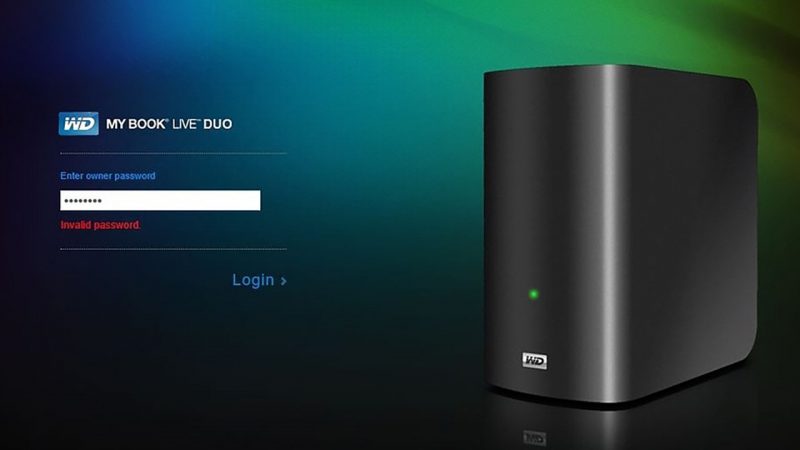
“Previously the 2T quantity was nearly comprehensive but now it shows comprehensive ability,” sunpeak claimed, likely on to explain how, on striving to login to the management consumer interface to diagnose the issue, they were being only equipped to get to the landing website page shown under, which prompted them to input their “owner password.”

The WD My Ebook landing page consumers observed after their devices had been wiped. Supply: WD Neighborhood discussion board.
When sunpeak tried to input the default password “admin,” it did not perform. Nor did the landing webpage give the possibility of resetting or retrieving the password.
The person wrote that it is “very scary” that a risk actor could perform a manufacturing unit reset on drives without the need of authorization granted by close users. Sunpeak available up these entries from their drive’s consumer.log:
Jun 23 15:14:05 MyBookLive factoryRestore.sh: start out script:
Jun 23 15:14:05 MyBookLive shutdown[24582]: shutting down for process reboot
Jun 23 16:02:26 MyBookLive S15mountDataVolume.sh: begin script: get started
Jun 23 16:02:29 MyBookLive _: pkg: wd-nas
Jun 23 16:02:30 MyBookLive _: pkg: networking-common
Jun 23 16:02:30 MyBookLive _: pkg: apache-php-webdav
Jun 23 16:02:31 MyBookLive _: pkg: day-time
Jun 23 16:02:31 MyBookLive _: pkg: alerts
Jun 23 16:02:31 MyBookLive logger: hostname=MyBookLive
Jun 23 16:02:32 MyBookLive _: pkg: admin-relaxation-api
“I feel this is the offender of why this occurs,” sunpeak wrote. “No one particular was even property to use this push at this time.”
Years of Information: Now Toast
Some of the wails of discomfort that arose from Western Digital people on the discussion board:
I’m not heading to lie, I have been in tears about this really much all day. I started out a new occupation 7 months ago and all my information/function was on here (indeed, this was not backed up as I only do again ups each and every 6 months or so and it’s been chaotic :frowning: ). I cannot beleive [sic] this has took place, it doesn’t seem to be genuine, but I will absoutely [sic] pursue each and every avenue I can to get them to at least tell me what they’ve done so I can instruct expert details recovery services (and then I will do all i can to keep them to account as perfectly. P***** off is an understatement). —Sammie101
All my data is long gone as well. Concept in GUI claims it was “Factory reset” these days! 06/23. I am entirely screwed without the need of that data…years of it. —Marknj1
Dusty Devices, Old Firmware
Western Electronic stopped supporting My Ebook Stay in 2015. That was the date of the last firmware update for its My Guide Reside and My Book Stay Duo equipment, according to its advisory. The firm gave the compulsory “customers’ details is really important” information and reported that it is “actively investigating the issue.” Western Electronic promised to update its advisory when it has more data.
Western Digital despatched a assertion to information outlets, such as Ars Technica, declaring that the firm has no indications that its cloud products and services or methods ended up breached:
The incident is beneath active investigation from Western Electronic. We do not have any indications of a breach or compromise of Western Electronic cloud products and services or devices.
We have identified that some My E-book Dwell units have been compromised by a risk actor. In some cases, this compromise has led to a manufacturing facility reset that appears to erase all information on the product. The My Book Are living system acquired its closing firmware update in 2015.
At this time, we are recommending that prospects disconnect their My Ebook Dwell devices from the Internet to safeguard their knowledge on the unit.
We…will provide updates to this thread when they are out there.
Threatpost has achieved out to Western Electronic for an update on the investigation.
Be part of Threatpost for “Tips and Ways for Improved Menace Hunting” — a Are living event on Wed., June 30 at 2:00 PM ET in partnership with Palo Alto Networks. Learn from Palo Alto’s Unit 42 specialists the best way to hunt down threats and how to use automation to enable. Sign up Right here for no cost.
Some sections of this posting are sourced from:
threatpost.com

 Western Digital: Disconnect My Book Live drives immediately
Western Digital: Disconnect My Book Live drives immediately