Misconfigured APIs make any app dangerous, but when you are chatting about economic applications, you are speaking about handing ne’er-do-wells the electric power to change your pockets within-out.
App builders have at the time yet again been accused of obtaining butterfingers when it comes to API keys, leaving millions of cell app end users at risk of exposing their personalized and payment details.
CloudSEK, maker of synthetic intelligence- (AI-) enabled digital danger defense, described previous week that the cell ecosystem is reeking with tricky-coded API keys: Keys that ought to under no circumstances be uncovered in endpoint applications.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Misconfigured APIs make any application dangerous, but when you are speaking about financial apps, it is about handing ne’er-do-wells the electrical power to change victims’ pockets inside-out.
“While the rampant exposure of API keys is hazardous for any application, it is specifically critical when it will come to applications that take care of payment details this sort of as bank aspects, credit score card information and facts and UPI transactions, in addition to user [personally identifiable information, or PII],” in accordance to CloudSEK’s writeup.
APIs – application programming interfaces – are the veins and arteries of the cell ecosystem, enabling applications to connect with many sources and to move information in and out of these apps. It is an “integral” element of how an application operates, CloudSEK reported, which signifies that app developers will need to manage them with child gloves in get to avoid leaking customer data: “Any systematic mishandling of API keys among application builders can cause risk to the app’s business enterprise,” researchers managed.
But like so a great deal of cybersecurity, it is a could-a, really should-a problem: “CloudSEK has noticed that a huge selection of businesses – both substantial and modest – that cater to hundreds of thousands of consumers have cell apps with API keys that are hardcoded in the application packages,” in accordance to CloudSEK scientists Arshit Jain and Sai Ahladini Tripathy. “These keys could be simply found out by malicious hackers or competition who could use them to compromise user info and networks.
They included, “Hardcoded API keys are akin to locking your house but leaving the crucial in an envelope titled ‘do not open.’”
It is Raining APIs
CloudSEK pointed to new significant-profile attacks as illustrations of how API misconfigurations have led to compromised cloud infrastructure, such as the 2019 breach of security seller Imperva. The Imperva breach was induced by the theft of an Amazon Web Products and services (AWS) administrative API key housed in a cloud instance that was remaining exposed to the general public internet.
APIs use a combination of a crucial_id and a vital_solution to make API requests to payment-provider companies. CloudSEK’s investigation uncovered 10 apps that ended up exposing the two halves of the equation.
Scientists focused on 13,000 apps presently uploaded to CloudSEK’s cellular app security research engine BeVigil, about 250 of which – approximately 5 % – have been using the Razorpay API to electrical power money transactions.
But the actuality that CloudSEK only checked out Razorpay transactions to come across those people 10 leaky apps also implies that “the actual quantity of apps exposing API keys could be increased,” CloudSEK instructed. That’s a most likely situation, offered that thousands and thousands of businesses use Razorpay as a payment gateway.
Brain you, there’s no flaw with the Razorpay monetary payment gateway or other these payment integration companies. No, this is all on developers, CloudSEK asserted, the API critical exposures currently being “evidence of how API keys are mishandled by app developers.”
The report pressured that the onus is also on the corporations where by the keys are obtaining bungled: “It is up to unique firms to address the security worries connected with payment gateways, AWS providers, open Firebases, etcetera.”
Beneath is a redacted screen capture listing the bundle names determined in applications submitted to CloudSEK’s BeVigil lookup motor that are working with Razorpay as a payment gateway:

List of package deal names discovered in applications submitted to BeVigil having Razorpay payment integration. Resource: CloudSEK.
A lot of of the apps exposing API keys – apps that include overall health and health, eCommerce, vacation and hospitality, health care and pharma – have far more than a million downloads. The apps are primarily based in India, which is also the place CloudSEK is based. A choice of the influenced applications:
- A person of India’s foremost metal buying and selling firms
- On line grocery application
- Nepalekart (Immediate Recharge to Nepal): Now remediated
- Top rated schooling app in south India
- Gold merchant
- Wellbeing app
A Well-Regarded Issue
As CloudSEK pointed out, the truth that unauthorized access to API keys can allow for menace actors to question sensitive info or obtain critical info is aged news. For case in point, in 2019, North Carolina State University released a report (PDF) describing the discovery of more than 100,000 GitHub repositories whose API or cryptographic keys had leaked.
In fact, more than the weekend, just a several times immediately after CloudSEK revealed its report, penetration tester Abdulrahman-Kamel shared what took place after he made a Python script that searched by archived requests in the Wayback Machine: A challenge that archives the material of internet web pages.
In a nutshell, the penetration tester identified API leakage that would let an attacker entry extra than 10,000 compensated API keys and to use them to get totally free expert services or sensitive details.
Tsk, tsk, remarked Michael Isbitski, specialized evangelist at Salt Security: “In this situation, the impacted web-sites dedicated the worst form of offense where by they relied on API keys submitted as parameters inside of a URL (i.e., a GET request),” he advised Threatpost on Monday. “This implementation technique goes from security greatest observe, wherever no sensitive facts really should be submitted in a URL. Delicate facts in URLs is usually logged and these information can frequently be harvested afterwards by an insider menace or external attacker.”
