Scientists uncovered flaws most of the ‘popular’ PDF apps tested.
Accredited transportable document structure (PDF) documents are applied to securely indication agreements amongst two parties while trying to keep the contents’ integrity shielded, but a new report uncovered the security protections on most licensed PDF applications have been insufficient and left companies exposed to a variety of attacks.
Scientists from Ruhr College Bochum stated qualified PDFs use two specific signatures to authenticate the document, an Approval signature and a Certification signature. Certification signatures are the additional adaptable and designed to handle sophisticated agreements amongst many functions and let some variations to the document inside a established of parameters while however protecting its validity.
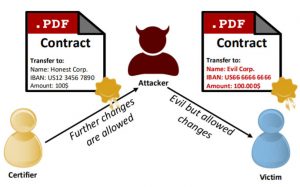
Unsurprisingly, Licensed signatures are the place the workforce observed vulnerabilities to two specific novel attacks they dubbed, “Evil Annotation” (EAA) and “Sneaky Signature” (SSA). Equally make it possible for an attacker to overlay malicious written content (PDF) on major of the certified details without the need of displaying any indications it was altered.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Novel Accredited PDF Attacks
EAAs display screen malicious written content in the document’s annotations and then sends it on with its electronic signature intact. SSAs insert malicious articles in excess of reputable information in the PDF alone.
The crew reported the results of its evaluation of the 26 most popular PDF programs had been “alarming.”
“In only 2 cases, we could not obtain a vulnerability 15 viewers had been vulnerable to EAA, 8 to SSA, like Adobe, Foxit, and LibreOffice,” the report stated. “We also analyzed the typical-compliant implementation of PDF certification purposes and found issues in 11 of them.”
Adobe experienced an supplemental flaw that authorized accredited paperwork to execute JavaScript code, opening these consumers to code in injection attacks.
 “For instance, a significant-stage JavaScript can call an arbitrary URL with out person confirmation to deanonymize a consumer. Our research reveals that these kinds of code is also executed if it is included as an permitted incremental update. We are the initially to reveal that this habits lets attackers to directly embed malicious code into a certified doc.
“For instance, a significant-stage JavaScript can call an arbitrary URL with out person confirmation to deanonymize a consumer. Our research reveals that these kinds of code is also executed if it is included as an permitted incremental update. We are the initially to reveal that this habits lets attackers to directly embed malicious code into a certified doc.
The group mentioned it disclosed their results to the proper suppliers and presented a complete vulnerability report, such as exploits, to CERT-Bund (BSI). The report also lists the specific qualified PDF security flaws observed in each and every software.
“Adobe, Foxit, and LibreOffice responded immediately and delivered patches for late 2020 (CVE-2020-35931) or early 2021 (CVE2021-28545, CVE-2021-28546),” the report stated. “Adobe fixed the code injection vulnerability in early Nov. 2020 inside of a patch outside the frequent update cycle (CVE-2020-24432). At the moment, we participate in the standardization process by way of the German Nationwide Firm for Standardization (DIN) and the Worldwide Group for Standardization (ISO) to deal with the claimed attacks in the subsequent PDF specification.”
Halting Certified PDF Attacks
To fend off Evil Annotation Attacks, the researchers endorse admins prohibit a few particularly risky annotations that make it possible for textual content or visuals to be additional to a certified PDF, “FreeText, Stamp and Redact.”
Sneaky Signatures can be blocked by reducing permissions, but that is not a promise SSAs will not get by way of. Described signature fields offer an added layer of safety, the report said.
“Signature fields have to be established up at described locations in the PDF document in advance of the document is qualified,” the report spelled out. “A subsequent addition of signature fields need to be penalized with an invalid certification standing. If not, it can always be utilized to add textual content or images provided in the signature at any place.”
Adobe JavaScript code injections are trickier given that in most circumstances the execution starts the moment the document is opened. “The only necessity is that the sufferer fully trusts the certificate used to certify the PDF doc,” the report stated.
Earlier this thirty day period Adobe Acrobat issued a patch for a zero-working day bug concentrating on Windows buyers. Just times later, scientists at Microsoft Security Intelligence (MSI) located PDFs were getting utilized by attackers to deliver StrRAT Java-based mostly distant entry software (RAT) applied to steal credentials, log keystrokes and just take distant manage more than infected systems.
The flexibility available by Certified signatures presents a substantial, perhaps catastrophic, security risk for many corporations and the report urges PDF applications to operate rapidly to come up with vast-scale fixes.
“The research community has struggled with related challenges on other knowledge formats, these kinds of as XML or Email, without having getting a satisfying resolution so much,” they said. “In the situation of PDF, the specification must be current to address these issues.”
Be a part of Threatpost for “A Wander On The Dark Facet: A Pipeline Cyber Disaster Simulation”– a Dwell interactive demo on Wed, June 9 at 2:00 PM EDT. Sponsored by Immersive Labs, obtain out no matter if you have the resources and skills to reduce a Colonial Pipeline-model attack on your group. Issues and Dwell viewers participation inspired. Sign up for the dialogue and Register HERE for absolutely free.
Some sections of this short article are sourced from:
threatpost.com


 VMware Sounds Ransomware Alarm Over Critical Severity Bug
VMware Sounds Ransomware Alarm Over Critical Severity Bug