A researcher hacked Nespresso Pro intelligent playing cards to dispense free of charge, limitless espresso.
Researchers have demonstrated how to outsmart Nespresso Pro equipment that use sure clever playing cards, hacking them to dispense espresso on-demand from customers.
Nespresso makes a variety of coffees and devices for own and specialist use. Some of the professional devices take Mifare Traditional stored-value wise playing cards, which let people to load revenue on to the playing cards to use in the equipment. The cards having said that have been extensively panned as lacking in security for at least the previous 12 many years. In 2008, a paper entitled Dismantling Mifare Common was posted, flagging a lot of issues.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
But, that did not prevent Nespresso from working with the playing cards with its Nespresso Pro community equipment, which are installed through Europe — inspite of current possibilities becoming offered, like the Mifare Moreover clever cards , according to researcher Polle Vanhoof.
He added that storing the funds on the card, fairly than on a again-conclude server, would seem to be to make sense on the area.
“This is a much more simple and expense-effective style, requiring fewer hardware and software to put into practice, earning it a likely alternative for anybody developing this kind of a process unaware of the security weaknesses of the Mifare Traditional,” Vanhoof stated in the disclosure.
Vanhoof found that he could simply crack the intelligent card and include endless funds to be used in the espresso dispensers.
Threatpost achieved out to Nespresso for comment but has not but heard back.
A Total Latte Security Flaws
Vanhoof spelled out that he applied mfoc, a resource to crack the Mifare Vintage chip’s encryption and shift the contents of the info to a individual file.
“While attempting to crack the keys for the Nespresso cards I encountered some bugs that would avoid the application from appropriately dumping the keys,” Vanhoof stated. “I mounted the issues and submitted a pull request… but I do not assume that it will be merged specified the condition of the repository.”
Vanhoof directed other scientists performing this style of work to use a patched model.
He then ran the mfoc instrument to crack non-default keys with the command [mfoc -P 500 nespressp.dmp].
“Before we carry on, we manually seize the keys that were uncovered and add them to a file [keys.txt], Vanhoof additional. “That way we can feed them into the instrument and skip the cracking element for subsequent dumps.”
He loaded the card with €1.50 and produced a binary dump applying the earlier keys. Then he purchased espresso from a Nespresso equipment, dropping the card’s benefit and manufactured one more dump for comparison to obtain the revenue bytes in the code.
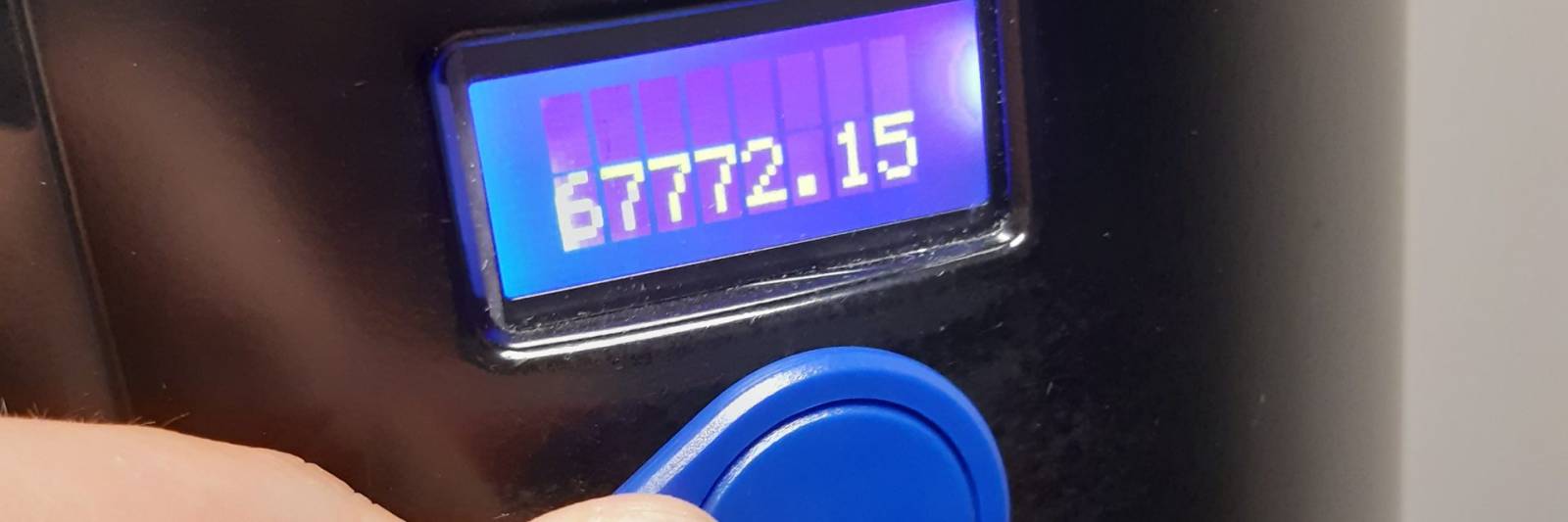
“After executing some a lot more testing and debugging, we arrive to the summary that the card employs 3 bytes to characterize the complete financial worth on the card,” Vanhoof mentioned. “The optimum doable amount of money of revenue on a single of these playing cards is therefore €167.772,15.”
Employing the [nfc-mfclassic] instrument, Vanhoof was then equipped to increase cash back again on to the card.
To take care of the bug, Vanhoof explained Nespresso customers really should update their smart cards. He extra that updating the equipment so that revenue values are saved on a centralized server, alternatively than the card by itself, would be a huge improvement.
“After conversing to Nespresso, it looks they presently provide both equally of these solutions,” Vanhoof stated. “Clients involved with the security of their programs should appear into these choices.”
Down load our unique Totally free Threatpost Insider E-book Healthcare Security Woes Balloon in a Covid-Era World, sponsored by ZeroNorth, to study more about what these security threats mean for hospitals at the day-to-day stage and how healthcare security groups can put into practice finest practices to defend providers and people. Get the complete story and Obtain the E-book now – on us!
Some parts of this article are sourced from:
threatpost.com

 DDoS attacks leverages Plex media server
DDoS attacks leverages Plex media server