In April, CloudSEC arrived throughout another leaking boat: Namely, AWS keys. Imperva is significantly from the the only business to misconfigure its AWS API, it uncovered: in simple fact, .5 p.c of mobile apps expose their internal AWS keys, impacting 100 million users’ data. “This highlights a sample of systemic mishandling of API keys among the application builders,” CloudSEK stated very last week.
Beneath is one example CloudSEK presented of an app that contains the hardcoded API essential_id and crucial_magic formula:
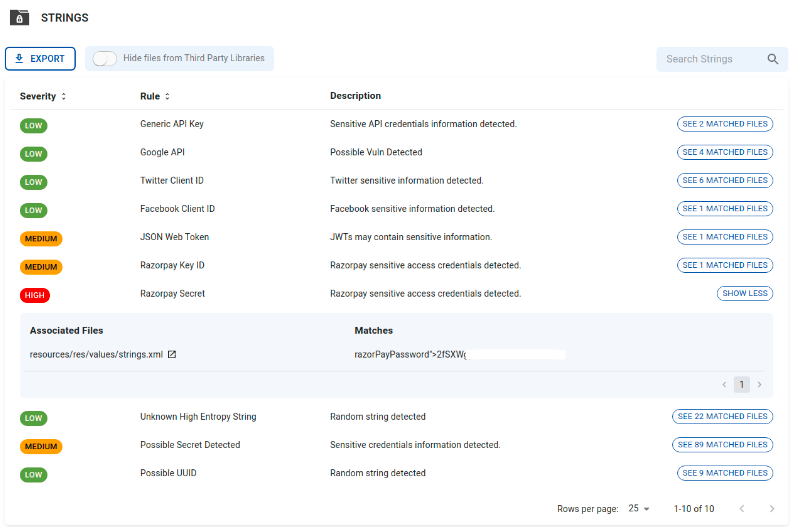
Sample proof of an application that contains the hardcoded API key_id and vital_solution. Supply: CloudSEK.
What Danger Actors Can Do With API Secrets and techniques
CloudSEK pointed out that attackers can extract query payment info via leaked APIs. They can also revoke unauthorized transactions and obtain access to a user’s PII (including phone figures and email addresses), transaction IDs, transaction amounts, get information and refund facts.
With regards to the fraud threat actors can get up to with this sort of delicate facts, they can initiate refunds by working with the compromised translation ID, according to CloudSEK.
“An adversary can make bulk buys and then initiate refunds,” in accordance to the researchers. “Such refunds can also guide to sizeable losses for the corporation. For example: In 1 of the applications we found a transaction for an amount of INR 1,82,813 along with the payment_id. And working with just these two details an adversary could have out a refund.”
They can also offer consumer info on the dark web or to a competitor: “A danger actor can either dump or market the money information and facts, transaction information, user PII on cybercriminal community forums and dark web marketplaces. They could also share the app’s consolidated information, proprietary research, and company financial documents as competitor intelligence to other gamers in the sector,” the CloudSEK researchers wrote.
Threat actors can also wield the users’ PII in social engineering techniques, scams and identity theft.
Hardcoded API Keys Are a No-No
Salt Security’s Isbitski mentioned that API keys are the equal of static passwords that businesses usually use as a sole signifies of authentication, with IT groups failing to rotate them often plenty of, “if at all,” even though engineering teams “often depend on API keys as a suggests of process integration or automation.”
Attackers know this whole effectively. They know that API keys can generally be discovered embedded inside of cell applications that are simple to reverse-engineer, Isbitski claimed. “API keys are generally hardcoded in just application source code or infrastructure code, both of which are typically stashed in just cloud-hosted code repositories like GitHub or common-purpose cloud storage like AWS S3,” he described. “Obtaining an API crucial is the equal of obtaining a working credential. Attackers craft requests to API endpoints working with harvested API keys to acquire entry to information or functionality.”
API security ideal procedures including disallowing the embedding of API keys or tricks in purposes or code, provided how simply they can be harvested by attackers.
“API keys by itself are not meant as a usually means of authentication,” he continued. “API keys have to be paired with other authentication and authorization material to present potent access control” – an issue that Salt Security tackled in its not long ago revealed API Security Ideal Methods.
Attackers often steal credentials or hijack authenticated classes through a selection of procedures which includes social engineering, phishing, individual-in-the-center attacks and by reverse engineering code, he iterated. Consequently, a different factor of API security very best methods is sturdy access manage, as very well as runtime conduct analysis that can detect and cease activities when authentication materials is compromised and, in transform, made use of to abuse APIs.
Rule #1 of Linux Security: No cybersecurity option is feasible if you do not have the basic principles down. Sign up for Threatpost and Linux security execs at Uptycs for a Are living roundtable on the 4 Golden Procedures of Linux Security. Your prime takeaway will be a Linux roadmap to getting the principles proper! Register NOW and be a part of the Reside celebration on Sept. 29 at Noon EST. Signing up for Threatpost is Uptycs’ Ben Montour and Rishi Kant who will spell out Linux security very best tactics and take your most urgent concerns in authentic time.
Some elements of this article are sourced from:
threatpost.com


 Data of 106 Million Visitors to Thailand Breached
Data of 106 Million Visitors to Thailand Breached